The collection of posts on single sign-on to Amazon Redshift with AWS IAM Identification Middle (successor to AWS Single Signal-On) integration continues from our prior submit.
On this submit, we define a complete information for establishing single sign-on from Tableau desktop to Amazon Redshift utilizing integration with IAM Identification Middle and PingFederate because the identification supplier (IdP) with an LDAP primarily based knowledge retailer, AWS Listing Service for Microsoft Energetic Listing.
Stipulations
It’s best to have the next stipulations:
- A PingFederate account that has an lively subscription. You want an admin position to arrange the applying on PingFederate. When you’re new to PingFederate, you possibly can attain out to Ping Identification Gross sales.
- A working PingFederate server.
- Amazon Redshift Serverless workgroup or a provisioned Amazon Redshift knowledge warehouse.
- Obtain and set up the newest Redshift ODBC 2.X driver.
- Obtain and set up Tableau Desktop 2024.1 or later
- Set up Tableau Server 2023.3.9 or later. For Tableau Server set up, see Set up and Configure Tableau Server.
Answer overview
PingFederate occasion connects to IAM Identification Middle utilizing SAML. The customers and teams in PingFederate are synced to IAM Identification Middle utilizing an open normal SCIM. After you arrange SAML and SCIM, it is possible for you to to allow single sign-on to Amazon Redshift from the AWS Administration Console utilizing Amazon Redshift Question Editor v2. That is achieved by creating an Identification Middle utility within the Amazon Redshift console.
To allow single sign-on to Amazon Redshift from outdoors of AWS utilizing a third-party shopper like Tableau, you arrange a trusted token issuer token trade utilizing OIDC normal.
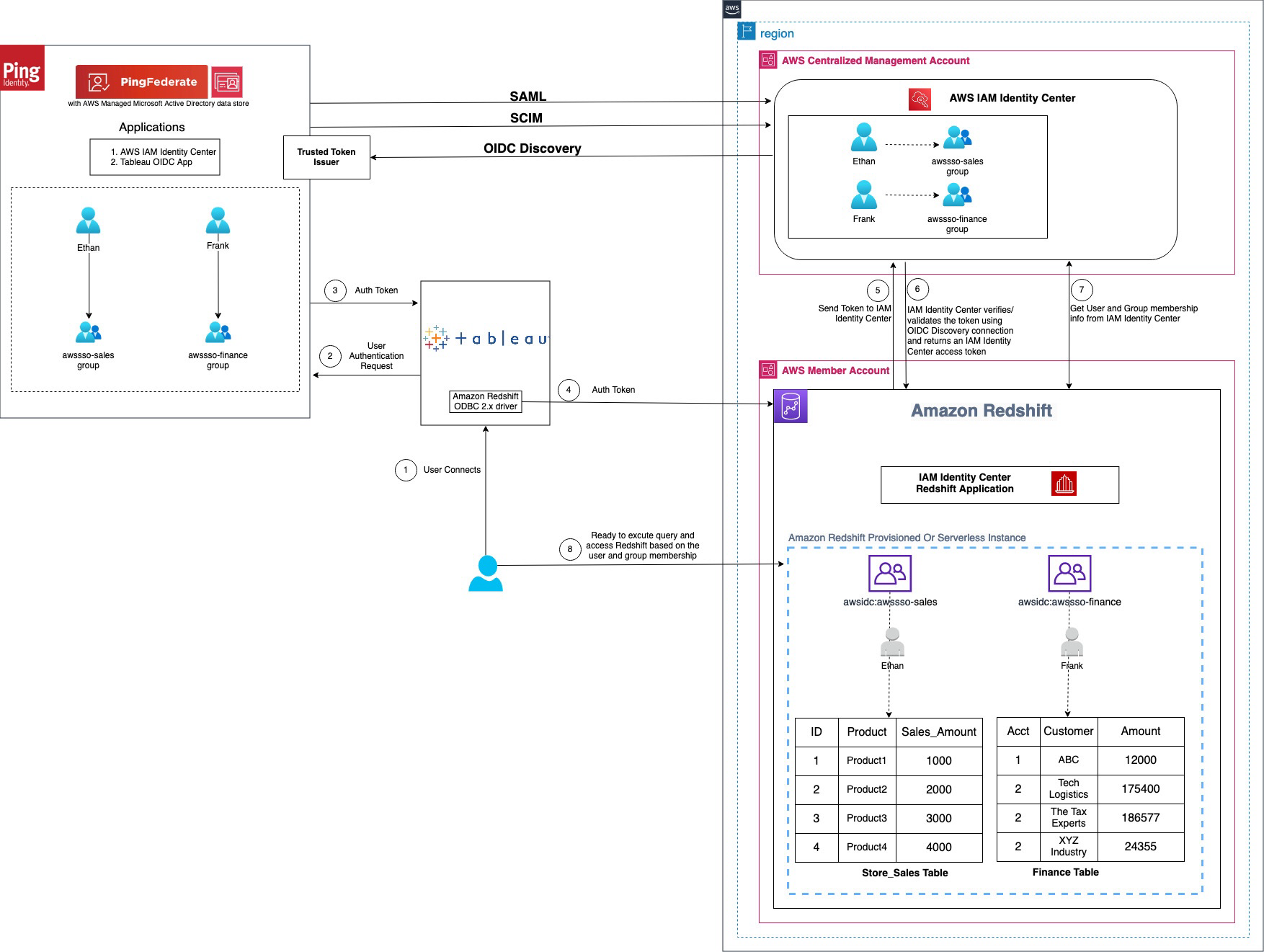
Determine 1 : Answer overview for Tableau integration with Amazon Redshift utilizing IAM Identification Middle and Ping Federate
The workflow, proven within the previous determine, consists of the next steps:
- The person configures Tableau to entry Amazon Redshift utilizing IAM Identification Middle authentication.
- On a person sign-in try, Tableau initiates a browser-based OAuth movement and redirects the person to the PingFederate register web page to enter the sign-in credentials. Password validation is finished in opposition to the AWS Managed Microsoft AD knowledge retailer.
- On profitable authentication, PingFederate points an authentication token (ID and entry token) to Tableau.
- The Amazon Redshift driver then makes a name to the Amazon Redshift-enabled Identification Middle utility and forwards the
- Amazon Redshift passes the token to Identification Middle and requests an entry token.
- Identification Middle verifies the token utilizing the OIDC discovery connection to the trusted token issuer and returns an Identification Middle-generated entry token for a similar person. Within the previous determine, trusted token issuer (TTI) is the PingFederate server that Identification Middle trusts to supply tokens that third-party purposes like Tableau use to name AWS companies.
- Amazon Redshift then makes use of the token to acquire the person and group membership data from Identification Middle.
- Tableau person will be capable to join with Amazon Redshift and entry knowledge primarily based on the person and group membership returned from Identification Middle. The person and group settings within the LDAP-based AWS Managed Microsoft AD knowledge retailer for PingFederate are propagated to identification middle utilizing SCIM protocol for outbound provisioning.
Walkthrough
On this walkthrough, you’ll use the next steps to construct the answer:
- SAML and SCIM arrange between PingFederate and IAM Identification Middle
- Connect with Amazon Redshift utilizing Question Editor v2
- Configure identification federation from a third-party shopper
- Create an entry token supervisor and entry token mapping
- Create an OIDC coverage
- Create an OAuth shopper
- Arrange a PingFederate Authorization Server
- Coverage Contract Grant Mapping
- Gather PingFederate data
- Arrange a trusted token issuer in IAM Identification Middle
- Arrange shopper connections and trusted token issuers in Amazon Redshift
- Configure Tableau OAuth config information for PingFederate to combine with Amazon Redshift utilizing IAM Identification Middle
- Set up a Tableau OAuth config file on a shopper machine for Tableau Desktop
- Set up a Tableau OAuth config file for a website on Tableau Server or Tableau Cloud
- Federate to Amazon Redshift from Tableau Desktop utilizing Identification Middle
- Federate to Amazon Redshift from Tableau Server utilizing Identification Middle authentication
SAML and SCIM arrange between PingFederate and IAM Identification Middle
IAM Identification Middle integration with PingFederate begins with SAML arrange adopted by SCIM.
- Arrange SAML 2.0 for SP Connection of kind Browser SSO (single sign-on) in PingFederate.
- Arrange SCIM 2.0 for outbound provisioning. It’s going to sync the customers and teams created in an LDAP primarily based knowledge retailer like AWS managed Microsoft AD for PingFederate to the customers and teams in IAM Identification Middle.
The implementation for the cloud primarily based IdP choice PingOne isn’t in scope of this submit and follows steps just like these described in Combine IdP with Amazon Redshift Question Editor v2 utilizing AWS IAM Identification Middle for seamless Single Signal-On.
Additional particulars of SAML and SCIM arrange are as follows.
- Set up PingFederate Server.
- Arrange IAM Identification middle integration by following the Ping documentation together with the obtain for Identification Middle integration information.
- Deploy the mixing information to your PingFederate set up.
- Allow provisioning and configure IdP Browser SSO (SAML connection). (You may implement Browser SSO connection solely utilizing IAM Identification Middle metadata file.)
