App builders can decrease fraud through the use of App Attest and DeviceCheck, two instruments offered by Apple. This is easy methods to use them to stop unauthorized modifications to your app, and to stop customers from illegitimately buying premium content material.
As an app developer, there are just a few methods which you could earn a living out of your creations. Nevertheless, not everybody could also be prepared to pay, however nonetheless wish to entry some paid premium options.
Builders search to keep away from this type of habits. That is the place Apple’s App Attest and DeviceCheck step in.
Through the use of Apple’s DeviceCheck framework, you may guarantee solely licensed customers can entry premium content material and promotions.
DeviceCheck
Apple supplies the DeviceCheck framework to assist your app scale back tried fraudulent use of premium app options.
DeviceCheck helps mitigate fraud on promotional choices in apps.
For instance, in case your app provides promotions or premium content material, some customers could attempt to abuse the options to get a number of free gadgets. They may do that by uninstalling after which re-installing your app.
The DeviceCheck framework permits your app to see if a specific {hardware} system has already acquired a promotional supply.
These checks are tied to the Safe Enclave in every Apple system. They’re mixed with an Apple Account and a non-public cryptographic key to make sure authorization.
- Two system state bits saved by Apple together with a timestamp
- Per system, per developer
- Persistent throughout {hardware} system resets
The 2 bits saved by Apple tie every Apple developer to a identified state for any beforehand registered promotions per app. Together with the timestamp you should use the bits any manner you want to ensure that your app to find out promotion standing.
DeviceCheck retains observe of units on a per-device foundation, per app developer.
The DeviceCheck state is saved throughout system resets, ought to the Apple system be utterly reset to manufacturing facility situation.
These checks can be utilized by your app to see if a given promotion was beforehand utilized by any app by any Apple Account on any Apple system.
App Attest
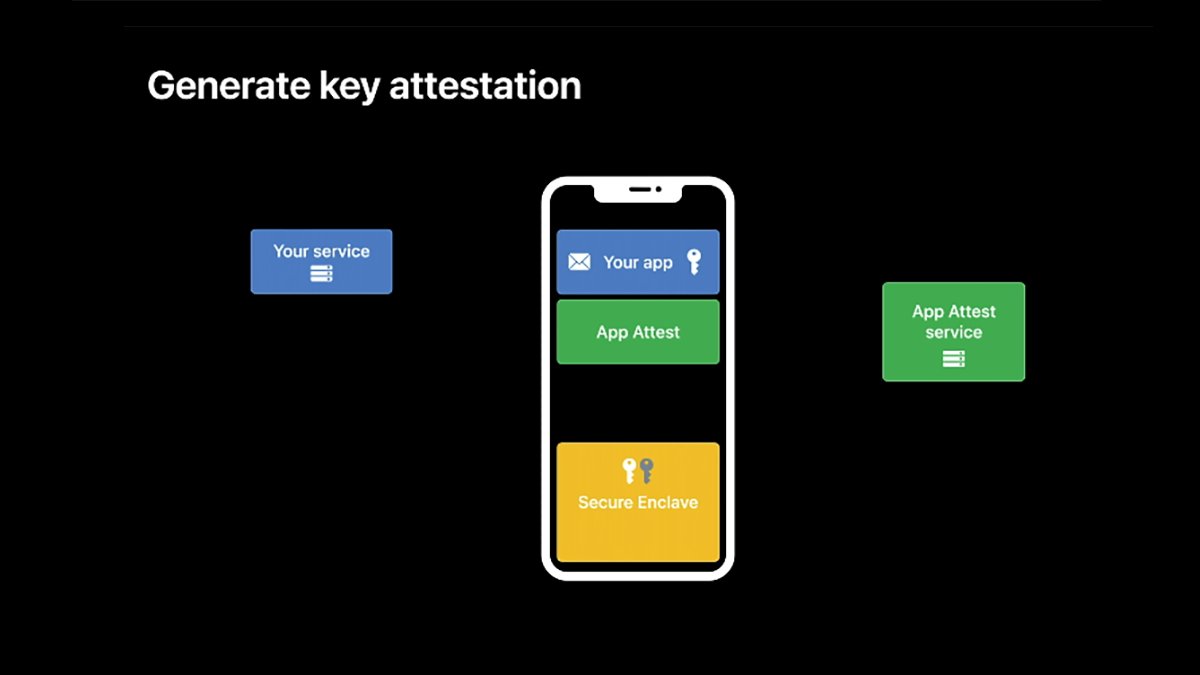
App Attest can also be a part of the DeviceCheck.framework and means that you can observe any given service your app options with a view to decide if that service is one your app acknowledges.
