Final November, we launched the Safe Future Initiative (SFI) to arrange for the growing scale and excessive stakes of cyberattacks. SFI brings collectively each a part of Microsoft to advance cybersecurity safety throughout our firm and merchandise.
Since then, the menace panorama has continued to quickly evolve, and we now have discovered lots. The current findings by the Division of Homeland Safety’s Cyber Security Overview Board (CSRB) concerning the Storm-0558 cyberattack from final July, and the Midnight Blizzard assault we reported in January, underscore the severity of the threats going through our firm and our clients.
Microsoft performs a central function on the planet’s digital ecosystem, and this comes with a vital duty to earn and keep belief. We should and can do extra.
We’re making safety our high precedence at Microsoft, above all else—over all different options. We’re increasing the scope of SFI, integrating the current suggestions from the CSRB in addition to our learnings from Midnight Blizzard to make sure that our cybersecurity strategy stays strong and adaptive to the evolving menace panorama.
We’ll mobilize the expanded SFI pillars and targets throughout Microsoft and this will likely be a dimension in our hiring choices. As well as, we are going to instill accountability by basing a part of the compensation of the corporate’s Senior Management Workforce on our progress in assembly our safety plans and milestones.
Beneath are particulars to display the seriousness of our work and dedication.
Enlargement of SFI strategy and scope
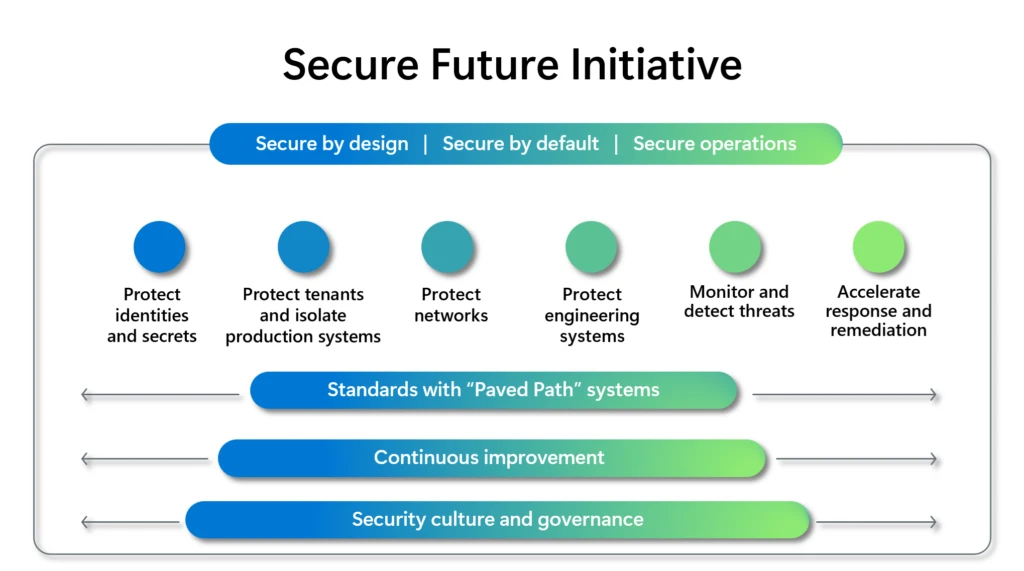
We’ve got advanced our safety strategy, and going ahead our work will likely be guided by the next three safety rules:
- Safe by design: Safety comes first when designing any services or products.
- Safe by default: Safety protections are enabled and enforced by default, require no additional effort, and aren’t elective.
- Safe operations: Safety controls and monitoring will constantly be improved to fulfill present and future threats.
We’re additional increasing our targets and actions aligned to six prioritized safety pillars and offering visibility into the main points of our execution:
1. Defend identities and secrets and techniques
Cut back the danger of unauthorized entry by implementing and imposing best-in-class requirements throughout all id and secrets and techniques infrastructure, and consumer and software authentication and authorization. As a part of this, we’re taking the next actions:
- Defend id infrastructure signing and platform keys with speedy and automated rotation with {hardware} storage and safety (for instance, {hardware} safety module (HSM) and confidential compute).