- Below System > Server > Protocol Settings > Federation Information
BASE_URLarea, use the publicly accessible totally certified area title of the PingFederate server. - Create an LDAP primarily based knowledge retailer (the title used on this instance is
AWSManagedMSAD) as a result of SCIM 2.0 protocol for outbound provisioning solely works with LDAP primarily based knowledge shops with PingFederate. If you’re utilizing a cloud-based answer like PinOne, you possibly can arrange outbound provisioning in PingOne itself. Thus for this writing, we have now used AWS Managed Microsoft AD as an information retailer created utilizing AWS Listing Service. - Create a password credential validator (title used on this instance is
awsmanagedmsadpassval) and IdP adapters (title used on this instance isawsmanagedmsadadapter) in your knowledge retailer as relevant. - Create an SP connection of kind Browser SSO utilizing the
sp-saml-metadata.xmlfile as defined in making a provisioning connection.
- Below System > Server > Protocol Settings > Federation Information
- Export SAML metadata from PingFederate.
- Register PingFederate as an IdP in Identification Middle.
- Navigate again to the connection saved in step b, and configure outbound provisioning.
- Allow provisioning in IAM Identification Middle by following step 1 within the documentation.
- Then, configure provisioning in PingFederate by following step 2 within the documentation.
- Optionally, you possibly can configure and move person attributes from PingFederate for entry management in Identification Middle.
Subsequent, hook up with Amazon Redshift utilizing its native question editor, Question Editor v2, to validate AWS companies’ connectivity utilizing IAM Identification Middle.
Connect with Amazon Redshift utilizing Question Editor v2
Full the Walkthrough part of IAM Identification Middle integration with Amazon Redshift, which is able to arrange your Amazon Redshift connectivity with Question Editor v2.
When you want additional assist with SAML and SCIM arrange, and connecting to Amazon Redshift utilizing Question Editor v2, you may also comply with step-by-step guided demo video single sign-on to Amazon Redshift with IAM IDC integration utilizing PingFederate with AWS Managed MSAD Demo
Configure identification federation from a third-party shopper
Configure identification federation enabled by IAM Identification Middle from IdP PingFederate to the service supplier Amazon Redshift utilizing an exterior shopper like Tableau. The next steps within the PingFederate admin console and Identification Middle information you thru the identification federation course of.
Create an entry token supervisor and entry token mapping
To map PingFederate attributes to OAuth entry tokens and OpenID Join ID (OIDC) tokens, create an entry token supervisor and token mapping. For full particulars and arrange primarily based in your safety wants, see Token mapping in PingFederate, which explains entry token administration intimately. Full the next steps to create a token supervisor.
- Within the PingFederate administrative console, go to Purposes > OAuth > Entry Token Administration, and select Create New Occasion.
- In Sort tab,
- Enter an Occasion Title and Occasion ID of your alternative, for instance
TrustedTokenIssuerMgr. - Choose the Sort from drop down listing as JSON Internet Tokens, generally known as JWT.
- Depart Guardian occasion as None and select Subsequent.
- Enter an Occasion Title and Occasion ID of your alternative, for instance
- In Occasion configuration tab,
- Below Certificates, choose Add a brand new row to ‘Certificates’, choose the certificates for token supervisor from the drop-down listing, enter a Key ID akin to
certkey, and select Replace beneath Motion. You may create a brand new certificates by navigating to Safety > Certificates & Key Administration > Signing & Decryption Keys & Certificates > Create New. - Choose Use Centralized Signing Key.
- In JWS Algorithm, choose RSA utilizing SHA-256.
- Choose Allow Token Revocation. Depart the whole lot else as default and select Subsequent.
- Below Certificates, choose Add a brand new row to ‘Certificates’, choose the certificates for token supervisor from the drop-down listing, enter a Key ID akin to
- Below Session Validation tab,
- Choose Embody Session Identifier in Entry Token.
- Choose Examine for legitimate authentication session.
- Depart different selections as is and select Subsequent.
- Within the Entry Token Attribute Contract tab, go away the Topic Attribute Title because the e default and proceed to Lengthen the Contract so as to add the next attribute and values.
- Enter
aud, go away multi-value unchecked. Select Add beneath Motion. - Repeat the identical to enter electronic mail, exp, iss, sub. When accomplished, select Subsequent.
- Enter
- On every of Useful resource URIs and Entry Management tabs, go away as is and select Subsequent.
- On the Abstract tab, evaluation your modifications and select Save. An occasion title with the title you offered, like TrustedTokenIssuerMgr seems in Purposes > Oauth > Entry Token Administration.
Determine 2 : Entry Token Administration Configuration Abstract
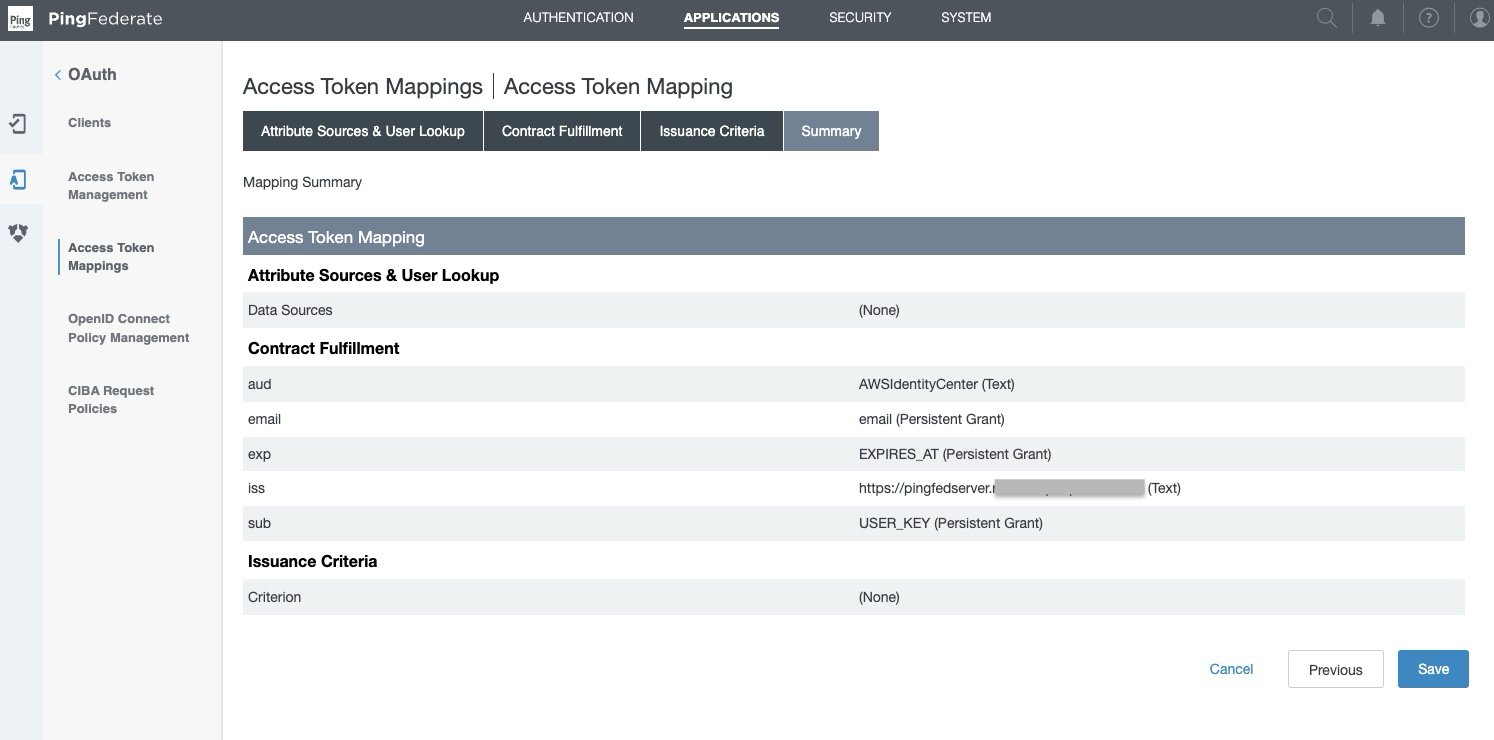
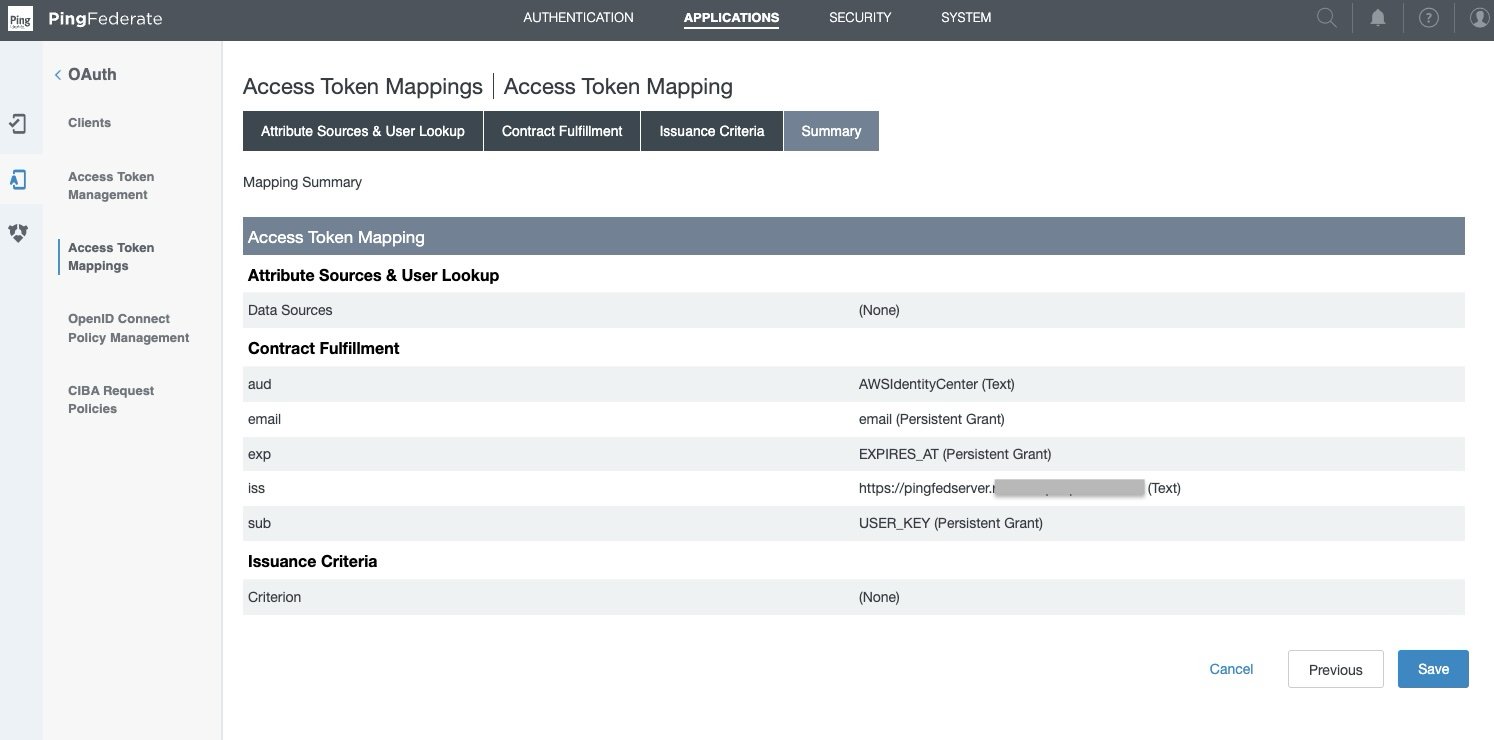
- Navigate to Purposes > OAuth > Entry Token Mappings, choose the default Context and Entry Token Supervisor, TrustedTokenIssuerMgr that was created within the earlier step. Select Add Mapping.
