Amazon Redshift is a robust cloud-based information warehouse that organizations can use to investigate each structured and semi-structured information via superior SQL queries. As a totally managed service, it offers excessive efficiency and scalability whereas permitting safe entry to the info saved within the information warehouse. Organizations worldwide depend on Amazon Redshift to deal with huge datasets, improve their analytics capabilities, and ship precious enterprise intelligence to their stakeholders.
AWS IAM Id Middle serves as the popular platform for controlling workforce entry to AWS instruments, together with Amazon Q Developer. It permits for a single connection to your current id supplier (IdP), making a unified view of customers throughout AWS purposes and making use of trusted id propagation for a easy and constant expertise.
You may entry information in Amazon Redshift utilizing native customers or exterior customers. An area consumer in Amazon Redshift is a database consumer account that’s created and managed straight throughout the Redshift cluster itself. Amazon Redshift additionally integrates with IAM Id Middle, and helps trusted id propagation, so you should utilize third-party IdPs reminiscent of Microsoft Entra ID (Azure AD), Okta, Ping, OneLogin, or use IAM Id Middle as an id supply. The IAM Id Middle integration with Amazon Redshift helps centralized authentication and SSO capabilities, simplifying entry administration throughout multi-account environments. As organizations develop in scale, it is suggested to make use of exterior customers for cross-service integration and centralized entry administration.
On this submit, we stroll you thru the method of easily migrating your native Redshift consumer administration to IAM Id Middle customers and teams utilizing the RedshiftIDCMigration utility.
Resolution overview
The next diagram illustrates the answer structure.
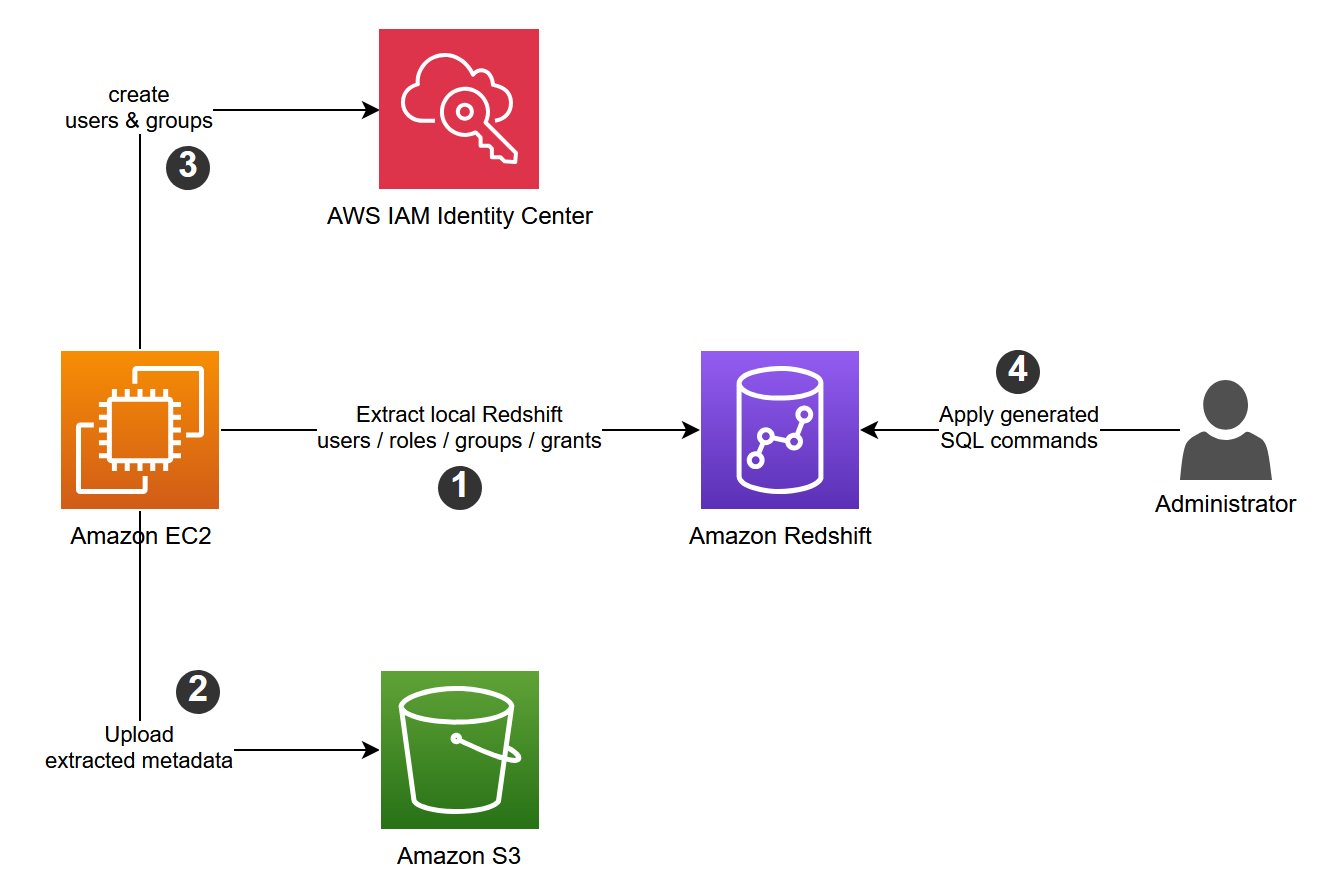
The RedshiftIDCMigration utility accelerates the migration of your native Redshift customers, teams, and roles to your IAM Id Middle occasion by performing the next actions:
- Create customers in IAM Id Middle for each native consumer in a given Redshift occasion.
- Create teams in IAM Id Middle for each group or position in a given Redshift occasion.
- Assign customers to teams in IAM Id Middle in keeping with current assignments within the Redshift occasion.
- Create IAM Id Middle roles within the Redshift occasion matching the teams created in IAM Id Middle.
