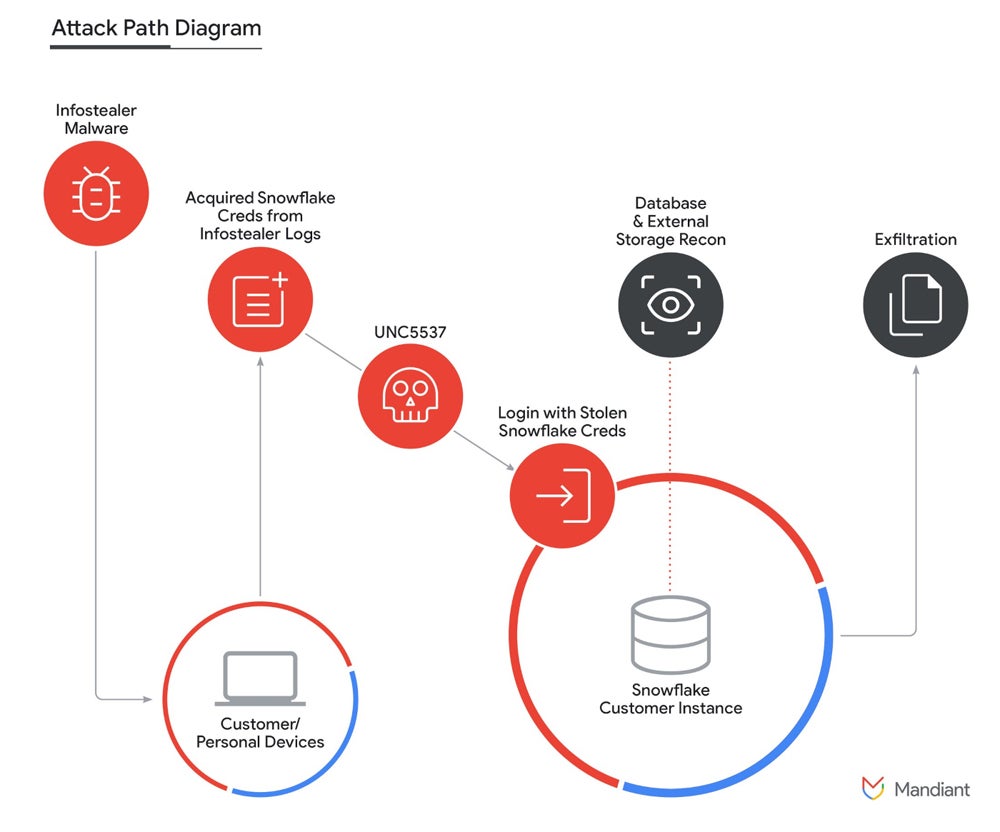
A brand new report from Mandiant, a part of Google Cloud, reveals {that a} financially motivated menace actor named UNC5537 collected and exfiltrated knowledge from about 165 organizations’ Snowflake buyer cases. Snowflake is a cloud knowledge platform used for storing and analyzing giant volumes of knowledge.
The menace actor managed to get entry to those knowledge by triggering credentials that have been beforehand stolen by infostealer malware or bought from different cybercriminals.
In line with Mandiant, the menace actor UNC5537 advertises sufferer knowledge on the market on cybercrime boards and makes an attempt to extort most of the victims. When the info is bought, any cybercriminal would possibly purchase this data for various functions akin to cyber espionage, aggressive intelligence or extra financially-oriented fraud.
How have been some Snowflake customers focused for this knowledge theft and extortion?
A joint assertion offered by Snowflake, Mandiant and cybersecurity firm CrowdStrike signifies there is no such thing as a proof suggesting the fraudulent exercise could be attributable to a vulnerability, misconfiguration or breach of Snowflake’s platform. There’s additionally no proof the exercise would have been attributable to compromised credentials from present or previous Snowflake staff.
As an alternative, proof exhibits the attackers obtained credentials from a number of infostealer malware campaigns that contaminated non-Snowflake owned programs. The menace actor then gained entry to the affected accounts, which allowed the exfiltration of a major quantity of buyer knowledge from the respective Snowflake buyer cases.