- Strengthen id requirements and drive their adoption by use of normal SDKs throughout 100% of functions.
- Guarantee 100% of consumer accounts are protected with securely managed, phishing-resistant multifactor authentication.
- Guarantee 100% of functions are protected with system-managed credentials (for instance, Managed Id and Managed Certificates).
- Guarantee 100% of id tokens are protected with stateful and sturdy validation.
- Undertake extra fine-grained partitioning of id signing keys and platform keys.
- Guarantee id and public key infrastructure (PKI) techniques are prepared for a post-quantum cryptography world.
2. Defend tenants and isolate manufacturing techniques
Defend all Microsoft tenants and manufacturing environments utilizing constant, best-in-class safety practices and strict isolation to attenuate breadth of impression. As a part of this, we’re taking the next actions:
- Keep the safety posture and industrial relationships of tenants by eradicating all unused, aged, or legacy techniques.
- Defend 100% of Microsoft, acquired, and employee-created tenants, commerce accounts, and tenant sources to the safety finest observe baselines.
- Handle 100% of Microsoft Entra ID functions to a excessive, constant safety bar.
- Remove 100% of id lateral motion pivots between tenants, environments, and clouds.
- 100% of functions and customers have steady least-privilege entry enforcement.
- Guarantee solely safe, managed, wholesome gadgets will likely be granted entry to Microsoft tenants.
3. Defend networks
Defend Microsoft manufacturing networks and implement community isolation of Microsoft and buyer sources. As a part of this, we’re taking the next actions:
- Safe 100% of Microsoft manufacturing networks and techniques linked to the networks by bettering isolation, monitoring, stock, and safe operations.
- Apply community isolation and microsegmentation to 100% of the Microsoft manufacturing environments, creating further layers of protection in opposition to attackers.
- Allow clients to simply safe their networks and community isolate sources within the cloud.
4. Defend engineering techniques
Defend software program property and constantly enhance code safety by governance of the software program provide chain and engineering techniques infrastructure. As a part of this, we’re taking the next actions:
- Construct and keep stock for 100% of the software program property used to deploy and function Microsoft services.
- 100% of entry to supply code and engineering techniques infrastructure is secured by Zero Belief and least-privilege entry insurance policies.
- 100% of supply code that deploys to Microsoft manufacturing environments is protected by safety finest practices.
- Safe improvement, construct, check, and launch environments with 100% standardized, ruled pipelines and infrastructure isolation.
- Safe the software program provide chain to guard Microsoft manufacturing environments.
5. Monitor and detect threats
Complete protection and automated detection of threats to Microsoft manufacturing infrastructure and providers. As a part of this, we’re taking the next actions:
- Keep a present stock throughout 100% of Microsoft manufacturing infrastructure and providers.
- Retain 100% of safety logs for not less than two years and make six months of acceptable logs accessible to clients.
- 100% of safety logs are accessible from a central knowledge lake to allow environment friendly and efficient safety investigation and menace looking.
- Robotically detect and reply quickly to anomalous entry, behaviors, and configurations throughout 100% of Microsoft manufacturing infrastructure and providers.
6. Speed up response and remediation
Stop exploitation of vulnerabilities found by exterior and inner entities, by complete and well timed remediation. As a part of this, we’re taking the next actions:
- Cut back the Time to Mitigate for high-severity cloud safety vulnerabilities with accelerated response.
- Enhance transparency of mitigated cloud vulnerabilities by the adoption and launch of Frequent Weak point Enumeration™ (CWE™), and Frequent Platform Enumeration™ (CPE™) business requirements for launched excessive severity Frequent Vulnerabilities and Exposures (CVE) affecting the cloud.
- Enhance the accuracy, effectiveness, transparency, and velocity of public messaging and buyer engagement.
