Welcome to Tech Discuss, a weekly column concerning the issues we use and the way they work. We attempt to maintain it easy right here so everybody can perceive how and why the gadget in your hand does what it does.
Issues could turn out to be a bit of technical at instances, as that is the character of know-how — it may be complicated and complex. Collectively we are able to break all of it down and make it accessible, although!
Tech Discuss

The way it works, defined in a manner that everybody can perceive. Your weekly look into what makes your devices tick.
You may not care how any of these things occurs, and that is OK, too. Your tech devices are private and ought to be enjoyable. You by no means know although, you may simply be taught one thing…
What’s malware?

it is one thing dangerous, however do you actually know what malware is? It is in all probability not precisely what you are considering.
Malware is outlined as any software program designed to disrupt or exploit a tool, a community, or knowledge on both. Some shady bootleg app that steals your financial institution information is malware, however underneath this definition, so is Chrome or Microsoft Edge. You might want to go one step additional and describe malware as a factor that does this with out your permission.
The best strategy to describe it’s with a easy instance: a boring flashlight app. You obtain and set up a flashlight app to do just one factor: flip in your digicam flash whenever you faucet the icon. To do that, the app solely wants entry to the fundamentals — a capability to take consumer enter and ship a request to toggle the flash on and off.
Now think about the identical app, however this time it desires to entry your contacts. It does not supply any form of group entry to your digicam flash and does not have a cause for doing it. It simply does and you don’t have any thought why. That is malware. It is planning on doing one thing along with your knowledge, perhaps sooner or later, however the essential factor is that it is attempting to do issues it does not must do. Substitute some other knowledge to your contacts and the scenario is identical.
How does malware unfold?
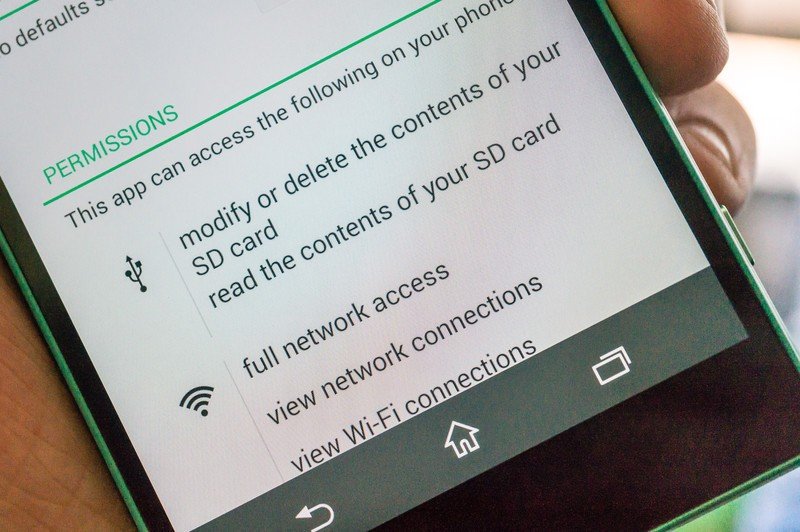
Fortunately, it is very troublesome for any utility to do what’s described above in secret. Sadly, it in all probability does not must be secretive since you by no means appeared to see what else the app tells you it’ll do down in its fantastic print.
A method malware is distributed is by counting on you to just accept all of the issues an app can do with out studying something. Nonetheless, this methodology solely works for apps that comply with the sophisticated and sometimes foolish platform distribution guidelines. And sure, that flashlight app state of affairs occurred on each Android and iOS, in every official app retailer; it adopted the principles, so it was allowed to on the time.
Social engineering (getting you to click on sure, realizing you will not learn all of it is social engineering on the lowest stage) might be the most typical strategy to unfold malware. If I can construct an app that does issues it should not, I nonetheless would want a strategy to have you ever set up it. Trickery works as a result of most individuals do not realize the hurt that may come up from their easy actions. You possibly can compromise your data, your family and friends’s data, and even the knowledge of different gadgets utilizing the identical community as you. All it’s important to do is click on sure.
A scarier manner of spreading malware is by exploiting bugs in your telephone’s OS and putting in software program with out your information. Perhaps you go to the incorrect web site, strive pirating websites for “free” paid apps, and even hook up with the incorrect open Wi-Fi community. These are methods malware can discover its manner onto your machine.
As soon as in place, this form of malware may cause severe points. Governments of the world even strive it, so it could actually monitor the individuals they assume must be monitored as a result of it is highly effective and normally undetectable.
What can I do to try to forestall all this?

Fortunately, it isn’t that troublesome to guard your self. You may set up one of many many malware scanners obtainable and hope it catches any and every part, however you additionally must comply with just a few easy guidelines should you simply need issues to be simple and malware-free.
Solely use the official app retailer that got here along with your telephone. Your telephone comes with at the least one strategy to discover and set up apps to do enjoyable and funky issues with. These shops aren’t good, however they’re one million instances higher at catching and eradicating malware earlier than it could actually get to you than some other distribution mannequin. Apple exams each app earlier than it is positioned within the retailer, whereas Google makes positive the app follows the principles earlier than it is made obtainable, after which scans each app earlier than it will get put in in your telephone. Samsung, Epic, and different app markets even have safeguards in place to ensure they don’t seem to be spreading dangerous apps.
By no means click on sure earlier than you learn what you are agreeing with. This cannot be pressured sufficient! These consumer agreements are horrible and sometimes stuffed with language designed to present one get together a bonus within the case of a dispute however power your self to learn by way of them each single time. You may not like your choices; you may both must comply with the phrases introduced or not use an app, a service, or perhaps a machine itself. No person desires to place their Galaxy S25 again within the field to ship to Samsung as a result of they do not need Samsung to research the best way they use it, however these are the principles. As soon as you’ve got mentioned sure, they will and can do what they requested permission to do. Be sure to’re OK with all of it by studying what’s put in entrance of you. (Editor’s notice: You possibly can belief firms like Samsung, Apple, and even Google to do solely what they are saying they may do with something they acquire out of your telephone, so do not let that scare you off.)

All the time settle for updates. Once you purchase a tool you are given a promise of software program help for a selected period of time. An enormous a part of that help is patching the bugs and exploits used to hijack your telephone or set up dangerous apps with out your information. Belief that firms like Google and Apple know what they’re doing but in addition settle for that different sensible persons are looking for methods to defeat each safety you may have. Exploits will occur and when these get patched, you’ll want to set up the replace instantly.
By no means belief something with out verifying it first. That is the toughest half. Is that message actually out of your little brother asking for $200 or saying he forgot the gate code or is it from another person? Be sure that. The identical goes for any hyperlinks you come throughout — are you positive you possibly can belief them? Be very cautious utilizing public Wi-Fi networks, too. It is simple to make one (you possibly can do it proper in your telephone!) and with the correct instruments every part despatched on them could be collected: passwords, 2FA data, bank card information, and so forth. Taking a minute to be sure you know the who and what is so much simpler than attempting to repair every part after somebody steals your id or your bank card quantity.
Actually, it isn’t as laborious because it sounds to guard your self. It is also not foolproof — anybody can find yourself with malware, even safety professionals or authorities officers with safety groups. Doing all your half makes it so much more durable.