Mandiant researchers said nearly all of the credentials utilized by UNC5537 have been accessible from historic infostealer malware; a few of these credentials date again to November 2020 however have been nonetheless usable. Completely different infostealer malware households have been chargeable for the credentials theft — probably the most used ones being Vidar, Risepro, Redline, Racoon Stealer, Lumma and Metastealer.
In line with Mandiant and Snowflake, at the very least 79.7% of the accounts leveraged by the menace actor had prior credential publicity.
Mandiant additionally reported the preliminary compromise of infostealer malware occurred on contractor programs that have been additionally used for private actions, together with gaming and downloads of pirated software program, which is a robust vector for spreading infostealers.
How did UNC5537 receive the stolen credentials?
As reported, the menace actor obtained credentials from a wide range of infostealer malware, but UNC5537 additionally leveraged credentials that have been beforehand bought.
Whereas no extra data is offered by Mandiant, it’s affordable to suppose these credentials have been purchased in a single or a number of cybercriminal underground marketplaces on to so-called Preliminary Entry Brokers, that are a class of cybercriminals who promote stolen company entry to different fraudsters.
As written by Mandiant in its report, “the underground infostealer financial system can also be extraordinarily strong, and huge lists of stolen credentials exist each without cost and for buy inside and out of doors of the darkish internet.” Mandiant additionally reported that, in 2023, 10% of total intrusions started with stolen credentials, representing the fourth most notable preliminary intrusion vector.
What was the preliminary entry and knowledge exfiltration strategies on this Snowflake assault?
On this assault marketing campaign, the preliminary entry to Snowflake buyer cases usually occurred by way of the native person interface accessible from the online (Snowflake SnowSight) or from the command-line interface instrument offered by Snowflake (SnowSQL). A further attacker-named instrument known as “rapeflake” and tracked below FROSTBITE by Mandiant has been used to carry out reconnaissance towards Snowflake cases.
FROSTBITE exists in at the very least two variations: one utilizing .NET to work together with the Snowflake .NET driver, and one model utilizing Java to work together with the Snowflake JDBC driver. The instrument permits the attackers to carry out SQL actions akin to itemizing customers, present roles, present IP addresses, session IDs and organizations’ names.
A public instrument for managing databases, DBeaver Final, has additionally been utilized by the menace actor to run queries on the Snowflake cases.
Utilizing SQL queries, the menace actor was capable of exfiltrate data from databases. As soon as attention-grabbing knowledge was discovered, it was compressed as GZIP utilizing the “COPY INTO” command to cut back the dimensions of the info to be exfiltrated.
The attacker primarily used Mullvad and Personal Web Entry VPN companies to entry the victims’ Snowflake cases. A moldovan VPS supplier, ALEXHOST SRL, was additionally used for knowledge exfiltration. The menace actor saved sufferer knowledge on a number of worldwide VPS suppliers, in addition to on the cloud storage supplier MEGA.
What organizations are in danger?
The assault marketing campaign seems to be a focused marketing campaign aimed toward Snowflake customers with single-factor authentication. All customers with multifactor authentication are secure from this assault marketing campaign and weren’t focused.
As well as, the impacted Snowflake buyer cases didn’t have enable lists in place to solely enable connections from trusted areas.
Ideas from Snowflake on learn how to defend what you are promoting from this cybersecurity menace
Snowflake revealed data on detecting and stopping unauthorized person entry.
The corporate offered an inventory of just about 300 suspicious IP addresses utilized by the menace actor and shared a question to establish entry from the suspect IP addresses. The corporate additionally offered a question to establish the utilization of the “rapeflake” and “DBeaver Final” instruments. Any person account returning outcomes from these queries should instantly be disabled.
Safety hardening is extremely advisable by Snowflake:
- Implement MFA for customers.
- Arrange account-level and user-level community insurance policies for extremely credentialed customers/companies accounts.
- Evaluate account parameters to limit knowledge exportation from Snowflake accounts.
- Monitor Snowflake accounts for unauthorized privilege escalation or configuration adjustments and examine any of these occasions.
Moreover, it’s strongly advisable to have all software program and working programs updated and patched to keep away from being compromised by a typical vulnerability, which could result in credentials leak.
Safety options must be deployed on each endpoint to stop infostealer an infection.
Additionally it is suggested to boost consciousness on laptop safety and prepare employees to detect and report suspicious cybersecurity occasions.
Disclosure: I work for Development Micro, however the views expressed on this article are mine.