- Depart Attribute Sources & Consumer Lookup as is and select Subsequent.
- Below Contract Success tab,
- For Contract aud, choose Textual content from the Supply, and enter the Worth as
AWSIdentityCenter. - For Contract electronic mail, choose Persistent Grant from the Supply, and Worth as electronic mail.
- For Contract exp, choose Persistent Grant from the Supply, and Worth as EXPIRES_AT.
- For Contract iss, choose Textual content from the Supply, and enter your base URL because the Worth, like
https://yourwebsite.area.com, the identical as in System > Server > Protocol Settings > BASE URL. - For Attribute Contract sub, choose Persistent Grant from the Supply, and Worth as USER_KEY.
- Select on Subsequent.
- For Contract aud, choose Textual content from the Supply, and enter the Worth as
- Depart Issuance Standards as is and select Subsequent.
- On the Abstract tab, evaluation all of your modifications and select Save. A brand new default Context with Entry Token Supervisor if TrustedTokenIssuerMgr seems in Purposes > OAuth > Entry Token Mappings.
Create an OIDC coverage
For full particulars and arrange primarily based in your safety wants, see to Open ID join (OIDC) coverage administration in PingFederate. Full the next steps to arrange an OIDC coverage.
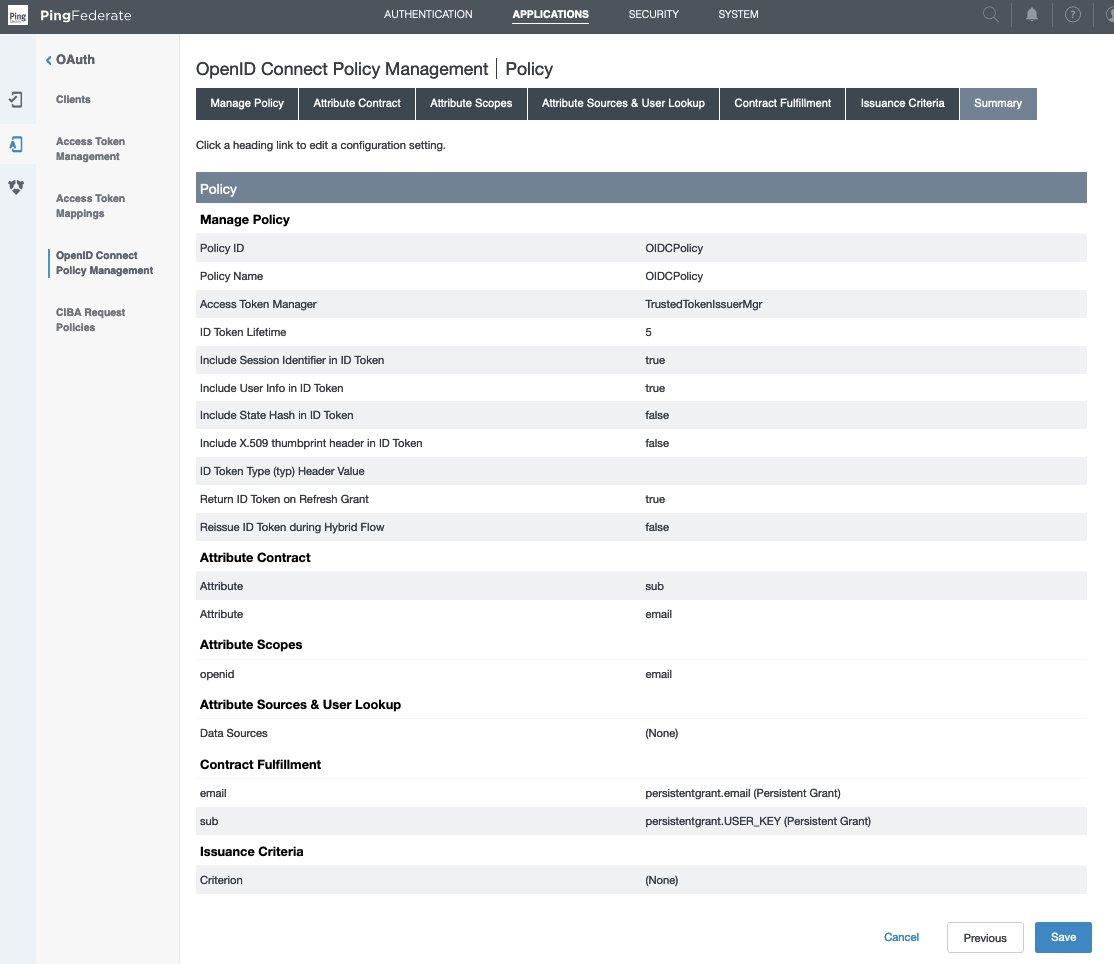
- Within the PingFederate administrative console, go to Purposes > OAuth > OpenID Join Coverage Administration, and select Add Coverage.
- Within the Handle Coverage tab,
- Enter the Coverage ID and Title of your alternative, for instance
OIDCPolicy. - Choose the Entry Token Supervisor from drop down listing created within the earlier part—TrustedTokenIssuerMgr.
- Choose Embody Session Identifier in ID Token
- Choose Embody Consumer Information in ID Token
- Choose Return ID Token on Refresh Grant
- Depart others as is and select Subsequent.
- Enter the Coverage ID and Title of your alternative, for instance
- Within the Attribute Contract tab, hold solely the required attributes in prolonged contract and delete the others.
- Depart the sub attribute beneath Attribute Contract as is.
- Below Lengthen the contract, select delete for all attributes besides electronic mail. select Subsequent.
- Within the Attribute Scopes tab,
- Choose openid from the Scope listing.
- Choose electronic mail from Attributes.
- Select Add from Actions. Select Subsequent.
- Depart Attribute Sources & Consumer Lookup as is and select Subsequent.
- In Contract Success tab,
- For Attribute Contract electronic mail, choose Persistent Grant from the Supply, and Worth as electronic mail.
- For Attribute Contract sub, choose Persistent Grant from the Supply, and Worth as USER_KEY.
- Select Subsequent.
- Depart Issuance Standards as is and select Subsequent.
- On the Abstract tab, evaluation your modifications and select Save. A coverage ID with the title you offered, like OIDCPolicy, seems in Purposes > Oauth > OpenID Join Coverage Administration.
Create OAuth shopper
For full particulars and arrange primarily based in your safety wants, see configure an OAuth shopper in PingFederate, which explains every area intimately. Full the next steps to create an OAuth shopper.
- Within the PingFederate administrative console, go to Purposes > OAuth > Purchasers, and select Add Consumer.
- Within the Consumer ID area, enter a novel, immutable shopper ID. We use
tableauredshiftpingfedbecause the title on this instance. - Enter a Title and Description for the shopper.
- Choose a Consumer Authentication technique. You may choose from None, Consumer TLS Certificates, Personal Key JWT, or Consumer Secret. For this state of affairs, choose Consumer Secret. Select Generate Secret to create a brand new one or use choose Change secret to create your personal.
- Depart Request object signing algorithm set to Enable Any. You may override to make use of the algorithm of your alternative if wanted.
