The Wake-Up Name We All Felt
On October 20, 2025, organizations throughout industries, from banking to streaming, logistics to healthcare, skilled widespread service degradation when AWS’s US-EAST-1 area suffered a major outage. Because the ThousandEyes evaluation revealed, the disruption stemmed from failures inside AWS’s inside networking and DNS decision methods that rippled via dependent providers worldwide.
The basis trigger, a latent race situation in DynamoDB’s DNS administration system, triggered cascading failures all through interconnected cloud providers. However right here’s what separated groups that would reply successfully from these flying blind: actionable, multilayer visibility.
When the outage started at 6:49 a.m. UTC, refined monitoring instantly revealed 292 affected interfaces throughout Amazon’s community, pinpointing Ashburn, Virginia because the epicenter. Extra critically, as situations developed, from preliminary packet loss to application-layer timeouts to HTTP 503 errors, complete visibility distinguished between community points and utility issues. Whereas floor metrics confirmed packet loss clearing by 7:55 a.m. UTC, deeper visibility revealed a special story: edge methods have been alive however overwhelmed. ThousandEyes brokers throughout 40 vantage factors confirmed 480 Slack servers affected with timeouts and 5XX codes, but packet loss and latency remained regular, proving this was an utility problem, not a community downside.
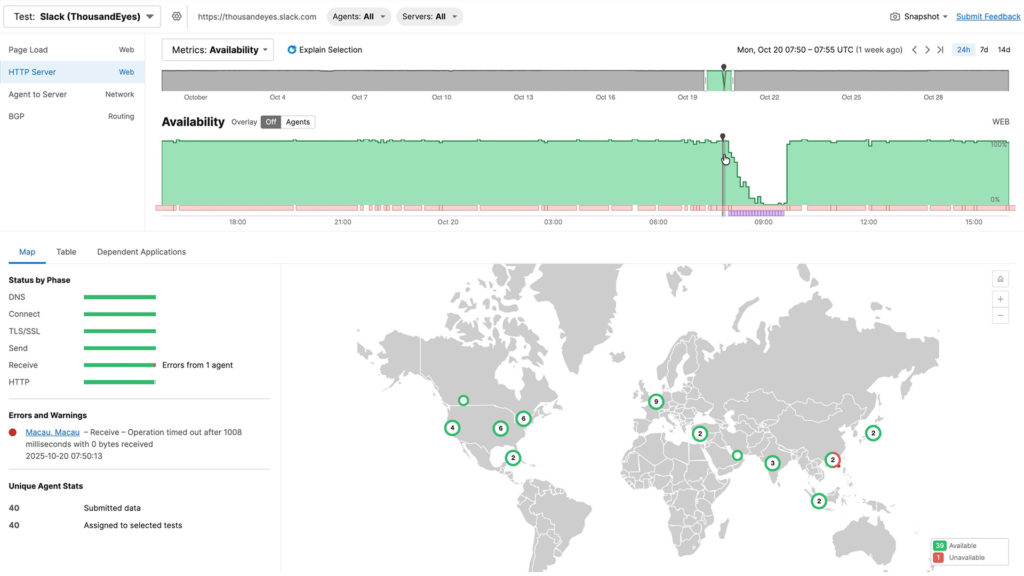
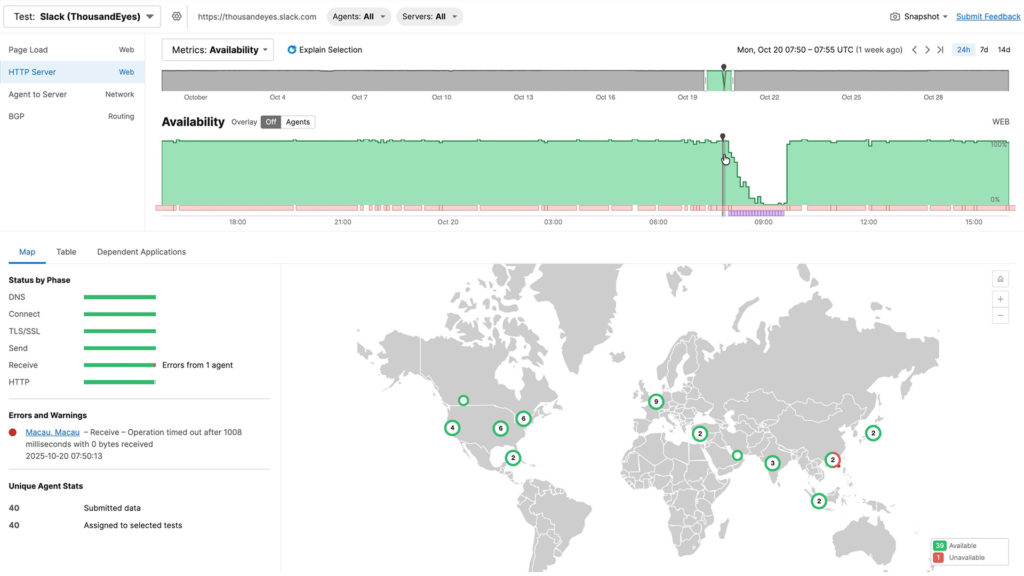
Determine 1. Altering nature of signs impacting app.slack.com throughout the AWS outage