With the intention to use App Attest you have to both a server or cloud-based service to obtain hardware-based tokens from the person’s system, together with an App Attest request. Your server should then ahead these app requests on to an Apple App Attest server for verification.
If the Apple server returns that the app and repair are legitimate, your server informs the sending system that the request is legitimate.
Since every request is tied to particular system {hardware} information, requests cannot be solid or copied for different units.
App Attest additionally prevents illegitimate copies of premium app or service options from being copied from one system to a different.
Three simple items
App Attest supplies three key items of information your app can use to confirm {that a} request got here from an genuine, licensed Apple system:
- Real Apple system
- Genuine software id
- Trustable payload
Checking for a real Apple system means that you can confirm that the app and premium content material are, the truth is, being run on an actual Apple system.
Genuine software id makes positive that the app which is making the request is your app and that it’s a reliable copy. One which has been downloaded from the App Retailer.
Trustable payloads will be checked to verify the premium characteristic or promotional content material is permitted, has been bought, and has not been tampered with.
Through the use of these three items of information, your app can be sure that the content material needs to be obtainable to the person. This prevents hackers and jail-breakers from trying to obtain or reuse premium content material paid for and licensed on one other Apple system.
The real system verify is completed by a an examination of a safe key pair on the system, which is utilized by the Safe Enclave. It is mixed with an App Attest request from the system which is generated utilizing the legitimate key pair.
Safe key pairs are half of what’s known as Public Key Infrastructure (PKI) which makes use of encryption to create safe keys and sends them over a community.
Through the use of safe keys and digital signatures, an app and system can affirm a request originates from who it claims to.
PKI is extraordinarily safe and even essentially the most performant supercomputers on the planet require years to crack it.
When your app makes an App Attest request, it could actually use the safe keys to take action, which may then be verified by the server. Every safe secret is distinctive per set up and will not be synced or copied throughout units.
An encoded copy of every requesting app’s Bundle ID can also be despatched with every request for verification.
Including App Attest to your app
So as to add App Attest to your app in Xcode, you should first embrace the DeviceCheck.framework within the Construct Information tab in every undertaking goal’s frameworks pane.
With the intention to use App Attest in your app, the app have to be working on a tool with a Safe Enclave. Due to this fact you should at all times verify for the power to make use of App Attest in your app earlier than you really accomplish that.
There are additionally three components to including App Attest to your app:
- Producing an AppAttest key
- Verifying keys
- Producing and verifying assertions
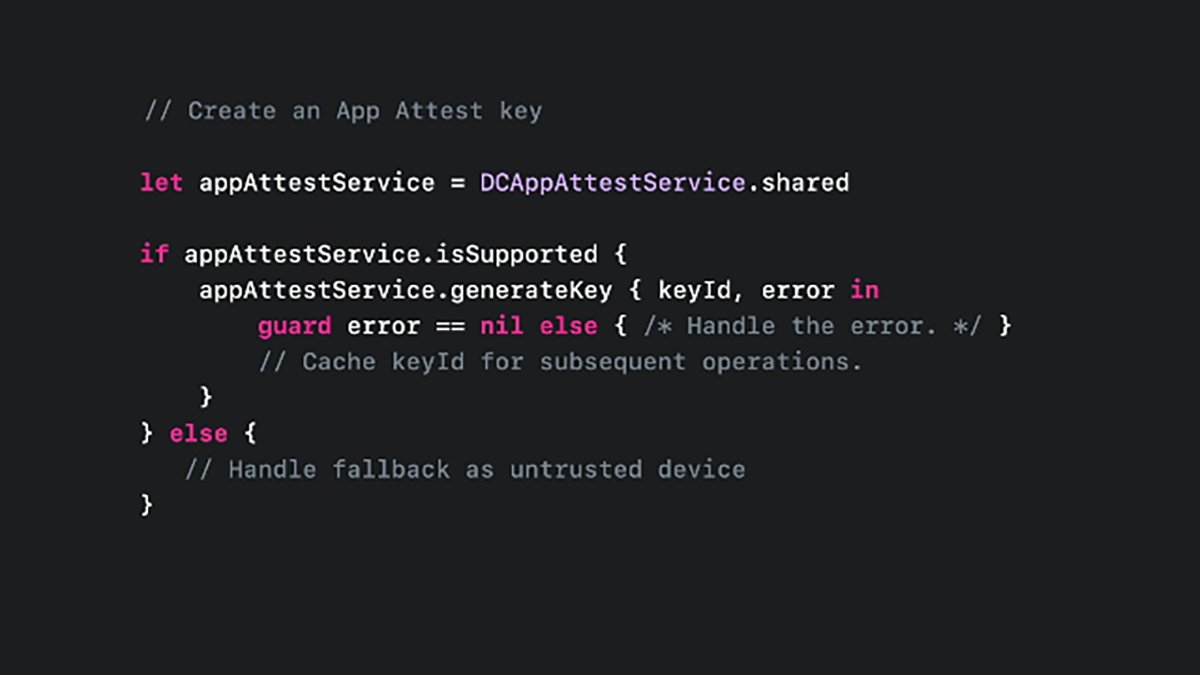
To create an AppAttest key in your app’s code, use the .shared property on the DCAppAttestService class object like this:
let appAttestService = DCAppAttestService.shared
This creates an area variable named appAttestService from the .shared property and shops a replica of the shared service object.