- Within the Redirect URIs area, add every of the next values.
http://localhost:8080/authorization-code/callbackhttp://localhost:55556/Callbackhttp://localhost:55557/Callbackhttp://localhost:55558/Callbackhttp://localhost/auth/add_oauth_token
- Choose Prohibit frequent scopes. Prohibit scopes by deciding on the checkboxes for electronic mail, offline_access, openid, and profile as required.
- In Brand URL, optionally enter the URL for brand you wish to show on the Consumer Grant Authorization and Revocation pages.
- Within the Allowed Grant Sorts listing, you possibly can select from an inventory of authorization choices. On this instance, choose Authorization code. Optionally, you possibly can choose Implicit, Refresh Token, and Consumer Credentials.
- Below Default entry token supervisor, choose the entry token supervisor TrustedTokenIssuerMgr created within the earlier part.
- Choose the Prohibit field for Prohibit to default entry token supervisor.
- Customise Persistent grants max lifetime to match your necessities. Set it to 12 hours for this instance by utilizing the third radio button.
- For Openid join, select your most popular ID token signing algorithm. Choose RSA utilizing SHA-256 for this instance. Optionally, for Coverage you possibly can select the OIDC coverage created within the earlier part.
- Depart the remaining settings as default and select Save.
Determine 5 : OAuth Consumer Configuration
The Tableau Desktop redirect URLs ought to at all times use localhost. The next instance, additionally use localhost for the Tableau Server hostname to simplify testing in a check atmosphere. For this setup, you must also entry the server at localhost within the browser. In a manufacturing atmosphere, or Tableau Cloud, you need to use the complete hostname that your customers will use to entry Tableau on the net, together with HTTPS. If you have already got an atmosphere with HTTPS configured, you possibly can skip the localhost configuration and use the complete hostname from the beginning.
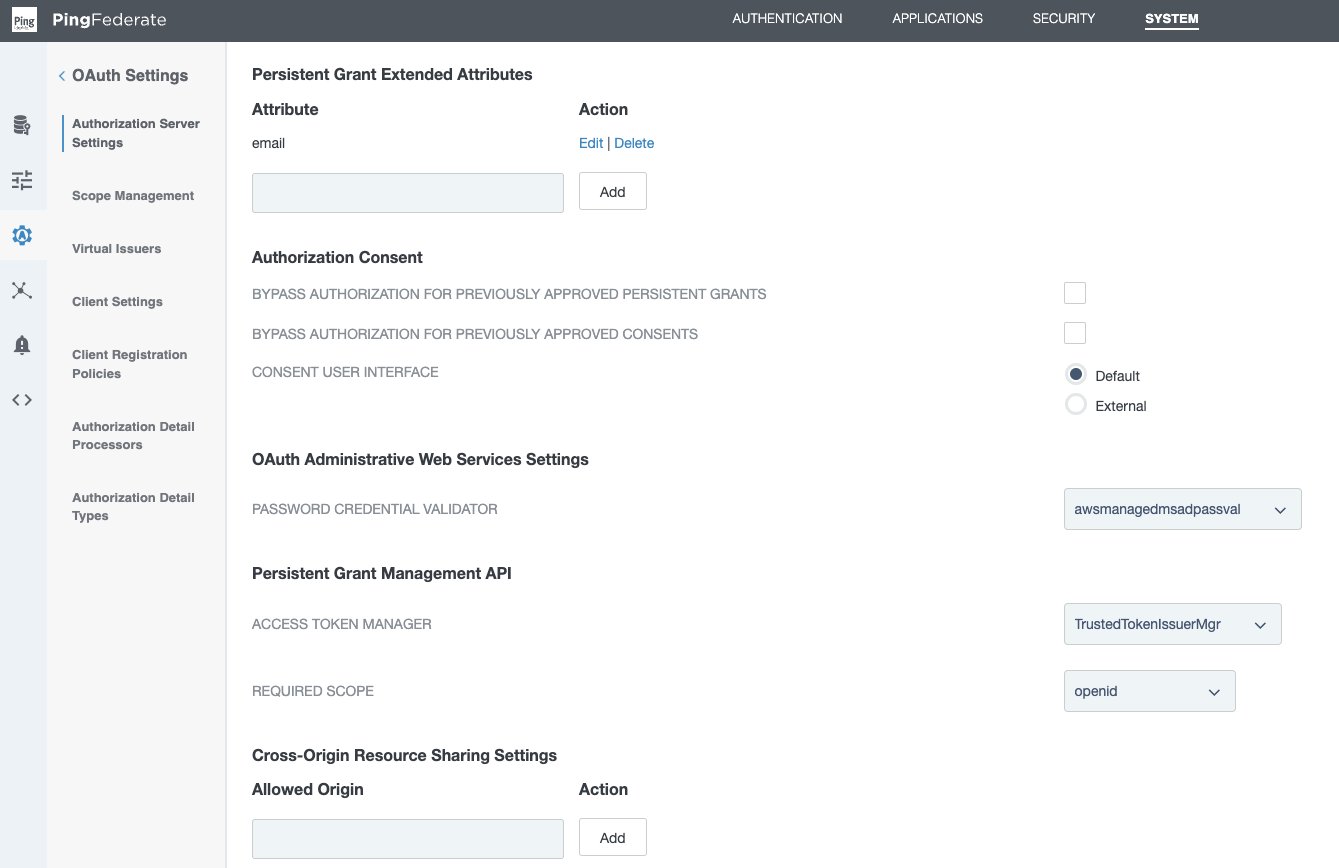
Arrange a PingFederate authorization server
For full particulars and arrange primarily based in your safety wants, see PingFederate authorization server settings in PingFederate. Full the next steps to configure an authorization server.
- Within the PingFederate administrative console, go to System > OAuth Settings > Authorization Server Settings, and make following modifications.
- Depart the preliminary configurations as default and scroll right down to Persistent Grant Prolonged Attributes, add Attribute electronic mail.
- For OAuth Administrative Internet Companies Settings, in Password Credential Validator, choose awsmanagedmsadpassval that you just created within the SAML and SCIM arrange part.
- For Persistent Grant Administration API,
- In Entry Token Supervisor, choose the TrustedTokenIssuerMgr created earlier.
- In Required Scope, choose openid.
- Depart remaining the settings as default and select Save.
Coverage contract grant mapping
For full particulars and arrange primarily based in your safety wants, see Grant contract mapping in PingFederate. For this illustration, we arrange a coverage contract grant mapping for authentication in a three-step course of.
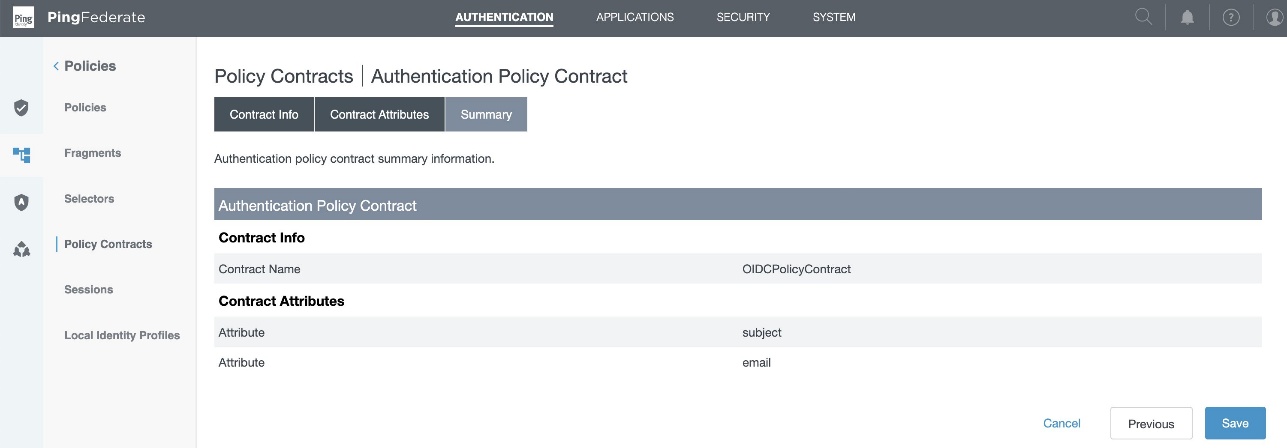
Step 1: Create a coverage contract
- Within the PingFederate administrative console, go to Authentication > Insurance policies > Coverage Contracts, and select Create New Contract.
- In Contract Information tab, enter a reputation. For this instance, we use
OIDCPolicyContract. - In Contract Attributes tab, select Lengthen the Contract so as to add electronic mail attribute.
- Assessment and select Save.