These targets instantly align to our learnings from the Midnight Blizzard incident in addition to all 4 CSRB suggestions to Microsoft and all 12 suggestions to cloud service suppliers (CSPs), throughout the areas of safety tradition, cybersecurity finest practices, auditing logging norms, digital id requirements and steering, and transparency.
We’re delivering on these targets by a brand new stage of coordination with a brand new working mannequin that aligns leaders and groups to the six SFI pillars, as a way to drive safety holistically and break down conventional silos. The pillar leaders are working throughout engineering Government Vice Presidents (EVPs) to drive built-in, cross-company engineering execution, doing this work in waves. These engineering waves contain groups throughout Microsoft Azure, Home windows, Microsoft 365, and Safety, with further product groups integrating into the method weekly.
Whereas there’s far more to do, we’ve made progress in executing in opposition to SFI priorities. For instance, we’ve applied automated enforcement of multifactor authentication by default throughout a couple of million Microsoft Entra ID tenants inside Microsoft, together with tenants for improvement, testing, demos, and manufacturing. We’ve got eradicated or diminished software targets by eradicating 730,000 apps thus far throughout manufacturing and company tenants that had been out-of-lifecycle or not assembly present SFI requirements. We’ve got expanded our logging to offer clients deeper visibility. And we lately introduced a major shift on our response course of: We are actually publishing root trigger knowledge for Microsoft CVEs utilizing the CWE™ business customary.
Adhering to requirements with paved paths techniques
Paved paths are finest practices from our discovered experiences, drawing upon classes reminiscent of the right way to optimize productiveness of our software program improvement and operations, the right way to obtain compliance (reminiscent of Software program Invoice of Supplies, Sarbanes-Oxley Act, Basic Information Safety Regulation, and others), and the right way to get rid of complete classes of vulnerabilities and mitigate associated dangers. A paved path turns into a typical when adoption considerably improves the developer or operations expertise or safety, high quality, or compliance.
With SFI, we’re explicitly defining requirements for every of the six safety pillars, and adherence to those requirements will likely be measured as targets and key outcomes (OKRs).
Driving steady enchancment
The Safe Future Initiative empowers all of Microsoft to implement the wanted adjustments to ship safety first. Our firm tradition is predicated on a development mindset that fosters an ethos of steady enchancment. We regularly search suggestions and new views to tune our strategy and progress. We’ll take our learnings from safety incidents, feed them again into our safety requirements, and operationalize these learnings as paved paths that may allow safe design and operations at scale.
Instituting new governance
We’re additionally taking main steps to raise safety governance, together with a number of organizational adjustments and extra oversight, controls, and reporting.
Microsoft is implementing a brand new safety governance framework spearheaded by the Chief Info Safety Officer (CISO). This framework introduces a partnership between engineering groups and newly fashioned Deputy CISOs, collectively liable for overseeing SFI, managing dangers, and reporting progress on to the Senior Management Workforce. Progress will likely be reviewed weekly with this govt discussion board and quarterly with our Board of Administrators.
Lastly, given the significance of menace intelligence, we’re bringing the complete breadth of nation-state actor and menace looking capabilities into the CISO group.
Instilling a security-first tradition
Tradition can solely be bolstered by our every day behaviors. Safety is a workforce sport and is finest realized when organizational boundaries are overcome. The engineering EVPs, in shut coordination with SFI pillar leaders, are holding broadscale weekly and month-to-month operational conferences that embrace all ranges of administration and senior particular person contributors. These conferences work on detailed execution and steady enchancment of safety in context with what we collectively ship to clients. By way of this technique of bottom-to-top and end-to-end downside fixing, safety pondering is ingrained in our every day behaviors.
Finally, Microsoft runs on belief and this belief should be earned and maintained. As a world supplier of software program, infrastructure, and cloud providers, we really feel a deep duty to do our half to maintain the world protected and safe. Our promise is to repeatedly enhance and adapt to the evolving wants of cybersecurity. That is job primary for us.

