
Digital identities, the digital credentials embedded in telephone wallets, office logins, and different apps, have gotten ubiquitous. Whereas they provide unprecedented comfort, in addition they create new privateness dangers, notably round monitoring and surveillance.
Certainly one of these dangers is linkability, the flexibility to affiliate a number of makes use of of a credential to a particular particular person. Presently, when individuals use their cellular driver’s license or log into varied apps, hidden identifiers can hyperlink these separate actions collectively, constructing detailed profiles of consumer habits.
To handle this, we’ve launched Crescent (opens in new tab), a cryptographic library that provides unlinkability to broadly used identification codecs, defending privateness. These embrace JSON Internet Tokens (the authentication normal behind many app logins) and cellular driver’s licenses. Crescent additionally works with out requiring the organizations that challenge these credentials to replace their techniques.
The safety goes past present privateness options. Some digital identification techniques already supply selective disclosure, permitting customers to share solely particular items of knowledge in every interplay.
However even with selective disclosure, credentials can nonetheless be linked by serial numbers, cryptographic signatures, or embedded identifiers. Crescent’s unlinkability function is designed to forestall something within the credential, past what a consumer explicitly chooses to disclose, from getting used to attach their separate digital interactions.

Two paths to unlinkability
To grasp how Crescent works, it helps to look at the 2 foremost approaches researchers have developed for including unlinkability to identification techniques:
- Specialised cryptographic signature schemes. These schemes can present unlinkability however require in depth modifications to present infrastructure. New algorithms should be standardized, applied, and built-in into software program and {hardware} platforms. For instance, the BBS (opens in new tab) signature scheme is presently being standardized by the Web Engineering Job Power (IETF), however even after completion, adoption could also be gradual.
- Zero-knowledge proofs with present credentials. This strategy, utilized by Crescent (opens in new tab), permits customers to show particular details about their credentials with out revealing the underlying information that might allow monitoring. For instance, somebody might show they maintain a legitimate driver’s license and stay in a selected ZIP code with out exposing some other private info or identifiers that might hyperlink this interplay to future ones.
Zero-knowledge proofs have turn into extra sensible since they had been first developed 40 years in the past however they don’t seem to be as environment friendly because the cryptographic algorithms utilized in right now’s credentials. Crescent addresses this computational problem by preprocessing, performing essentially the most advanced calculations as soon as prematurely in order that later proof era is fast and environment friendly for cellular gadgets.
Past unlinkability, Crescent helps selective disclosure, permitting customers to show particular details with out revealing pointless particulars. For instance, it could possibly affirm {that a} credential is legitimate and unexpired with out disclosing the precise expiration date, which could in any other case function a singular identifier. These privateness protections work even when credentials are saved in a telephone’s safe {hardware}, which retains them tied to the machine and prevents unauthorized entry.
PODCAST SERIES
The AI Revolution in Medication, Revisited
Be part of Microsoft’s Peter Lee on a journey to find how AI is impacting healthcare and what it means for the way forward for drugs.
Behind the cryptographic curtain
At its core, Crescent makes use of a classy type of cryptographic proof known as a zero-knowledge SNARK (Zero-Information Succinct Noninteractive Argument of Information). This methodology permits one social gathering to show possession of knowledge or credentials with out revealing the underlying information itself.
Crescent particularly makes use of the Groth16 proof system, one of many first sensible implementations of this know-how. What makes Groth16 notably helpful is that its proofs are small in measurement, fast to confirm, and may be shared in a single step with out back-and-forth communication between the consumer and verifier.
The system works by first establishing shared cryptographic parameters primarily based on a credential template. A number of organizations issuing comparable credentials, comparable to totally different state motorcar departments issuing cellular driver’s licenses, can use the identical parameters so long as they comply with appropriate information codecs and safety requirements.
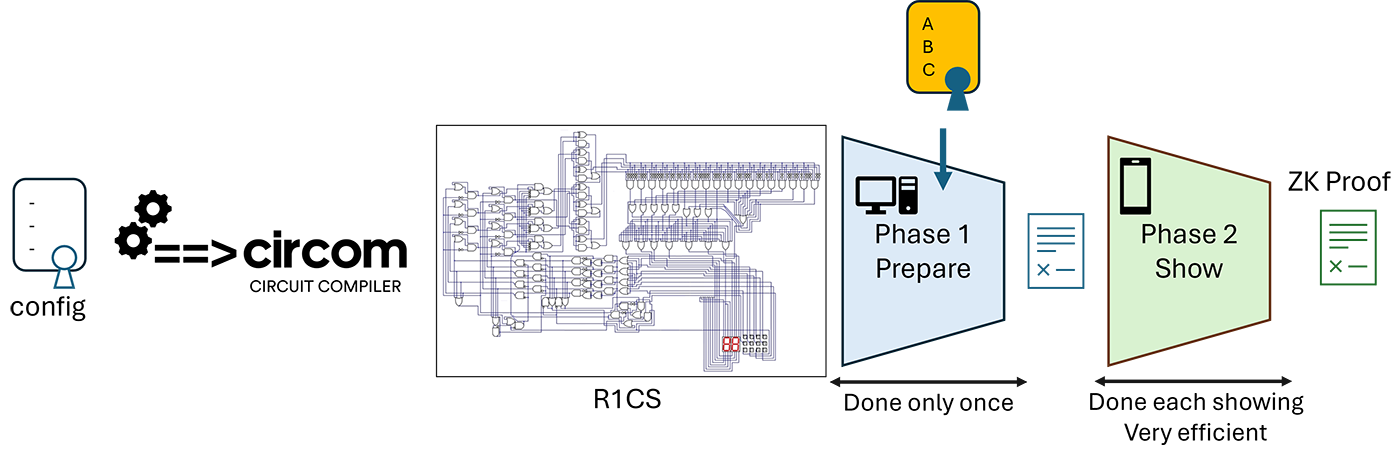
The mathematical guidelines that outline what every proof will confirm are written utilizing specialised programming instruments that convert them right into a Rank-1 Constraint System (R1CS), a mathematical framework that describes precisely what must be confirmed a few credential.
To make the system quick sufficient for real-world use, Crescent splits the proof era into two distinct phases:
- Put together stage. This step runs as soon as and generates cryptographic values that may be saved on the consumer’s machine for repeated use.
- Present stage. When a consumer must current their credential, this faster step takes the saved values and randomizes them to forestall any connection to earlier shows. It additionally creates a compact cryptographic abstract that reveals solely the precise info wanted for that individual interplay.
Figures 2 and three illustrate this credential-proving workflow and the division between the put together and present steps.

A pattern software
To exhibit how Crescent works, we created a pattern software protecting two real-world eventualities: verifying employment and proving age for on-line entry. The applying contains pattern code for establishing fictional issuers and verifiers as Rust servers, together with a browser-extension pockets for the consumer. The step numbers correspond to the steps in Determine 4.
Setup
- A Crescent service pre-generates the zero-knowledge parameters for creating and verifying proofs from JSON Internet Tokens and cellular driver’s licenses.
- The consumer obtains a cellular driver’s license from their Division of Motor Automobiles.
- The consumer obtains a proof-of-employment JSON Internet Token from their employer, Contoso.
- These credentials and their non-public keys are saved within the Crescent pockets.
Situations
- Employment verification: The consumer presents their JSON Internet Token to Fabrikam, a web based well being clinic, to show they’re employed at Contoso and eligible for office advantages. Fabrikam learns that the consumer works at Contoso however not the consumer’s identification, whereas Contoso stays unaware of the interplay.
- Age verification: The consumer presents their cellular driver’s license to a social community, proving they’re over 18. The proof confirms eligibility with out revealing their age or identification.
Throughout each eventualities, Crescent ensures that credential shows stay unlinkable, stopping any social gathering from connecting them to the consumer.
For simplicity, the pattern defines its personal issuance and presentation protocol, however it could possibly be built-in into higher-level identification frameworks comparable to OpenID/OAuth, Verifiable Credentials, or the cellular driver’s license ecosystem.

To study extra in regards to the venture, go to the Crescent venture GitHub (opens in new tab) web page, or try our current shows given on the Actual-Phrase Crypto 2025 (opens in new tab) and North Sec 2025 (opens in new tab) conferences.