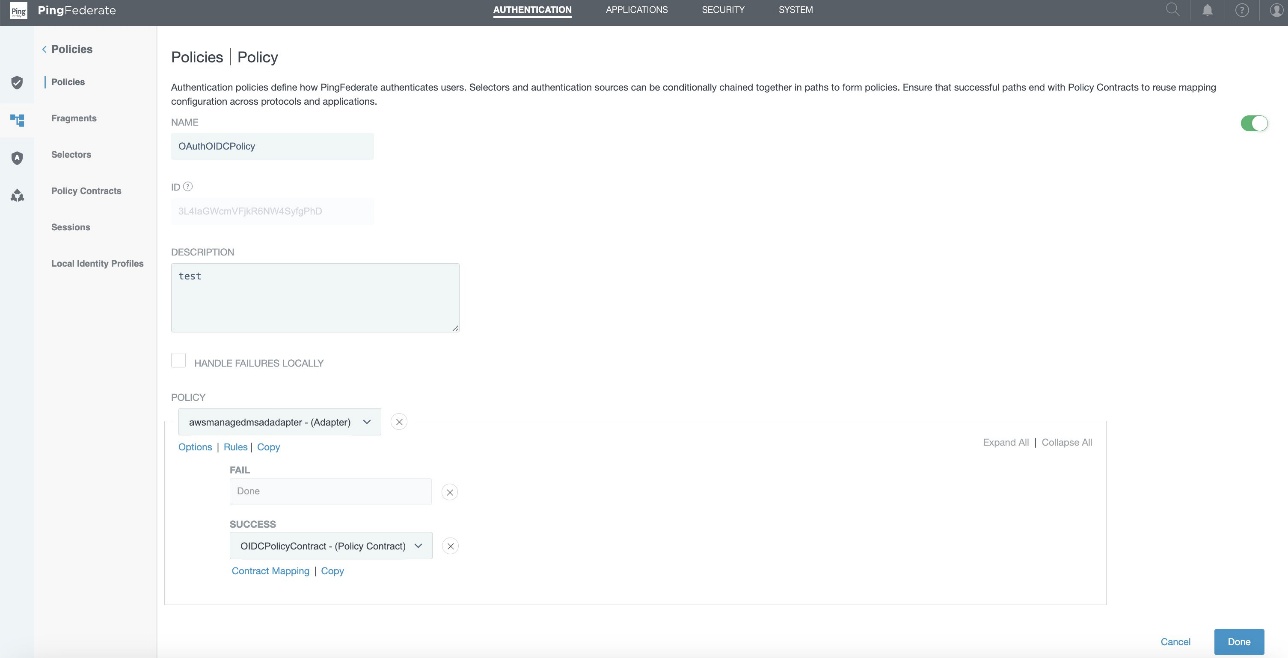
Step 2: Add authentication coverage
- Within the PingFederate administrative console, go to Authentication > Insurance policies > Insurance policies, and select Add Coverage.
- Enter a coverage title. On this instance, we use
OAuthOIDCPolicy. - Within the Coverage drop down, choose IdP Adapter and choose the awsmanagedmsadadapter that you just created within the SAML and SCIM arrange part.
- Set FAIL to Finished and beneath SUCCESS, choose Coverage Contracts from the drop-down menu and choose the OIDCPolicyContract created in step 1. Select Finished.
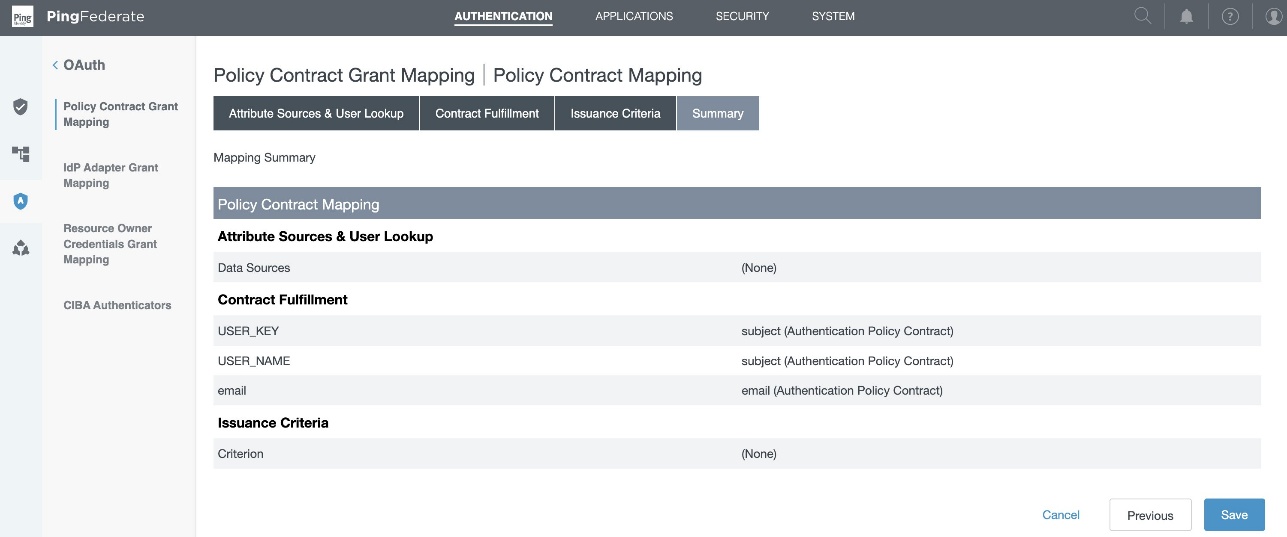
Step 3: Coverage contract grant mapping
- Within the PingFederate administrative console, go to Authentication > OAuth > Coverage Contract Grant Mapping, and beneath Mappings, choose OIDCPolicyContract created in Step1 and select Add Mapping.
- On the Attribute Sources & Consumer Lookup tab, select Subsequent.
- Within the Contract Success tab,
- For Contract USER_KEY, choose Authentication Coverage Contract from the Supply, and Worth as topic.
- For Contract USER_NAME, choose Authentication Coverage Contract from the Supply, and Worth as topic.
- For Contract electronic mail, choose Authentication Coverage Contract from the Supply, and Worth as electronic mail.
- Select Subsequent.
- Depart Issuance Standards as is, evaluation and select Save.
Gather PingFederate data
To configure your PingFederate with IAM Identification Middle and Amazon Redshift, gather the next parameters. When you don’t have these parameters, contact your PingFederate admin.
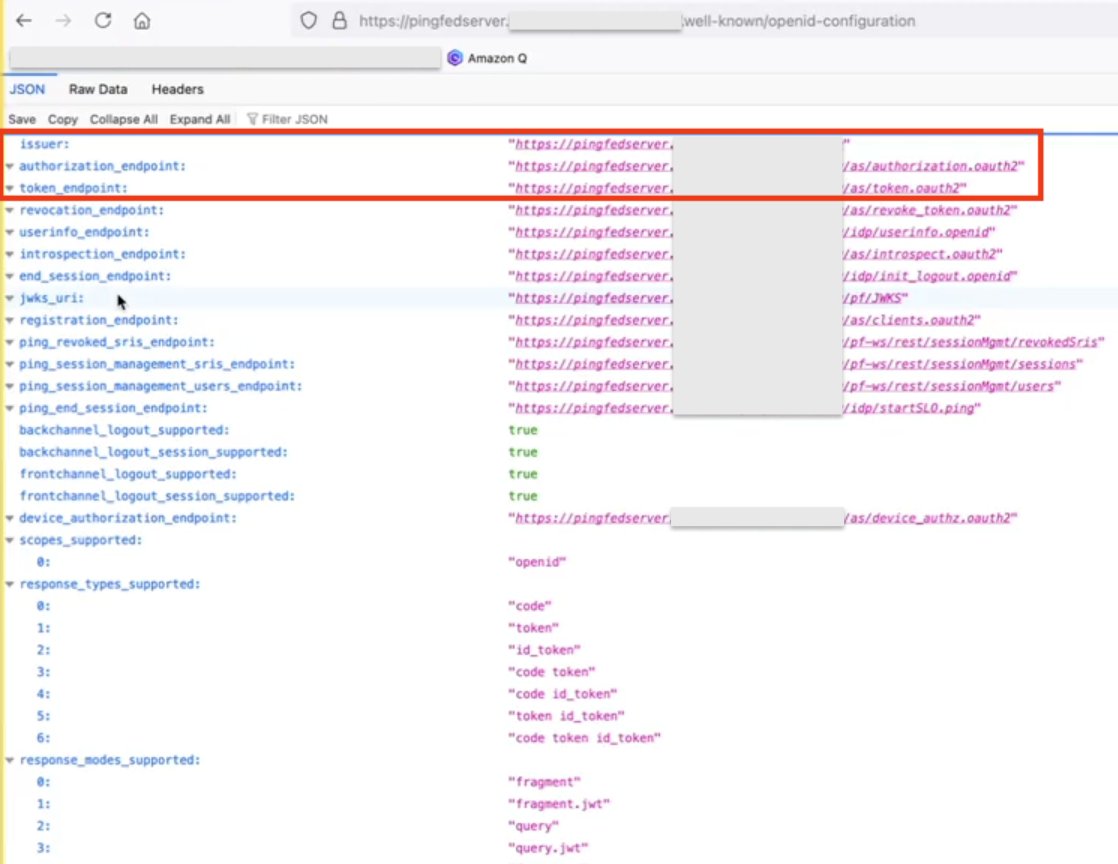
- Issuer URL, auth URL (authUri), and token URL (tokenUri).
You may get these values from the OIDC IdP URL: https://pingfedserver.instance.com/.well-known/openid-configuration. Open this URL in an internet browser, changing pingfedserver.instance.com along with your IdP server title.