Endpoint information revealed app.slack.com expertise scores of simply 45% with 13-second redirects, whereas native community high quality remained good at 100%. With out this multilayer perception, groups would waste valuable incident time investigating the mistaken layer of the stack.
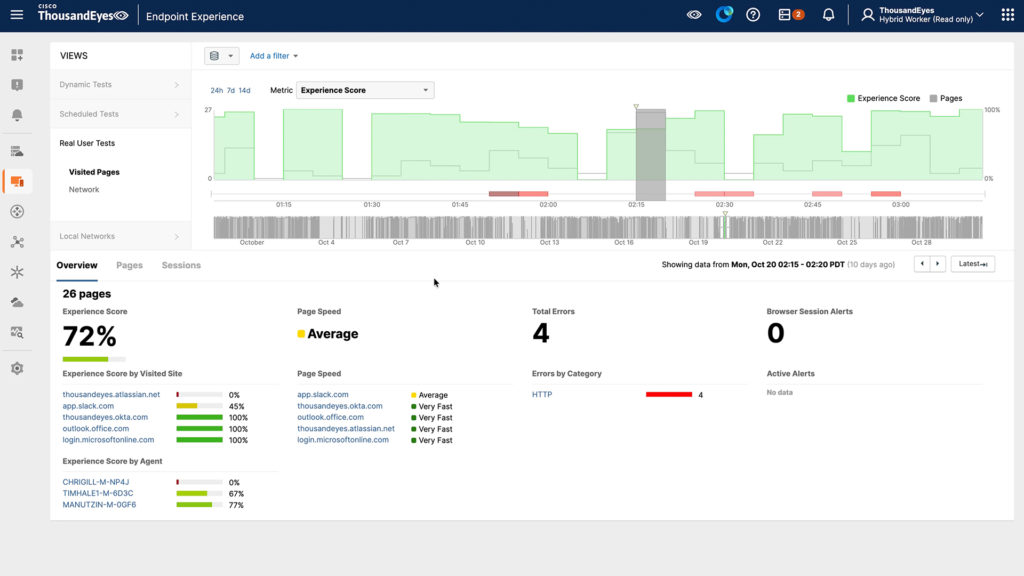
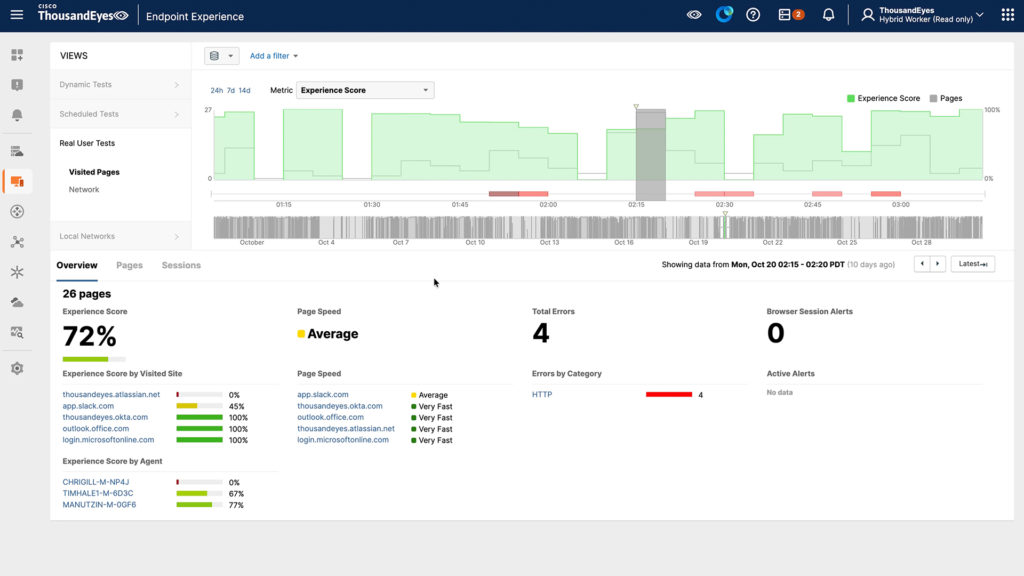
Determine 2. app.slack.com noticed for an finish person
The restoration section highlighted why complete visibility issues past preliminary detection. Even after AWS restored DNS performance round 9:05 a.m. UTC, the outage continued for hours as cascading failures rippled via dependent methods, EC2 couldn’t preserve state, inflicting new server launches to fail for 11 extra hours, whereas providers like Redshift waited to recuperate and clear large backlogs.
Understanding this cascading sample prevented groups from repeatedly trying the identical fixes, as an alternative recognizing they have been in a restoration section the place every dependent system wanted time to stabilize. This outage demonstrated three crucial classes: single factors of failure conceal in even essentially the most redundant architectures (DNS, BGP), preliminary issues create long-tail impacts that persist after the primary repair, and most significantly, multilayer visibility is nonnegotiable.
In in the present day’s warfare rooms, the query isn’t whether or not you’ve monitoring, it’s whether or not your visibility is complete sufficient to shortly reply the place the issue is going on (community, utility, or endpoint), what the scope of influence is, why it’s occurring (root trigger vs. signs), and whether or not situations are enhancing or degrading. Floor-level monitoring tells you one thing is mistaken. Solely deep, actionable visibility tells you what to do about it.
The occasion was a stark reminder of how interconnected and interdependent trendy digital ecosystems have develop into. Functions in the present day are powered by a dense internet of microservices, APIs, databases, and management planes, lots of which run atop the identical cloud infrastructure. What seems as a single service outage usually masks a much more intricate failure of interdependent parts, revealing how invisible dependencies can shortly flip native disruptions into world influence.
Seeing What Issues: Assurance because the New Belief Cloth
At Cisco, we view Assurance because the connective tissue of digital resilience, working in live performance with Observability and Safety to present organizations the perception, context, and confidence to function at machine pace. Assurance transforms information into understanding, bridging what’s noticed with what’s trusted throughout each area, owned and unowned. This “belief material” connects networks, clouds, and functions right into a coherent image of well being, efficiency, and interdependency.
Visibility alone is not ample. In the present day’s distributed architectures generate an enormous quantity of telemetry, community information, logs, traces, and occasions, however with out correlation and context, that information provides noise as an alternative of readability. Assurance is what interprets complexity into confidence by connecting each sign throughout layers right into a single operational reality.