After getting an occasion of the .shared property, you should use it to create a key:
Within the above code, you first get a shared occasion of the DCAppAttestService class. Then you definately verify its .isSupported property to verify AppAttest is offered on this system, after which generate a key with the .generatekey technique.
If .generatekey returns an error, you verify for it and deal with it, else the secret’s returned in keyId.
After getting the important thing, you may then retailer it away for later use – most probably in an object you outlined and created beforehand.
The DeviceCheck.framework additionally helps Goal-C interfaces in case you are nonetheless utilizing that language as an alternative of Swift.
If the .isSupported property returns NO or the important thing returns nil you may’t use AppAttest in your app.
Bear in mind there are some circumstances through which code should return NO for the .isSupported. Even when the system does have a Safe Enclave in it (normally if the code is named from an app extension).
Your app have to be ready to deal with these circumstances as properly. In these conditions assume the caller is untrusted, then devise your individual code logic primarily based on a set of threat evaluation guidelines to find out if the premium options needs to be allowed.
This strategy is a second-best validation when the .isSupported property returns NO.
Validate key
Assuming you do have a sound key from the above code, the following step is to validate or attest the important thing.
To do that your app might want to create a one-time server problem. This problem is designed to attest the important thing you generated with a problem out of your server, which validates the important thing together with person account information.
You have to to additionally devise server-side code to do that for every key attest prevalence.
Key attestation supplies a further stage of safety by stopping man-in-the-middle and replay assaults.
Step one on this course of is to generate a key attestation. You utilize the identical app attest server object as above, however with the .attestKey technique.
Utilizing this technique, you go the unique keyID, a shopper information hash, an attestationObject, and an elective error variable which the .attestKey technique takes as enter.
On return, the attestationObject can be utilized for the server problem.
The aim of the .attestKey technique is to make use of the system’s non-public key to create an opaque {hardware} attestation request. One tied to the important thing and this particular system.
This {hardware} attestation is then despatched to an Apple attestation server for {hardware} verification. As soon as verified, the Apple server will return an nameless attestation object to your app.
Solely Apple’s server is aware of easy methods to confirm the system at a {hardware} stage primarily based on the data despatched to it, thus making it very troublesome for hackers to intercept the request and return a false constructive that permits the premium options.
As soon as the app receives the response from Apple and makes positive it’s legitimate, the app ought to then ship the response together with any customized payload to your server for ultimate verification.
This relatively advanced course of, mixed with Apple’s {hardware} verification and a non-public key, makes it very troublesome for anybody to hack your premium options and allow unauthorized content material.
There are 4 extra sections within the DeviceCheck framework documentation that you will wish to try:
- Accessing and modifying per-device information
- Assessing fraud threat
- Establishing your app’s integrity
- Validating apps that connect with your server
Dealing with errors
Within the above code, we noticed a few of Apple’s DeviceCheck APIs return an elective error code.
Your app ought to deal with these codes and inform the person if any errors happen.
Take a look at the documentation for the DCDevice and DCError courses within the DeviceCheck framework.
You can even get hold of person displayable error codes from any DeviceCheck framework API which returns a DCError by getting the worth of its .Code property. That is outlined as an enum (a quantity) which will be mapped to a set of predefined Apple error codes.
Utilizing a normal Swift/C case assertion, you may then map an error code consequence to a user-displayable string your app reveals to the person.
At the moment, there are 5 predefined DCError codes set by Apple:
- featureUnsupported
- invalidInput
- invalidKey
- serverUnavailable
- unknownSystemFailure
featureUnsupported implies that some or all the DeviceCheck API is not obtainable. invalidKey means the important thing you tried to make use of failed.
On any error return from an Apple API or the important thing attestation, your app ought to show an applicable localized textual content string to the person, informing them why it did not work.
You can even verify the worldwide variable DCErrorDomain after errors to find out the area of the final occurring error.
Consider error domains as classes errors are organized into. Through the use of the DCErrorDomain string, you can provide customers extra helpful information on what kind of error occurred.
DeviceCheck and AppAttest are welcome additions to Apple app growth. Through the use of them in your app, you may safe your premium options and income with out an excessive amount of additional work.