The next is an instance screenshot of IdP attributes utilizing OIDC IdP URL the place:
- The issuer URL corresponds to the issuer
- The auth URL (authUri) corresponds to
authorization_endpoint - The token URL (tokenUri) corresponds to
token_endpoint
- Viewers worth
To get the Viewers worth from PingFederate, register as an admin to PingFederate and navigate to the next path to get the viewers worth that you just created throughout entry token mapping creation in PingFederate:
Purposes > OAuth > Entry Token Mappings > TrustedTokenIssuerMgr → Abstract > aud
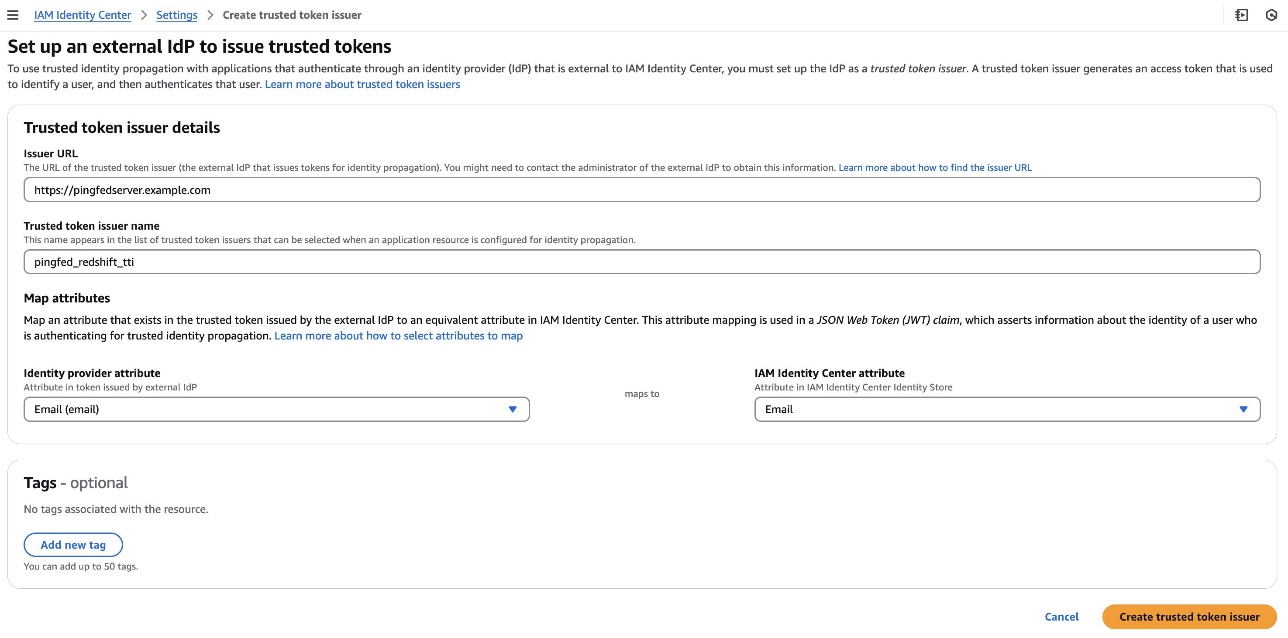
Arrange a trusted token issuer in IAM Identification Middle
Swap from the PingFederate console to the IAM Identification Middle console for the AWS facet of configuration. Begin by including a trusted token issuer (TTI), which makes it potential to authorize Tableau to make requests on behalf of their customers to entry knowledge in Amazon Redshift. A TTI is an OAuth 2.0 authorization server that points tokens to purposes that provoke requests (requesting purposes). The tokens authorize these purposes to provoke requests on behalf of their customers to a receiving utility (an AWS service). On this step, you create a TTI within the central administration account. To create a TTI,
- Open the AWS Administration Console and navigate to IAM Identification Middle, after which to the Settings web page.
- Choose the Authentication tab and beneath Trusted token issuers, select Create trusted token issuer.
- On the Arrange an exterior IdP to subject trusted tokens web page, beneath Trusted token issuer particulars, do the next:
- For Issuer URL, enter the OIDC discovery URL of the exterior IdP that can subject tokens for trusted identification propagation. You may get issuer the URL as talked about in step 1 of the previous part Gather PingFederate data.
- For Trusted token issuer title, enter a reputation to determine this TTI in Identification Middle and within the utility console.
- Below Map attributes, do the next:
- For the identification supplier attribute, choose an attribute from the listing to map to an attribute within the Identification Middle identification retailer. You may choose E mail, Object Identifier, Topic, and Different.
- For Identification Middle attribute, choose the corresponding attribute for the attribute mapping.
- Below Tags (non-obligatory), select Add new tag, enter a worth for Key, and optionally for Worth. For details about tags, see Tagging AWS IAM Identification Middle assets.
The next determine reveals the arrange for TTI:
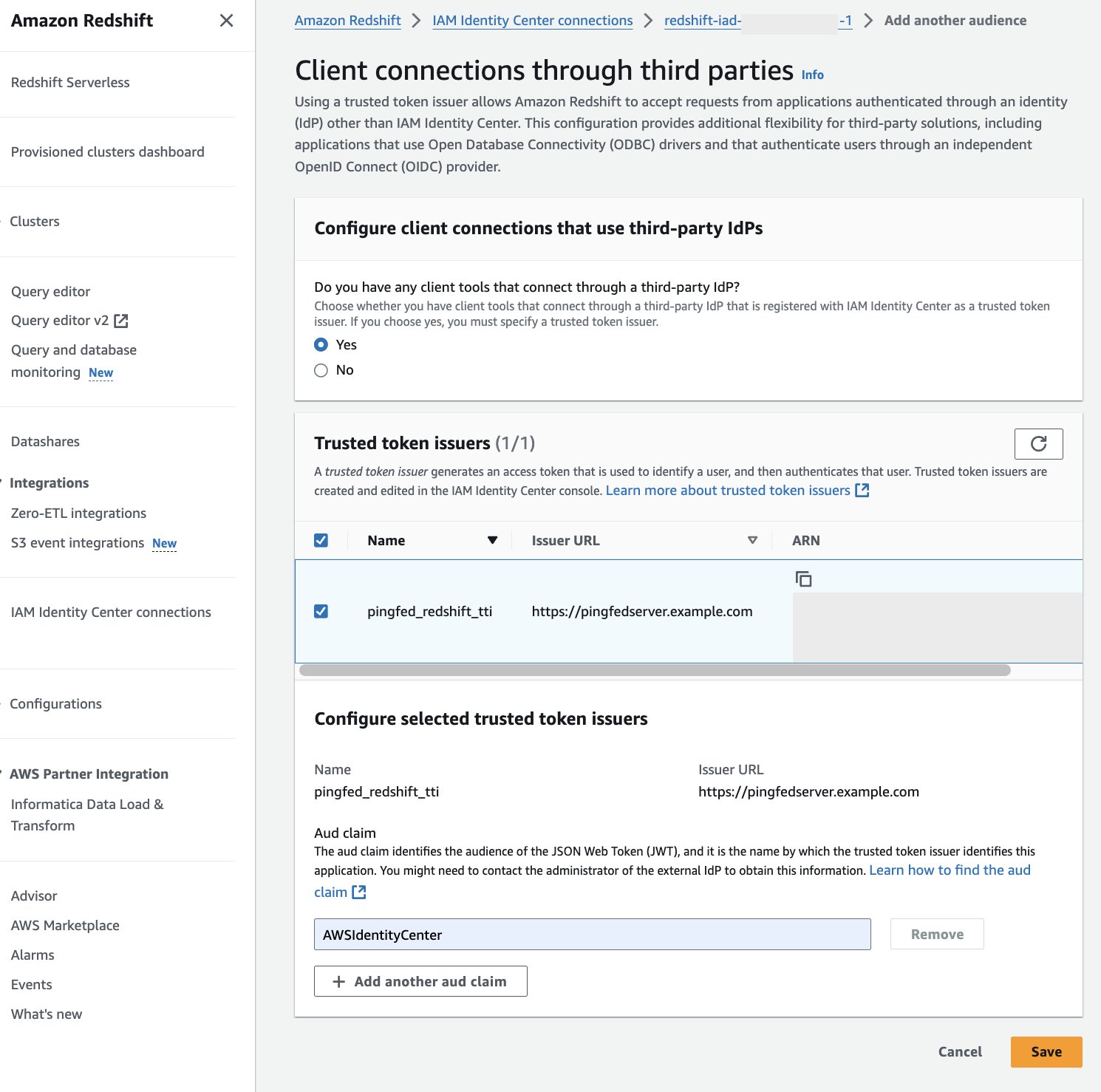
Arrange shopper connections and trusted token issuers in Amazon Redshift
On this step, the Amazon Redshift purposes that trade externally generated tokens have to be configured to make use of the TTI you created within the earlier step. Additionally, the viewers declare (or aud declare) from PingFederate have to be specified. On this instance, you might be configuring the Amazon Redshift utility within the member account the place the Amazon Redshift cluster or serverless occasion exists.
- Choose IAM Identification Middle connection from the Amazon Redshift console menu.
- Choose the Amazon Redshift utility that you just created as a part of the stipulations.
- Choose the Consumer connections tab and select Edit.
- Select Sure beneath Configure shopper connections that use third-party IdPs.
- Choose the checkbox for Trusted token issuer that you just created within the earlier part.
- Enter the Aud declare worth beneath Configure chosen trusted token issuers. For instance,
AWSIdentityCenter. You may get the viewers worth from the PingFederate path: Purposes > OAuth > Entry Token Mappings > TrustedTokenIssuerMgr > Abstract > aud. - Select Save.
At this level, your IAM Identification Middle, Amazon Redshift, and PingFederate configuration are full. Subsequent, it’s essential to configure Tableau.