- Grant permissions to IAM Id Middle roles within the Redshift occasion based mostly on the present permissions given to native teams and roles.
Conditions
Earlier than operating the utility, full the next stipulations:
- Allow IAM Id Middle in your account.
- Comply with the steps within the submit Combine Id Supplier (IdP) with Amazon Redshift Question Editor V2 and SQL Consumer utilizing AWS IAM Id Middle for seamless Single Signal-On (particularly, observe Steps 1–8, skipping Steps 4 and 6).
- Configure the IAM Id Middle utility assignments:
- On the IAM Id Middle console, select Utility Assignments and Functions.
- Choose your utility and on the Actions dropdown menu, select Edit particulars.
- For Consumer and group assignments, select Don’t require assignments. This setting makes it potential to check Amazon Redshift connectivity with out configuring particular information entry permissions.
- Configure IAM Id Middle authentication with administrative entry from both Amazon Elastic Compute Cloud (Amazon EC2) or AWS CloudShell.
The utility will likely be run from both an EC2 occasion or CloudShell. In the event you’re utilizing an EC2 occasion, an IAM position is hooked up to the occasion. Make it possible for the IAM position used throughout the execution has the next permissions (if not, create a brand new coverage with these permissions and fasten it to the IAM position):
- Amazon Redshift permissions (for serverless):
- Amazon Redshift permissions (for provisioned):
- Id retailer permissions:
Artifacts
Obtain the next utility artifacts from the GitHub repo:
- idc_redshift_unload_indatabase_groups_roles_users.py – A Python script to unload customers, teams, roles and their associations.
- redshift_unload.ini – The config file used within the previous script to learn Redshift information warehouse particulars and Amazon S3 places to unload the recordsdata.
- idc_add_users_groups_roles_psets.py – A Python script to create customers and teams in IAM Id Middle, after which affiliate the customers to teams in IAM Id Middle.
- idc_config.ini – The config file used within the previous script to learn IAM Id Middle particulars.
- vw_local_ugr_to_idc_urgr_priv.sql – A script that generates SQL statements that carry out two duties in Amazon Redshift:
- Create roles that precisely match your IAM Id Middle group names, including a specified prefix.
- Grant acceptable permissions to those newly created Redshift roles.
