On this weblog, you’ll be taught extra about how the Microsoft Safe Future Initiative (SFI)—a real-world case research on Zero Belief—aligns with Zero Belief methods. We’ll share key updates from the April 2025 SFI progress report and sensible Zero Belief steerage that will help you strengthen your group’s safety posture. Whether or not you’re trying to improve safety, cut back danger, or future-proof your setting, this weblog presents actionable insights to assist your journey towards a safer future.
The Zero Belief safety mannequin presents longstanding, confirmed advantages. Zero Belief minimizes the assault floor and makes it considerably tougher for cyberattackers to achieve illicit entry, whether or not from outdoors or inside a company’s community. Zero Belief can also be nice at securing hybrid and distant work environments, serving to to facilitate safe modernization efforts. Microsoft strongly believes in these advantages and works diligently to share assets, insights, and instruments like Zero Belief workshops with prospects. As Microsoft innovates within the Zero Belief area, it shares insights with the expertise {industry} and its prospects.
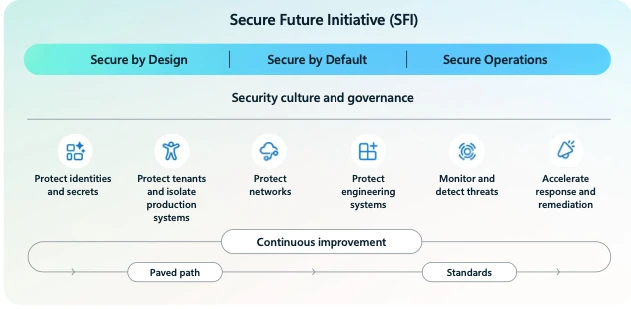
In November of 2023, we launched the Safe Future Initiative—a multiyear effort to revolutionize the best way we design, construct, take a look at, and function our services with a view to obtain the best safety requirements. In Could 2024, Microsoft expanded the Safe Future Initiative to incorporate six engineering pillars and 28 aligned targets. Engineering house owners have been assigned to every pillar and established an preliminary physique of labor to advance every goal, articulated as requirements and measured as key outcomes. In lots of circumstances, these targets and requirements are stringent functions of Zero Belief for Microsoft’s distinctive necessities as a number one hyper-scale cloud operator, supplier of cloud providers and merchandise, and as a serious enterprise goal for unhealthy actors.
Zero Belief: What it means for you
Zero Belief assumes cyberattackers can come from anyplace—inside or outdoors your community. Which means you should “by no means belief, at all times confirm.” In follow, it additionally means each entry request should be authenticated, licensed, and constantly validated—supplying you with better confidence that solely the appropriate folks and gadgets can hook up with your assets.
How Microsoft helps you set Zero Belief into motion
- Confirmed steerage and collaboration: We align with the Nationwide Institute of Requirements and Expertise (NIST), The Open Group, the Cybersecurity and Infrastructure Safety Company (CISA), MITRE, and others, serving to our prospects profit from industry-standard frameworks and greatest practices.
- Finish-to-end deployment assist: From planning to rollout, Microsoft consultants, instruments, and companion ecosystem information prospects by means of every of our six safety pillars: identities, endpoints, functions, infrastructure, community, and information.
- AI-ready safety: We’ve prolonged Zero Belief to cowl AI workloads and fashions, embedding Microsoft options and governance controls at each layer, so our prospects can innovate confidently.
With this complete method from Microsoft, prospects don’t simply be taught the ideas—they achieve the flexibility to use them throughout their setting to assist cut back danger, simplify operations, and speed up safe modernization.
Learnings from the Safe Future Initiative on your Zero Belief journey
Microsoft processes greater than 84 trillion safety alerts day by day—from gadgets and endpoints to cloud providers and functions—giving us strong visibility into rising cyberthreats and assault patterns.1 By integrating information and insights with a “by no means belief, at all times confirm” method, the Safe Future Initiative at Microsoft builds on established Zero Belief methods—turning structure into sensible implementation. Insights from this expertise can allow you to expedite your Zero Belief implementations.
Key insights from SFI
The journey Microsoft has gone on whereas implementing the Safe Future Initiative surfaced these sensible classes: use them to speed up your individual safety enhancements.
Lesson 1: Set priorities and measure progress
Primarily based on our priorities, we developed six pillars and 28 targets to assist us deal with what really issues. You are able to do likewise: analyze your prime dangers, then group them right into a set of measurable targets. This offers your staff a transparent roadmap and helps prioritize efforts that transfer the needle.
Lesson 2: Align tradition with safety targets
We discovered that instruments alone don’t stick—folks do. The Safe Future Initiative’s emphasis on tradition, clear safety targets, ongoing coaching, and particular person efficiency targets creates accountability. Translate this by embedding safety accountability into each function and providing steady, role-based coaching.