Configure Tableau OAuth config information for PingFederate to combine with Amazon Redshift utilizing IAM Identification Middle
This XML file used on this part might be used for all of the Tableau merchandise like Tableau Desktop, Server and Cloud.
To combine Tableau with Amazon Redshift utilizing IAM Identification Middle, it’s essential to use a customized XML file. On this step, you’ll use the next XML and exchange the values beginning with a $ signal and highlighted in daring. The remainder of the values might be saved as it’s or you possibly can modify them primarily based in your particular wants. For detailed data on every of the weather within the file, see the Tableau documentation on GitHub.
You may get authUri and tokenUri as talked about in step 1 of previous part, Gather PingFederate data.
The next is the instance XML:
Set up Tableau OAuth config file on a shopper machine for Tableau Desktop
After the XML configuration file is created, it must be copied to a particular location for use by Amazon Redshift Connector from Tableau Desktop. Save the previous file as .xml and put it aside beneath DocumentsMy Tableau RepositoryOAuthConfigs.
Word: At present this integration isn’t supported in macOS as a result of the Amazon Redshift ODBC 2.X Driver isn’t supported but for MAC.
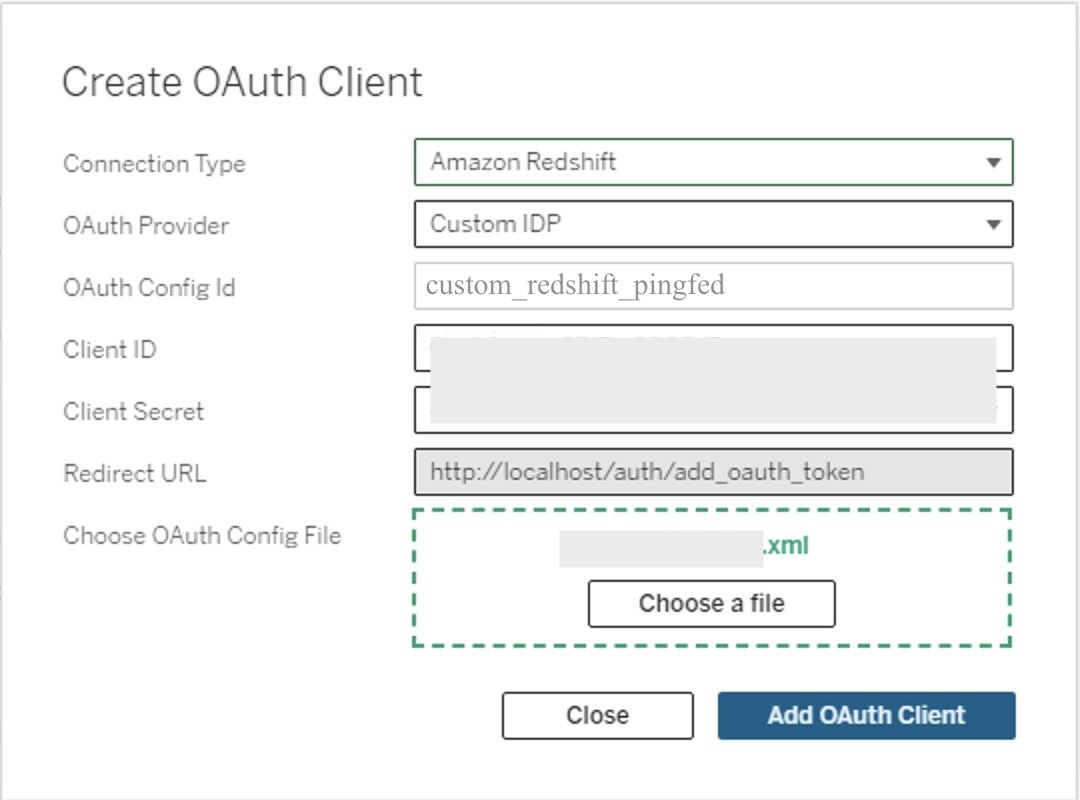
Set up Tableau OAuth config file for a website on Tableau Server or Tableau Cloud
To combine with Amazon Redshift utilizing IAM Identification Middle authentication, it’s essential to set up the Tableau OAuth config file in Tableau Server or Tableau Cloud.
- Register to the Tableau Server or Tableau Cloud utilizing admin credentials.
- Navigate to Settings.
- Go to OAuth Purchasers Registry and choose Add OAuth Consumer.
- Select the next settings:
- Connection kind: Choose Amazon Redshift.
- OAuth Supplier: Choose Custom_IdP.
- Consumer ID: Enter your IdP shopper ID worth.
- Consumer Secret: Enter your shopper secret worth.
- Redirect URL: Enter the worth as
http://localhost/auth/add_oauth_token. On this submit, we’re utilizing localhost for testing within the native atmosphere. It’s best to ideally use the complete hostname with https. - Select OAuth Config File: Choose the XML file that you just configured in Configure Tableau Desktop.
- Choose Add OAuth Consumer and select Save.
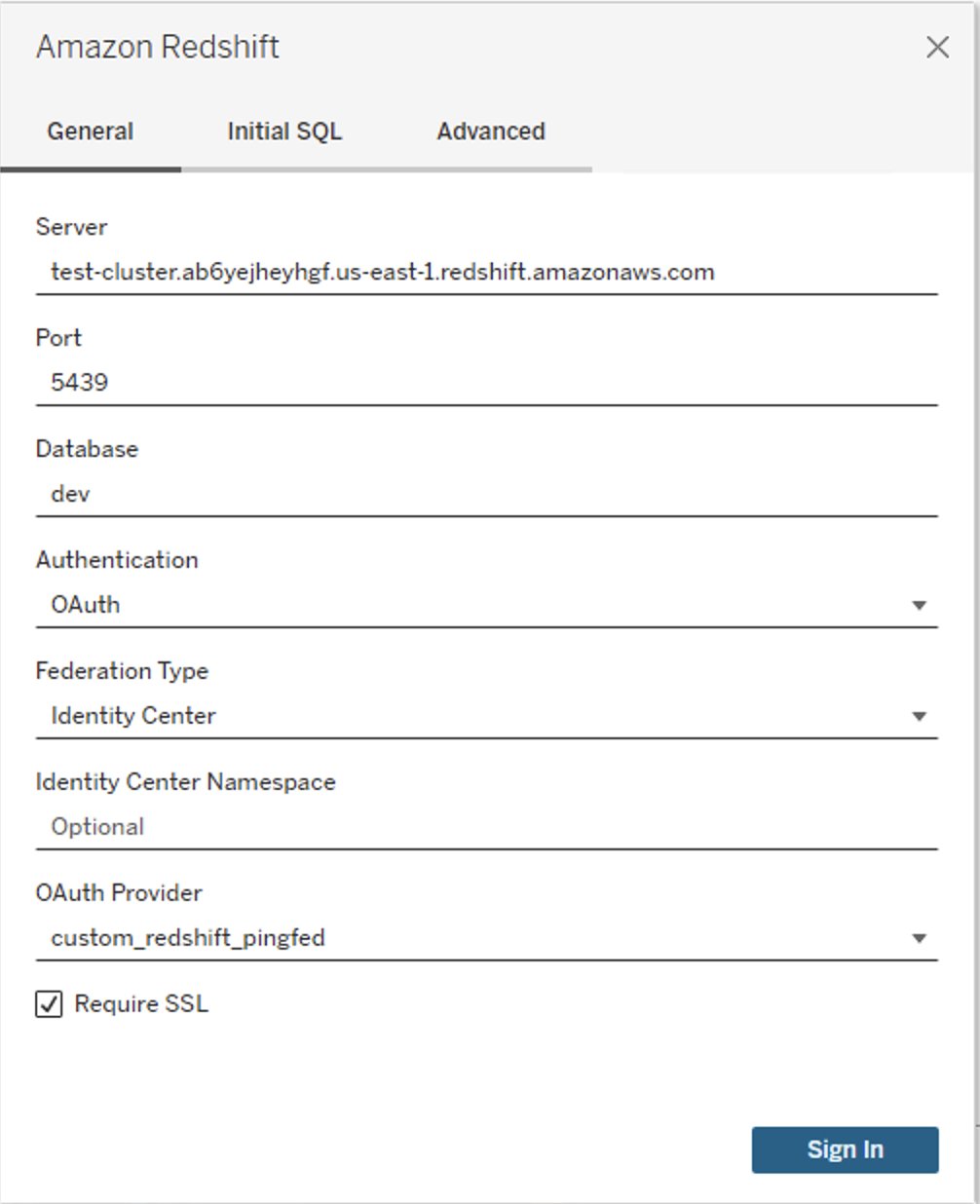
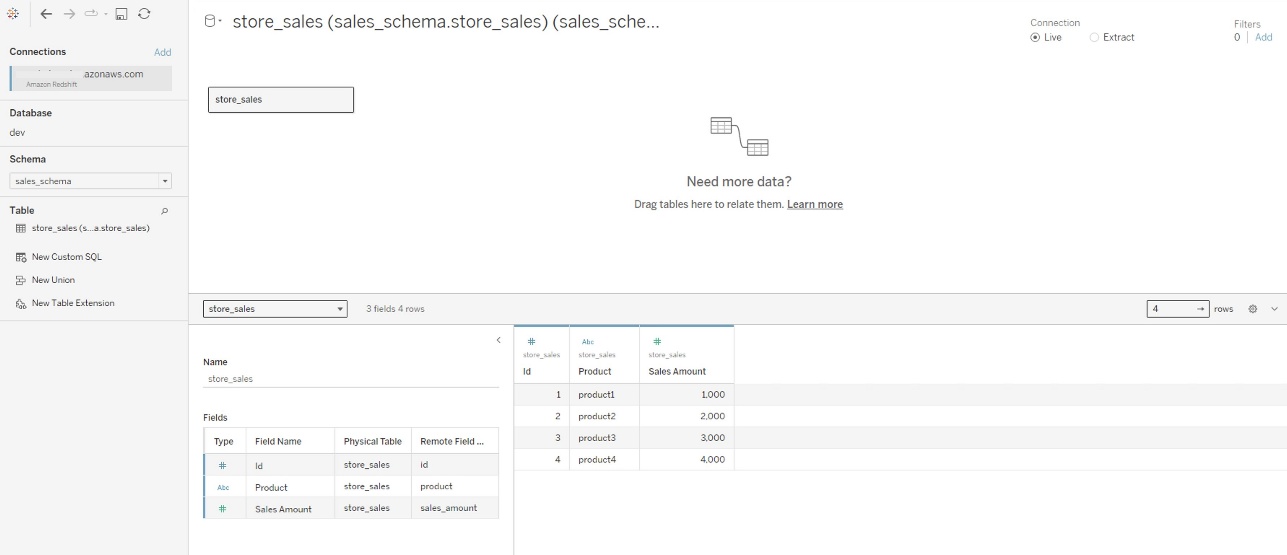
Federate to Amazon Redshift from Tableau Desktop utilizing IAM Identification Middle
Now, you’re prepared to attach from Tableau and federated sign-in utilizing IAM Identification Middle authentication. On this step, you’ll create a Tableau Desktop report and publish it to Tableau Server.
