As a part of Week of Brokers, prospects can now handle fashions, MCP and instruments by way of Databricks AI Gateway, absolutely built-in with Unity Catalog. To ship actual worth, brokers have to securely attain exterior instruments like GitHub, Glean, and Atlassian. AI Gateway makes this simple and safe, so groups can give attention to constructing brokers, not auth infrastructure.
On this put up, we’ll stroll by way of the right way to join an exterior MCP server and deploy an agent finish to finish, to be able to construct context-aware brokers that purpose and act in your knowledge.
The issue: Authenticating exterior MCP servers
AI brokers are solely as highly effective because the instruments they’ll entry. The Mannequin Context Protocol (MCP) supplies a common method to uncover and work together with these instruments, and on Databricks, enterprises already use it to attach brokers with native and exterior MCPs.
Many times, prospects inform us the identical factor: auth is the bottleneck. Each supplier has its personal OAuth app registration, its personal consumer secrets and techniques, its personal token refresh logic. Secrets and techniques want rotating, permissions want auditing, and there is no centralized method to observe which brokers are accessing what. What ought to take minutes takes weeks.
The answer: AI Gateway for exterior connectivity
AI Gateway solves this by giving groups a single, ruled method to join brokers to exterior methods:
- Govern exterior MCP servers by way of Unity Catalog: Each exterior MCP server is registered in Unity Catalog, making it discoverable and ruled like every other catalog object. Admins can apply fine-grained permissions, with all exercise captured in a centralized audit desk. Groups may set up MCP servers from companions by way of Databricks Market.
- Entry on behalf of the consumer: Brokers act on behalf of the top consumer, so Consumer A’s agent solely sees what Consumer A is allowed to see. This implies brokers can safely entry private e mail, personal repos, and restricted paperwork with out overprivileged service accounts. Admins can additional prohibit what brokers are allowed to do by scoping OAuth permissions per connection, like limiting a GitHub connection to read-only repo entry.
- Simplify authentication to exterior methods: Managed OAuth flows simplify auth, without having to register OAuth apps or handle secrets and techniques per supplier. Decide from a dropdown and Databricks handles the total auth lifecycle server-side. Supported suppliers in the present day embody Glean, GitHub, Atlassian (Jira and Confluence), Google Drive, and SharePoint, with extra on the way in which.
- Works throughout clouds and suppliers: The identical governance and auth expertise whether or not you run Databricks on AWS, Azure, or GCP, with pre-configured assist for third-party suppliers like GitHub, Glean, and Atlassian.
The way it works
Let’s stroll by way of connecting GitHub as an exterior MCP server and taking all of it the way in which to a deployed agent.
Step 1. Create the connection.
- Navigate to AI Gateway → Register MCP Server -> Exterior MCP
- Choose your auth mode: Per-Consumer OAuth (advisable — every consumer authenticates with their very own id) or Shared Principal (single id for all customers)
- Decide GitHub from the supplier dropdown
- Create. Databricks handles OAuth app registration, token trade, and refresh behind the scenes

Step 2. Check it. You may validate the connection in two methods. In AI Playground, choose a mannequin with instruments enabled, browse your exterior MCP connections, choose GitHub, and ask “What are the open pull requests in repo X?”
Or check straight in code utilizing DatabricksMCPClient:
Step 3. Deploy your agent. As soon as validated, deploy with Agent Bricks.
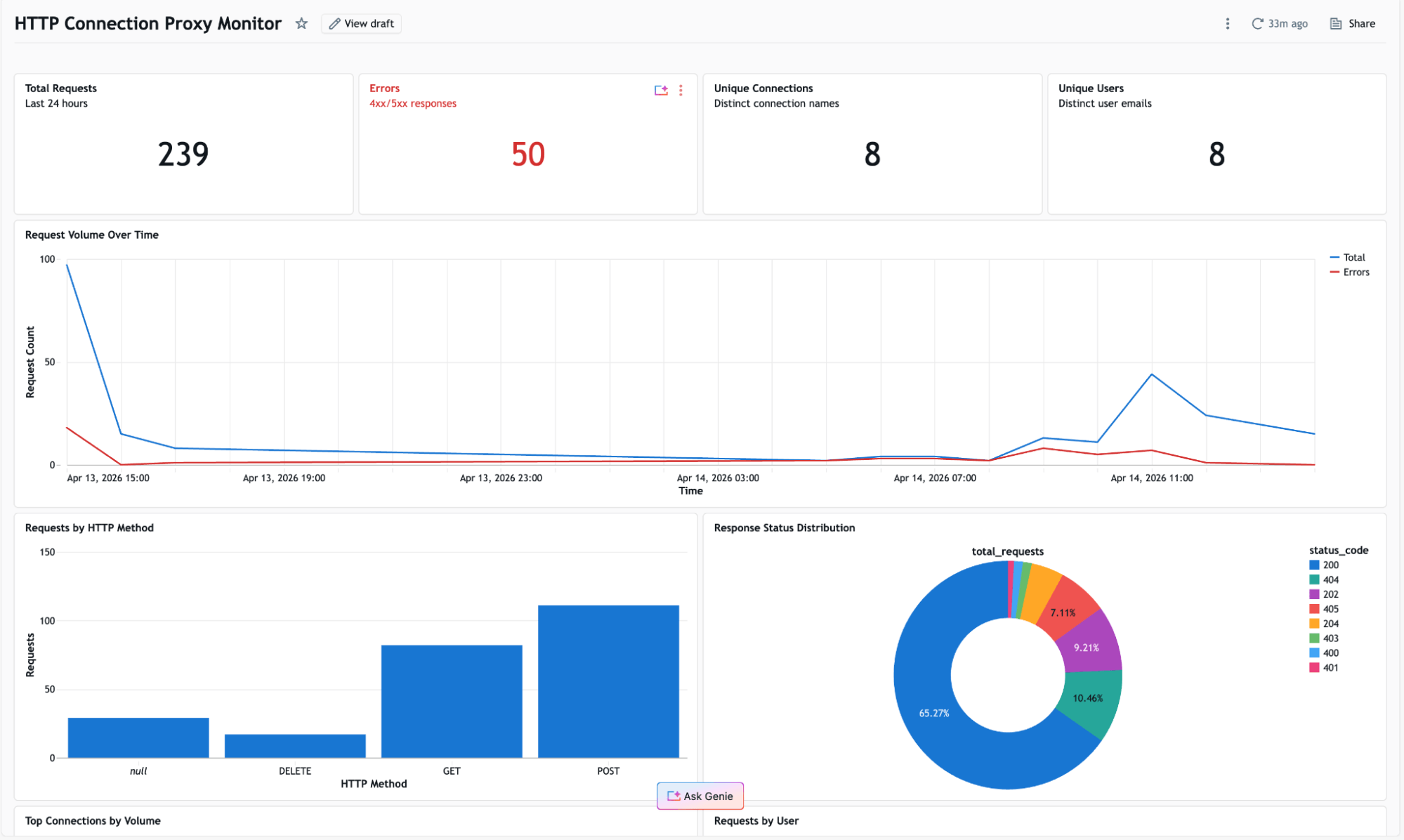
Step 4. Monitor and hint. As soon as your agent is reside, MLflow Tracing offers you end-to-end observability: each request, each instrument name, each MCP server interplay, with full inputs and outputs. Mix with Unity Catalog audit logs to see who accessed what, when, and thru which agent.
Get began
Do not let auth be the explanation your brokers cannot attain the instruments they want. Begin constructing brokers that purpose and act on each inner and exterior knowledge. Get began in the present day.