Testing situation
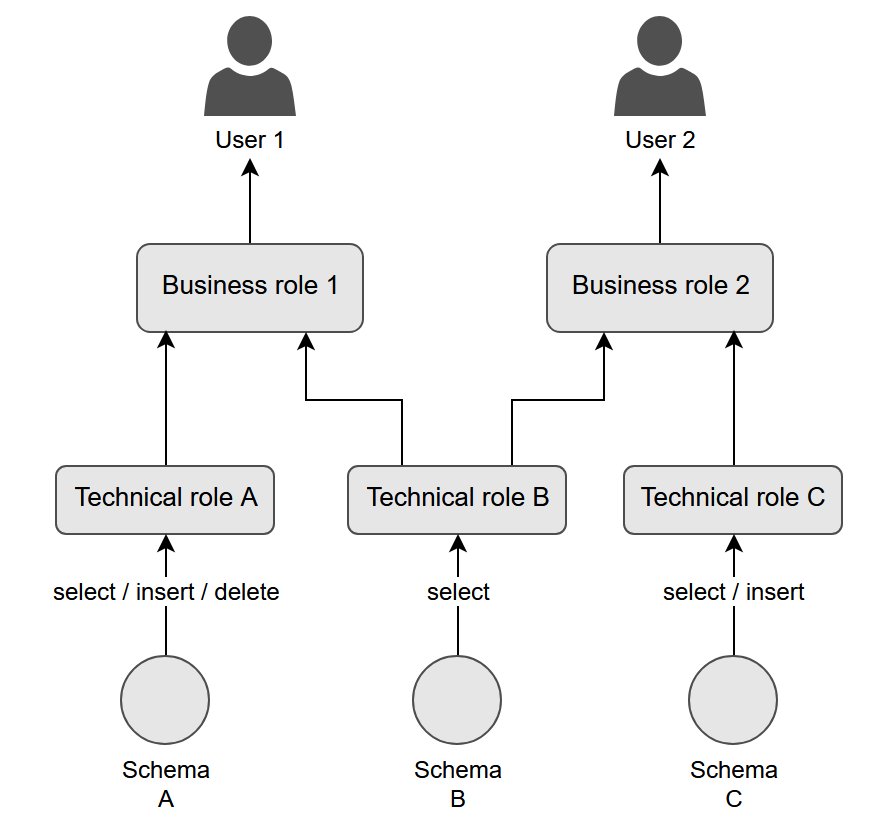
This check case is designed to supply sensible expertise and familiarize you with the utility’s performance. The situation is structured round a hierarchical nested roles system, beginning with object-level permissions assigned to technical roles. These technical roles are then allotted to enterprise roles. Lastly, enterprise roles are granted to particular person customers. To boost the testing atmosphere, the situation additionally incorporates a consumer group.The next diagram illustrates this hierarchy.
Create datasets
Arrange two separate schemas (tickit and tpcds) in a Redshift database utilizing the create schema command. Then, create and populate a number of tables in every schema utilizing the tickit and tpcds pattern datasets.
Specify the suitable IAM position Amazon Useful resource Identify (ARN) within the copy instructions if crucial.
Create customers
Create customers with the next code:
Create enterprise roles
Create enterprise customers with the next code:
Create technical roles
Create technical roles with the next code:
Create teams
Create teams with the next code:
Grant rights to technical roles
To grant rights to the technical roles, use the next code:
Grant technical roles to enterprise roles
To grant the technical roles to the enterprise roles, use the next code:
Grant enterprise roles to customers
To grant the enterprise roles to customers, use the next code:
Grant rights to teams
To grant rights to the teams, use the next code:
Add customers to teams
So as to add customers to the teams, use the next code:
Deploy the answer
Full the next steps to deploy the answer:
- Replace Redshift cluster or serverless endpoint particulars and Amazon S3 location in
redshift_unload.ini:- cluster_type =
provisionedorserverless - cluster_id =
${cluster_identifier}(required ifcluster_typeisprovisioned) - db_user =
${database_user} - db_name =
${database_name} - host =
${host_url}(required ifcluster_typeisprovisioned) - port =
${port_number} - workgroup_name =
${workgroup_name}(required ifcluster_typeisserverless) - area =
${area} - s3_bucket =
${S3_bucket_name} - roles =
roles.csv - customers =
customers.csv - role_memberships =
role_memberships.csv
- cluster_type =
- Replace IAM Id Middle particulars in
idc_config.ini:- area =
${area} - account_id =
${account_id} - identity_store_id =
${identity_store_id}(out there on the IAM Id Middle console Settings web page) - instance_arn =
${iam_identity_center_instance_arn}(out there on the IAM Id Middle console Settings web page) - permission_set_arn =
${permission_set_arn} - assign_permission_set =
TrueorFalse(Trueifpermission_set_arnis outlined) - s3_bucket =
${S3_bucket_name} - users_file =
customers.csv - roles_file =
roles.csv - role_memberships_file =
role_memberships.csv
- area =
- Create a listing in CloudShell or by yourself EC2 occasion with connectivity to Amazon Redshift.