- Open Tableau Desktop.
- Select Amazon Redshift Connector and enter the next values:
- Server: Enter the title of the server that hosts the database and the title of the database you wish to hook up with.
- Port: Enter
5439. - Database: Enter your database title. On this instance, we use
dev. - Authentication: Choose OAuth.
- Federation Sort: Choose Identification Middle
- Identification Middle Namespace: You may go away this clean.
- OAuth Supplier: This worth ought to robotically be pulled out of your configured XML. Will probably be the worth from the factor
oauthConfigId. - Choose checkbox for Require SSL.
- Select Signal-In.
- A browser pop-up will provoke the place you’ll enter your IdP credentials.
- When authentication is profitable, you will notice the message Tableau created this window to authenticate. It’s now protected to shut it.
Congratulations! You’re signed in utilizing the IAM Identification Middle integration with Amazon Redshift and are able to discover and analyze your knowledge utilizing Tableau Desktop.
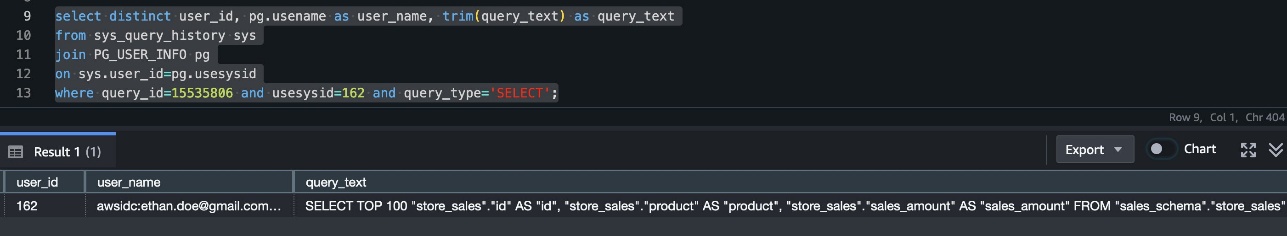
The next is a screenshot from Amazon Redshift system desk (sys_query_history) displaying that person Ethan from PingFederate is accessing the gross sales report.
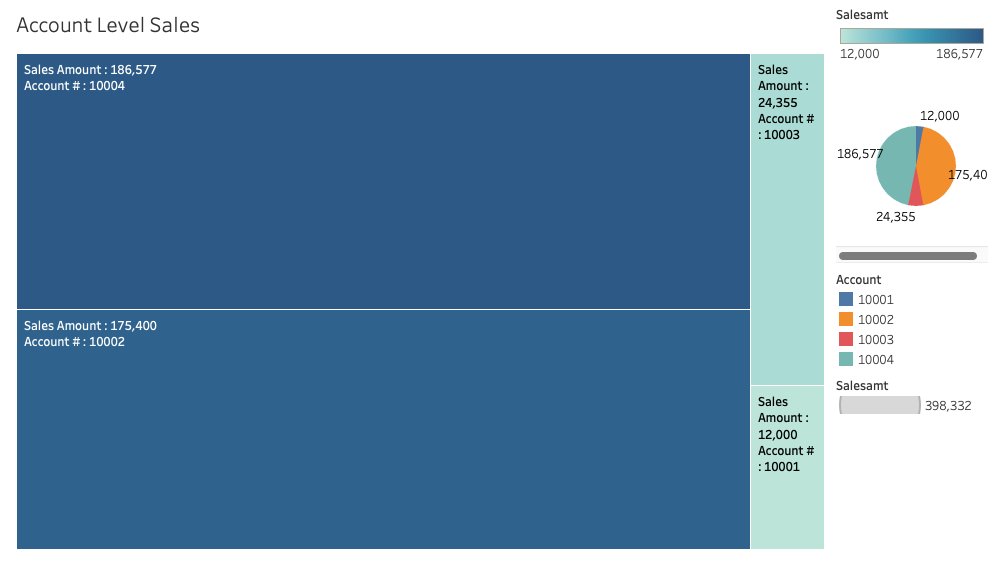
Now you possibly can create your personal Tableau Report on the desktop model and publish it to your Tableau Server. For the subsequent part, you create and publish a report named Account Degree Gross sales.
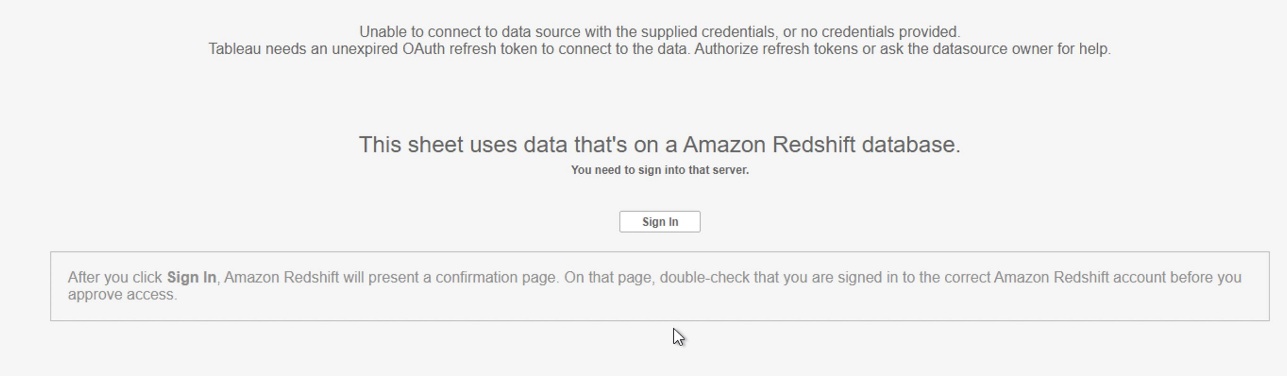
Federate to Amazon Redshift from Tableau Server utilizing IAM Identification Middle authentication
After you have got revealed the report from Tableau Desktop to Tableau Server, register as non-admin person and consider the revealed report utilizing IAM Identification Middle authentication.
- Register to the Tableau Server website as a non-admin person.
- Navigate to Discover and go to the folder the place your revealed report is saved.
- Choose the report and select Signal In.
- Enter your PingFederate credentials to the browser pop-up to authenticate.
- After profitable authentication, you possibly can entry the information and create reviews.
Clear up
Full the next steps to scrub up your assets:
- Delete the IdP purposes that you just created to combine with IAM Identification Middle.
- Delete Identification Middle configuration.
- Delete the Amazon Redshift utility and the Amazon Redshift provisioned cluster or Serverless occasion that you just created for testing.
- Delete the IAM position and IAM coverage that you just created for Identification Middle and Amazon Redshift integration.
- Delete the permission set from Identification Middle that you just created for Amazon Redshift Question Editor v2 within the administration account.
- Clear up assets associated to PingFederate.
Conclusion
This submit coated streamlining entry administration for knowledge analytics by utilizing Tableau’s functionality to help single sign-on primarily based on the OAuth 2.0 and OIDC protocol. This setup facilitates federated person authentication, the place person identities from an exterior identification supplier like PingFederate are trusted and propagated to Amazon Redshift. You walked by means of the steps to configure Tableau Desktop and Tableau Server to combine seamlessly with Amazon Redshift utilizing AWS IAM Identification Middle for single sign-on. By harnessing this integration of a third-party IdP with IAM Identification Middle, analysts can securely entry Amazon Redshift knowledge sources inside Tableau with out managing separate database credentials.
Study extra about Amazon Redshift integration with IAM Identification Middle utilizing PingFederate as an identification supplier by visiting the next assets.