Lesson 3: Strengthen safety governance
With SFI, integrating Deputy CISOs from key product and purposeful areas into the Governance Council has superior safety as a core a part of growth. That makes it greater than only a checkpoint, enabling earlier danger mitigation and improved resilience at scale. You’ll be able to evolve your method to governance consistent with your progress and key purposeful areas to make sure visibility and accountability. It will make it easier to speed up Zero Belief maturity and keep forward of rising cyberthreats.
Lesson 4: You’ll be able to’t defend what you may’t see
With the Safe Future Initiative, at present, greater than 99% of community gadgets are logged in a central repository for full lifecycle administration. These gadgets use centralized authentication and audit trails, are configured with Entry Management Lists (ACLs) for IPv4/v6 to limit lateral motion and have safeguards in place to forestall key compromise or abuse. Apply this by creating a list of your individual setting and implementing isolation, monitoring and safe operations.
Lesson 5: Share learnings and construct suggestions loops
The Safe Future Initiative is a residing case research—sharing progress, learnings, and greatest practices by means of experiences and blogs. You can even undertake an identical mindset: doc what works, share internally and externally (the place applicable), and constantly refine your Zero Belief journey based mostly by yourself real-world experiences.
Construct safe by design, safe by default, and safe operations
The Safe Future Initiative embeds three foundational ideas into all the pieces we do, and you may too:
- Safe by design: Incorporate risk modeling and danger assessments on the earliest planning phases.
- Safe by default: Allow guardrails and insurance policies out of the field so customers—and cyberattackers—can’t simply disable them.
- Safe operations: Repeatedly monitor, take a look at, and iterate on defenses as cyberthreats evolve.
Obtain our Safe by design: A UX toolkit to combine these checklists into your growth pipelines at the moment.
Key buyer takeaways from the April 2025 Safe Future Initiative report
You’ll be able to be taught extra concerning the progress we’ve got made bettering our safety posture within the April 2025 progress report.
Beneath are learnings from that report, and examples of how one can enhance your safety posture by making use of the Zero Belief framework and ideas.
1. Defend identities and secrets and techniques
Validate controls with assault simulations: Use crimson staff workout routines or breach-and-attack-simulation instruments to check your identification protections (multifactor authentication, conditional entry, just-in-time privilege). Determine gaps, then tune insurance policies and workflows to shut them.
2. Defend tenants and isolate manufacturing programs
Map and restrict lateral paths: Graph your setting’s belief relationships (subscriptions, useful resource teams, service connections). Pinpoint the place a cyberattacker might “hop,” then apply micro-segmentation, just-in-time community entry, or privileged identification administration to comprise any breach.
3. Defend networks
Stock, monitor, and phase: Guarantee each machine, digital machine, and repair is inventoried and sending telemetry. Lock down community flows with Zero Belief community insurance policies and micro-segmentation. Use steady monitoring to detect misconfigurations earlier than they develop into vulnerabilities.
4. Defend engineering programs
Implement safe construct pipelines: Assign clear code-ownership and combine safety gates into your steady integration/steady supply (CI/CD) pipeline. Undertake infrastructure-as-code templates with embedded guardrails and routinely remediate any drift out of your safety baseline.
5. Monitor and detect threats
Check your detection end-to-end: Usually run real looking cyberattack simulations (for instance, breach-and-attack-simulation, purple staff workout routines) throughout all clouds and on-premises environments. Validate that alerts hearth appropriately and that your safety operations middle (SOC) workflows drive well timed investigation and response.
6. Speed up response and remediation
Automate patching at scale: Implement automated working system (OS) and utility updates (Microsoft has deployed automated working system upgrades to 86% of our first-party Digital Machine Scale Units (VMSS)-based providers, leading to greater than 91 million upgrades in 2024). Shift left on vulnerability administration: combine scanning and patch-orchestration into your DevOps pipelines.
By adopting these practices, you may harden your Zero Belief posture, cut back danger, and speed up safe modernization—irrespective of the place you’re in your journey.
Further assets and motion gadgets
Get began in your Zero Belief journey: Go to the Microsoft Zero Belief webpage, entry the Zero Belief Adoption Framework within the Microsoft Zero Belief steerage middle, and obtain the self-serve Zero Belief Workshop Evaluation at the moment.
Learn the April 2025 report from the Safe Future Initiative and go to the Microsoft Safe Future Initiative web page for extra info and assets.
Speak to our consultants: Join by means of your Microsoft account staff or submit a request on the Microsoft Safety contact web page.
Work with a trusted companion: Use the Microsoft Answer Associate listing to search out specialists who will help you deploy and optimize your technique.
Be a part of the group: Get direct entry to engineers and early insights by way of the Safety Tech Neighborhood and Buyer Connection Program.
To be taught extra about Microsoft Safety options, go to our web site. Bookmark the Safety weblog to maintain up with our professional protection on safety issues. Additionally, observe us on LinkedIn (Microsoft Safety) and X (@MSFTSecurity) for the newest information and updates on cybersecurity.
1Microsoft unveils Microsoft Safety Copilot brokers and new protections for AI, March 24, 2025.

