Do you keep in mind when attackers have been sending the identical e-mail to everybody? These days are lengthy gone! Assaults are actually extra focused, inventive, and leverage respected cloud functions to provoke malicious assaults that evade status detection engines.
Using Machine Studying and Deep Studying fashions permits us to know the intention of the message, who’s sending it, and if the sender is pretending to be somebody they don’t seem to be. It additionally permits us to study what a authentic message appears like and determine the elements of an e-mail that point out malicious intent, making it simpler to foretell these markers sooner or later.
Cisco Safe Electronic mail Risk Protection makes use of these fashions to leverage a number of detection engines that concurrently consider completely different parts of an incoming e-mail to detect malicious intent whereas permitting authentic messages to undergo.
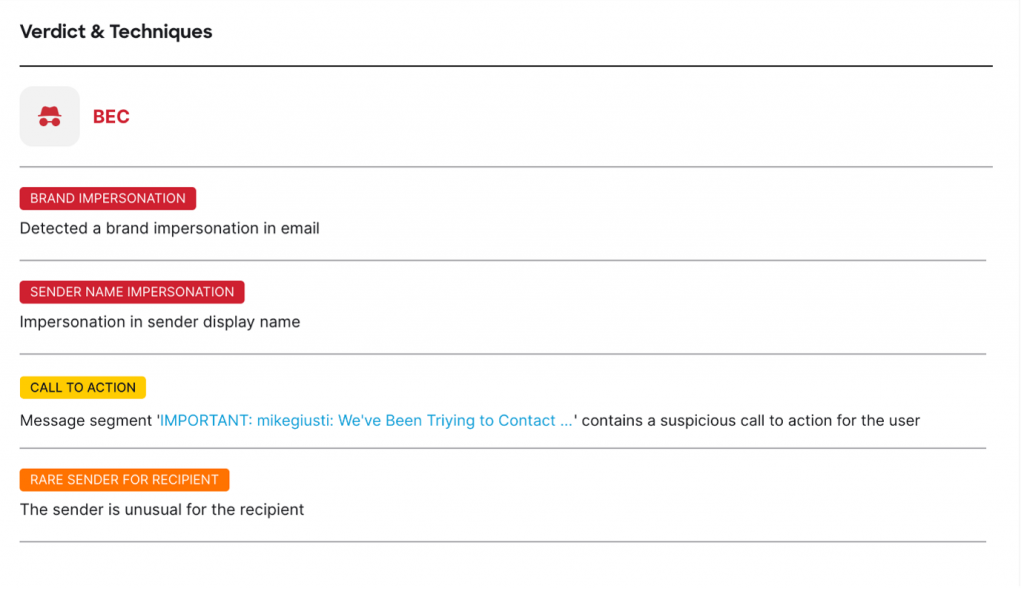
How will we do this? By producing indicators primarily based on data-driven detections. We then leverage these indicators to create a verdict. Nonetheless, it is very important perceive {that a} sign generated doesn’t imply a conviction as a sign alone doesn’t present the mandatory data to determine the intent of the message.
A notable instance of how Cisco makes use of AI is the connection mapping between senders and recipients. On common, solely 8% of the incoming e-mail visitors of a company comes from new senders whereas the remaining 92% is from current senders. Nonetheless, if we contemplate the malicious messages, 90% of them come from new senders that have been by no means seen earlier than. Having the ability to perceive if the sender is new or not generates a sign, which at the side of different indicators, can be utilized to succeed in a verdict.
One other nice instance of how our answer leverages AI is the potential of detecting the impersonation of customers and types. Many instances, attackers attempt to cover behind well-known manufacturers to lure the person to belief their requests. Though there are mechanisms for e-mail safety to reduce these makes an attempt (DMARC compliance), attackers can nonetheless attain the top person. AI permits us to know which model is being impersonated within the messages by trying to find logos and different brand-related data.
We will then analyze the content material of the message (topic, message textual content, request, signature, and so forth.) with what we all know to be authentic messages from that model. If one thing doesn’t match, we generate a sign that shall be used as a part of the conviction choice.
There are different methods the place we leverage AI like QR-code detection, name to motion requests, sense of urgency, pretend replies, and lots of different methods which can be used to trick the person.

With AI, even when the attacker adjustments the message textual content, format, or intent of the message, the Electronic mail Risk Protection will detect the menace and forestall these malicious messages from reaching the top customers — maintaining companies and knowledge secure!
When contemplating AI-driven e-mail safety, one factor is obvious, the panorama of digital protection has been perpetually altered. By leveraging AI, companies now have a robust software to make use of in opposition to evolving threats that focus on their customers and knowledge.
You’ll be able to depend on the Cisco Safe Electronic mail Risk Protection to maintain what you are promoting and knowledge safe. To see these indicators in motion, begin a free trial right now.
To learn extra concerning the AI in Safe Electronic mail Risk Protection, learn the white paper.
We’d love to listen to what you suppose. Ask a Query, Remark Beneath, and Keep Related with Cisco Safety on social!
Cisco Safety Social Channels
Share:

