Many organizations depend on the Safe File Switch Protocol (SFTP) because the business commonplace for exchanging vital enterprise information. Historically, securely connecting to non-public SFTP servers required customized infrastructure, handbook scripting, or exposing endpoints to the general public web.
At the moment, AWS Switch Household SFTP connectors now assist connectivity to distant SFTP servers via Amazon Digital Non-public Cloud (Amazon VPC) environments. You may switch information between Amazon Easy Storage Service (Amazon S3) and personal or public SFTP servers whereas making use of the safety controls and community configurations already outlined in your VPC. This functionality helps you combine information sources throughout on-premises environments, partner-hosted non-public servers, or internet-facing endpoints, with the operational simplicity of a totally managed Amazon Net Providers (AWS) service.
New capabilities with SFTP connectors
The next are the important thing enhancements:
- Join to non-public SFTP servers – SFTP connectors can now attain endpoints which might be solely accessible inside your AWS VPC connection. These embrace servers hosted in your VPC or a shared VPC, on-premises techniques related over AWS Direct Join, and partner-hosted servers related via VPN tunnels.
- Safety and compliance – All file transfers are routed via the safety controls already utilized in your VPC, akin to AWS Community Firewall or centralized ingress and egress inspection. Non-public SFTP servers stay non-public and don’t have to be uncovered to the web. You may as well current static Elastic IP or convey your personal IP (BYOIP) addresses to satisfy accomplice allowlist necessities.
- Efficiency and ease – Through the use of your personal community assets akin to NAT gateways, AWS Direct Join or VPN connections, connectors can make the most of increased bandwidth capability for large-scale transfers. You may configure connectors in minutes via the AWS Administration Console, AWS Command Line Interface (AWS CLI), or AWS SDKs with out constructing customized scripts or third-party instruments.
How VPC- primarily based SFTP connections work
SFTP connectors use Amazon VPC Lattice assets to ascertain safe connectivity via your VPC. Key constructs embrace a useful resource configuration and a useful resource gateway. The useful resource configuration represents the goal SFTP server, which you specify utilizing a non-public IP handle or public DNS title. The useful resource gateway gives SFTP connector entry to those configurations, enabling file transfers to circulate via your VPC and its safety controls.
The next structure diagram illustrates how site visitors flows between Amazon S3 and distant SFTP servers.  As proven within the structure, site visitors flows from Amazon S3 via the SFTP connector into your VPC. A useful resource gateway is the entry level that handles inbound connections from the connector to your VPC assets. Outbound site visitors is routed via your configured egress path, utilizing Amazon VPC NAT gateways with Elastic IPs for public servers or AWS Direct Join and VPN connections for personal servers. You need to use present IP addresses out of your VPC CIDR vary, simplifying accomplice server allowlists. Centralized firewalls within the VPC implement safety insurance policies, and customer-owned NAT gateways present increased bandwidth for large-scale transfers.
As proven within the structure, site visitors flows from Amazon S3 via the SFTP connector into your VPC. A useful resource gateway is the entry level that handles inbound connections from the connector to your VPC assets. Outbound site visitors is routed via your configured egress path, utilizing Amazon VPC NAT gateways with Elastic IPs for public servers or AWS Direct Join and VPN connections for personal servers. You need to use present IP addresses out of your VPC CIDR vary, simplifying accomplice server allowlists. Centralized firewalls within the VPC implement safety insurance policies, and customer-owned NAT gateways present increased bandwidth for large-scale transfers.
When to make use of this function
With this functionality, builders and IT directors can simplify workflows whereas assembly safety and compliance necessities throughout a spread of eventualities:
- Hybrid environments – Switch information between Amazon S3 and on-premises SFTP servers utilizing AWS Direct Join or AWS Website-to-Website VPN, with out exposing endpoints to the web.
- Accomplice integrations – Join with enterprise companions’ SFTP servers which might be solely accessible via non-public VPN tunnels or shared VPCs. This avoids constructing customized scripts or managing third-party instruments, lowering operational complexity.
- Regulated industries – Route file transfers via centralized firewalls and inspection factors in VPCs to adjust to monetary companies, authorities, or healthcare safety necessities.
- Excessive-throughput transfers – Use your personal community configurations akin to NAT gateways, AWS Direct Join, or VPN connections with Elastic IP or BYOIP to deal with large-scale, high-bandwidth transfers whereas retaining IP addresses already on accomplice allowlists.
- Unified file switch resolution – Standardize on Switch Household for each inside and exterior SFTP connectivity, lowering fragmentation throughout file switch instruments.