Throughout incidents just like the October 20th outage, platforms corresponding to Cisco ThousandEyes play a pivotal position by offering real-time, exterior visibility into how cloud providers are behaving and the way customers are affected. As a substitute of ready for standing updates or piecing collectively logs, organizations can straight observe the place failures happen and what their real-world influence is.
Key capabilities that allow this embody:
- International vantage level monitoring: Cisco ThousandEyes detects efficiency and reachability points from the skin in, revealing whether or not degradation stems out of your community, your supplier, or someplace in between.
- Community path visualization: It pinpoints the place packets drop, the place latency spikes, and whether or not routing anomalies originate in transit or throughout the cloud supplier’s boundary.
- Software-layer synthetics: By testing APIs, SaaS functions, and DNS endpoints, groups can quantify person influence even when core methods seem “up.”
- Cloud dependency and topology mapping: Cisco ThousandEyes exposes the hidden service relationships that usually go unnoticed till they fail.
- Historic replay and forensics: After the occasion, groups can analyze precisely when, the place, and the way degradation unfolded, remodeling chaos into actionable perception for structure and course of enhancements.
When built-in throughout networking, observability, and AI operations, Assurance turns into an orchestration layer. It permits groups to mannequin interdependencies, validate automations, and coordinate remediation throughout a number of domains, from the information heart to the cloud edge.
Collectively, these capabilities flip visibility into confidence, serving to organizations isolate root causes, talk clearly, and restore service quicker.
Find out how to Put together for the Subsequent “Inevitable” Outage
If the previous few years have proven something, it’s that large-scale cloud disruptions will not be uncommon; they’re an operational certainty. The distinction between chaos and management lies in preparation, and in having the proper visibility and administration basis earlier than disaster strikes.
Listed here are a number of sensible steps each enterprise can take now:
- Map each dependency, particularly the hidden ones.
Catalogue not solely your direct cloud providers but in addition the management airplane methods (DNS, IAM, container registries, monitoring APIs) they depend on. This helps expose “shared fates” throughout workloads that seem impartial. - Take a look at your failover logic beneath stress.
Tabletop and reside simulation workout routines usually reveal that failovers don’t behave as cleanly as meant. Validate synchronization, session persistence, and DNS propagation in managed situations earlier than actual crises hit. - Instrument from the skin in.
Inner telemetry and supplier dashboards inform solely a part of the story. Exterior, internet-scale monitoring ensures you understand how your providers seem to actual customers throughout geographies and ISPs. - Design for sleek degradation, not perfection.
True resilience is about sustaining partial service quite than going darkish. Construct functions that may briefly shed non-critical options whereas preserving core transactions. - Combine assurance into incident responses.
Make exterior visibility platforms a part of your playbook from the primary alert to ultimate restoration validation. This eliminates guesswork and accelerates government communication throughout crises. - Revisit your governance and funding assumptions.
Use incidents like this one to quantify your publicity: what number of workloads depend upon a single supplier area? What’s the potential income influence of a disruption? Then use these findings to tell spending on assurance, observability, and redundancy.
The aim isn’t to remove complexity; it’s to simplify it. Assurance platforms assist groups repeatedly validate architectures, monitor dynamic dependencies, and make assured, data-driven choices amid uncertainty.
Resilience at Machine Velocity
The AWS outage underscored that our digital world now operates at machine pace, however belief should maintain tempo. With out the power to validate what’s actually occurring throughout clouds and networks, automation can act blindly, worsening the influence of an already fragile occasion.
That’s why the Cisco strategy to Assurance as a belief material pairs machine pace with machine belief, empowering organizations to detect, resolve, and act with confidence. By making complexity observable and actionable, Assurance permits groups to automate safely, recuperate intelligently, and adapt repeatedly.
Outages will proceed to occur. However with the proper visibility, intelligence, and assurance capabilities in place, their penalties don’t need to outline your corporation.
Let’s construct digital operations that aren’t solely quick, however trusted, clear, and prepared for no matter comes subsequent.