- Copy the 2 .ini recordsdata and obtain the Python scripts to that listing.
- Run
idc_redshift_unload_indatabase_groups_roles_users.pyboth from CloudShell or your EC2 occasion:python idc_redshift_unload_indatabase_groups_roles_users.py - Run
idc_add_users_groups_roles_psets.pyboth from CloudShell or your EC2 occasion:python idc_add_users_groups_roles_psets.py - Join your Redshift cluster utilizing the Amazon Redshift question editor v2 or most well-liked SQL consumer, utilizing superuser credentials.
- Copy the SQL within the
vw_local_ugr_to_idc_urgr_priv.sqlfile and run it within the question editor to create thevw_local_ugr_to_idc_urgr_privview. - Run following SQL command to generate the SQL statements for creating roles and permissions:
For instance, think about the next current grants:
These grants are transformed to the next code:
- Overview the statements within the
idc_based_grantscolumn.
This won’t be a complete listing of permissions, so evaluation them fastidiously. - If every part is right, run the statements from the SQL consumer.
When you’ve accomplished the method, it is best to have the next configuration:
- IAM Id Middle now incorporates newly created customers from Amazon Redshift
- The Redshift native teams and roles are created as teams in IAM Id Middle
- New roles are established in Amazon Redshift, comparable to the teams created in IAM Id Middle
- The newly created Redshift roles are assigned acceptable permissions
In the event you encounter a difficulty whereas connecting to Amazon Redshift with the question editor utilizing IAM Id Middle, check with Troubleshooting connections from Amazon Redshift question editor v2.
Concerns
Take into account the next when utilizing this resolution:
- On the time of writing, creating permissions in AWS Lake Formation is just not in scope.
- IAM Id Middle and IdP integration setup is out of scope for this utility. Nonetheless, you should utilize the view
vw_local_ugr_to_idc_urgr_priv.sqlto create roles and grant permissions to the IdP customers and teams handed via IAM Id Middle. - When you have permissions given on to native consumer IDs (not utilizing teams or roles), you will need to change that to a role-based permission strategy for IAM Id Middle integration. Create roles and supply permissions utilizing roles as a substitute of straight giving permissions to customers.
Clear up
When you have accomplished the testing situation, clear up your atmosphere:
- Take away the brand new Redshift roles that have been created by the utility, comparable to the teams established in IAM Id Middle.
- Delete the customers and teams created by the utility inside IAM Id Middle.
- Delete the customers, teams, and roles specified within the testing situation.
- Drop the
tickitandtpcdsschemas.
You should use the FORCE parameter when dropping the roles to take away related assignments.
Conclusion
On this submit, we confirmed easy methods to migrate your Redshift native consumer administration to IAM Id Middle. This transition affords a number of key benefits in your group, reminiscent of simplified entry administration via centralized consumer and group administration, a streamlined consumer expertise throughout AWS companies, and decreased administrative overhead. You may implement this migration course of step-by-step, so you possibly can check and validate every step earlier than absolutely transitioning your manufacturing atmosphere.
As organizations proceed to scale their AWS infrastructure, utilizing IAM Id Middle turns into more and more precious for sustaining safe and environment friendly entry administration, together with Amazon SageMaker Unified Studio for an built-in expertise for all of your information and AI.