Begin constructing with SFTP connectors
To start transferring information with SFTP connectors via my VPC atmosphere, I observe these steps:
First, I configure my VPC Lattice assets. Within the Amazon VPC console, beneath PrivateLink and Lattice within the navigation pane, I select Useful resource gateways, select Create useful resource gateway to create one to behave because the ingress level into my VPC. 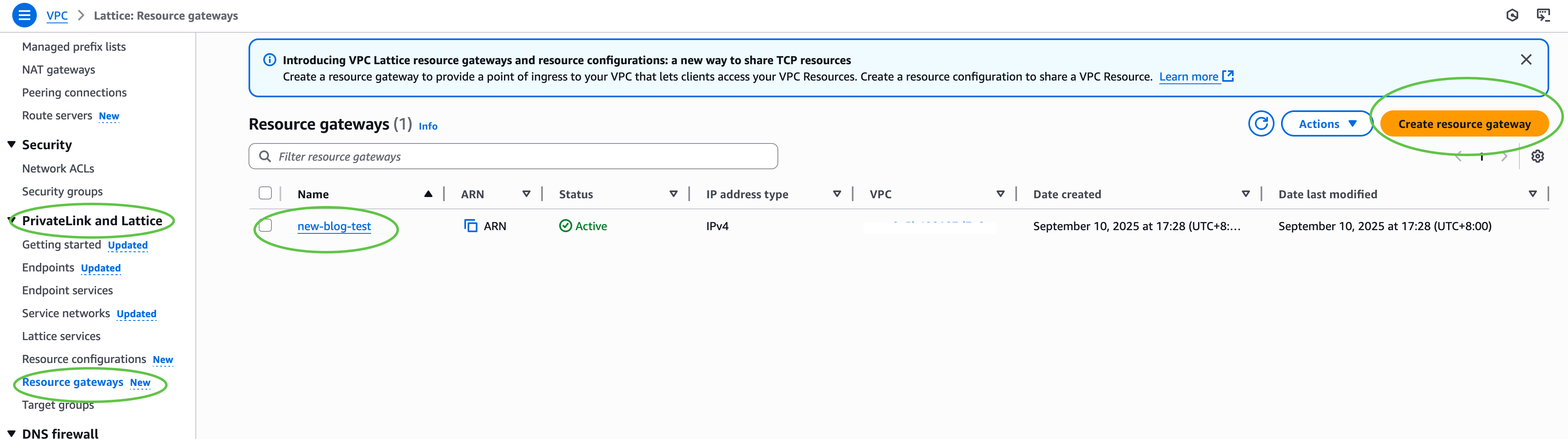 Subsequent, beneath PrivateLink and Lattice within the navigation pane, I select Useful resource configuration and select Create useful resource configuration to create a useful resource configuration for my goal SFTP server. Specify the non-public IP handle or public DNS title, and the port (sometimes 22).
Subsequent, beneath PrivateLink and Lattice within the navigation pane, I select Useful resource configuration and select Create useful resource configuration to create a useful resource configuration for my goal SFTP server. Specify the non-public IP handle or public DNS title, and the port (sometimes 22). 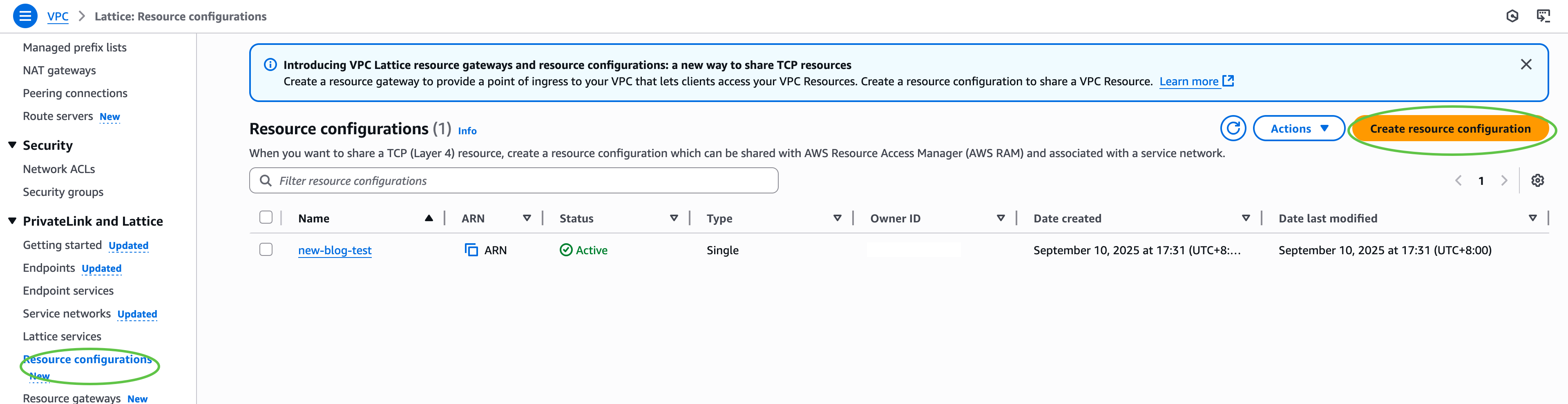
Then, I configure AWS Id and Entry Administration (IAM) permissions. I be certain that the IAM function used for connector creation has switch:* permissions, and VPC Lattice permissions (vpc-lattice:CreateServiceNetworkResourceAssociation, vpc-lattice:GetResourceConfiguration, vpc-lattice:AssociateViaAWSService). I replace the belief coverage on the IAM function to specify switch.amazonaws.com as a trusted principal. This permits AWS Switch Household to imagine the function when creating and managing my SFTP connectors.
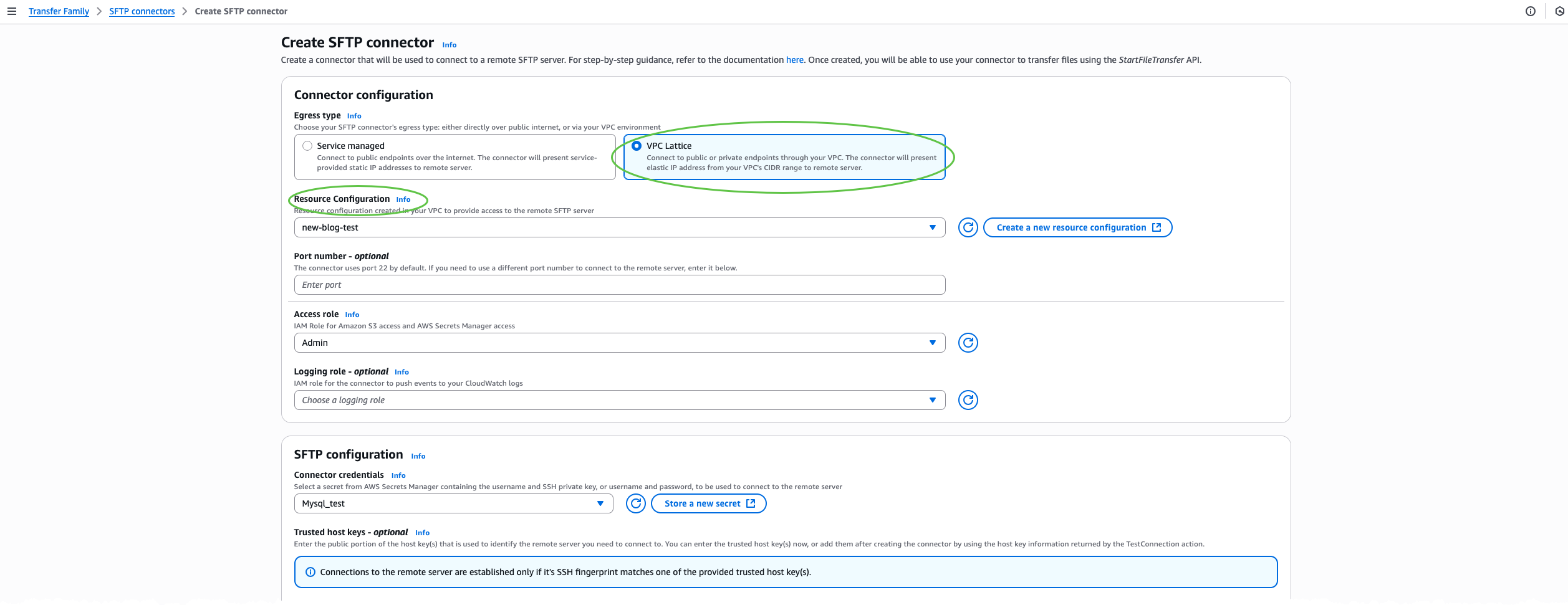
After that, I create an SFTP connector via the AWS Switch Household console. I select SFTP Connectors after which select Create SFTP connector. 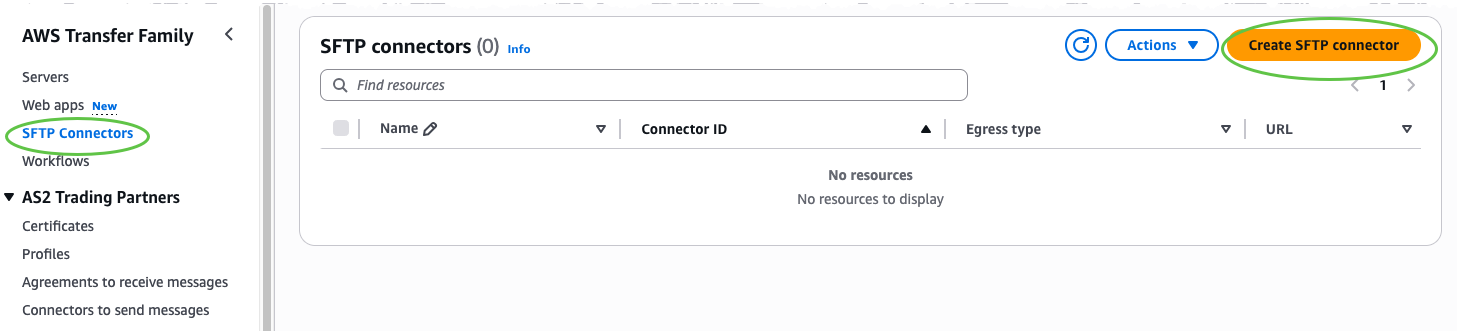 Within the Connector configuration part, I choose VPC Lattice because the egress kind, then present the Amazon Useful resource Identify (ARN) of the Useful resource Configuration, Entry function, and Connector credentials. Optionally, embrace a trusted host key for enhanced safety, or override the default port if my SFTP server makes use of a nonstandard port.
Within the Connector configuration part, I choose VPC Lattice because the egress kind, then present the Amazon Useful resource Identify (ARN) of the Useful resource Configuration, Entry function, and Connector credentials. Optionally, embrace a trusted host key for enhanced safety, or override the default port if my SFTP server makes use of a nonstandard port.
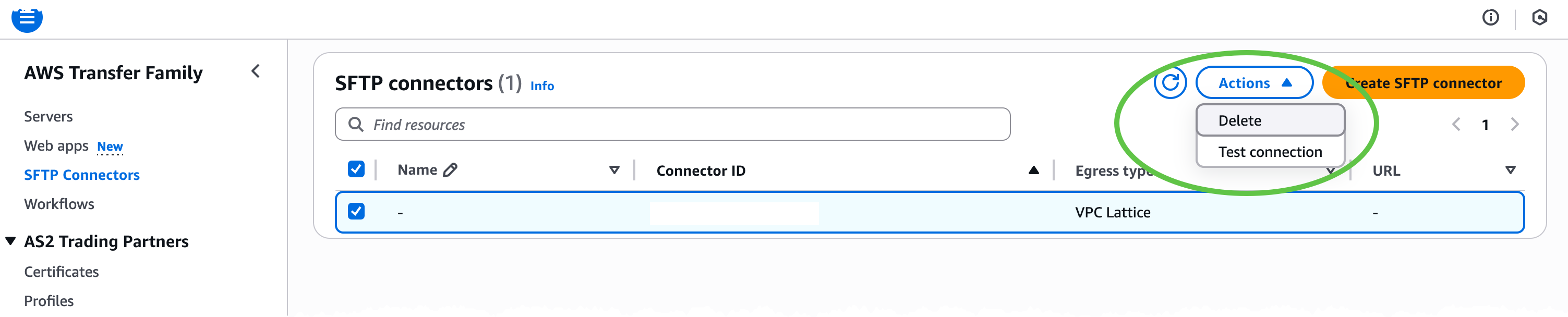
 Subsequent, I check the connection. On the Actions menu, I select Check connection to substantiate that the connector can attain the goal SFTP server.
Subsequent, I check the connection. On the Actions menu, I select Check connection to substantiate that the connector can attain the goal SFTP server.
 Lastly, after the connector standing is ACTIVE, I can start file operations with my distant SFTP server programmatically by calling Switch Household APIs akin to
Lastly, after the connector standing is ACTIVE, I can start file operations with my distant SFTP server programmatically by calling Switch Household APIs akin to StartDirectoryListing, StartFileTransfer, StartRemoteDelete, or StartRemoteMove. All site visitors is routed via my VPC utilizing my configured assets akin to NAT gateways, AWS Direct Join, or VPN connections along with my IP addresses and safety controls.
For the entire set of choices and superior workflows, confer with the AWS Switch Household documentation.
Now out there
SFTP connectors with VPC-based connectivity at the moment are out there in 21 AWS Areas. Test the AWS Providers by Area for the newest supported AWS Areas. Now you can securely join AWS Switch Household SFTP connectors to non-public, on-premises, or internet-facing servers utilizing your personal VPC assets akin to NAT gateways, Elastic IPs, and community firewalls.
— Betty


