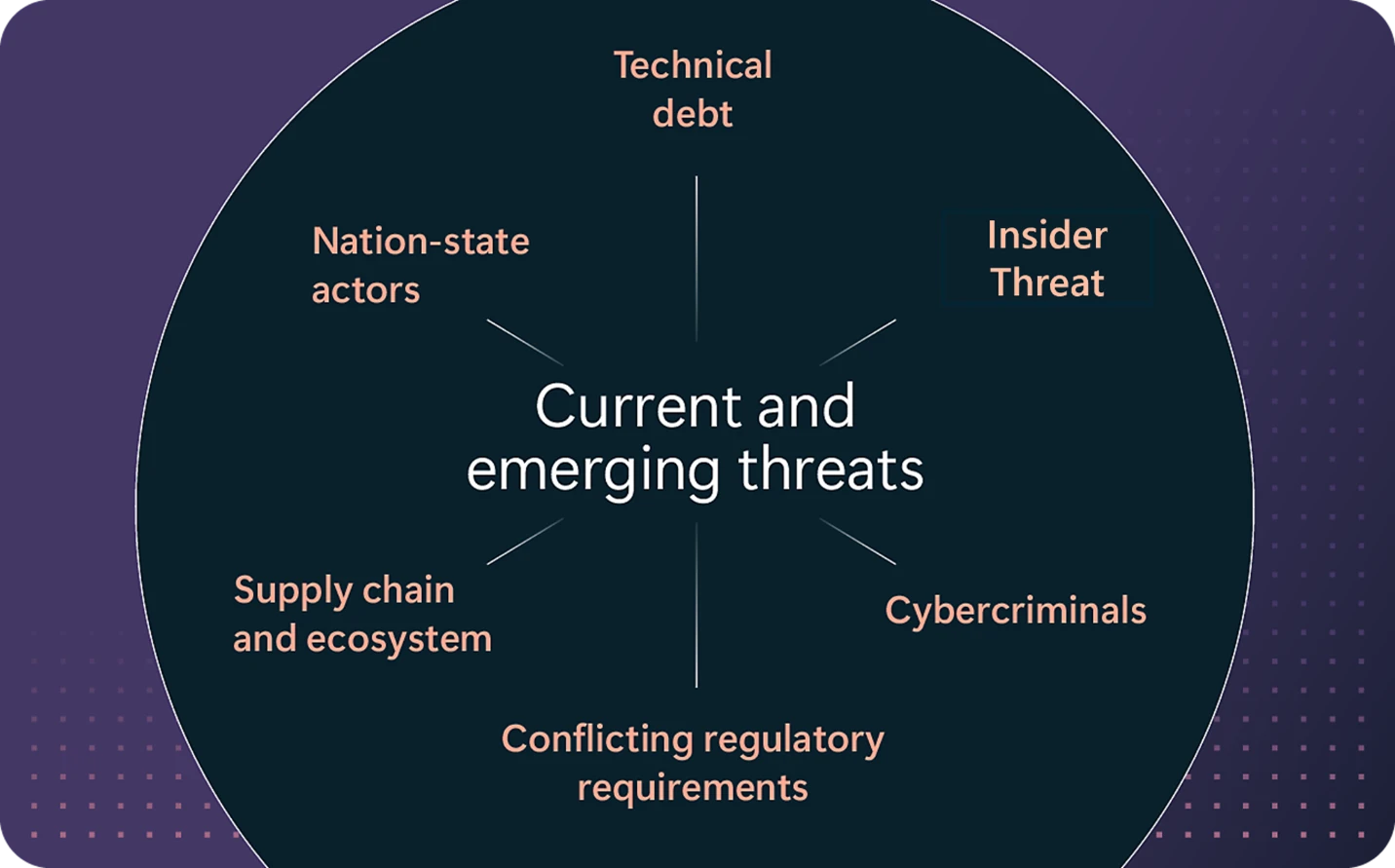
Cybersecurity is among the high dangers dealing with companies. Organizations are struggling to navigate the ever-evolving cyberthreat panorama through which 600 million identification assaults are carried out day by day.1 The median time for a cyberattacker to entry non-public knowledge from phishing is 1 hour and 12 minutes, and nation-state cyberattacks are on the rise.2 Organizations additionally face unprecedented complexity, making safety jobs tougher—57% of organizations are utilizing greater than 40 safety instruments, which requires vital resourcing and energy to combine workflows and knowledge.3 These challenges are magnified by the worldwide safety expertise scarcity organizations are dealing with and there are greater than 4 million safety jobs unfilled worldwide, rising insider dangers, and the quickly evolving regulatory panorama at the moment.4 These cybersecurity challenges can’t solely enhance vital enterprise disruptions, they will additionally create devastating financial damages—the price of cybercrime is predicted to develop at 15% yr over yr, reaching $15.6 trillion by 2029.5
In November 2023, to handle the evolution of the digital and regulatory panorama, and the unprecedented adjustments within the cyberthreat panorama, we introduced the Microsoft Safe Future Initiative. The Safe Future Initiative (SFI) is a multiyear effort to revolutionize the way in which we design, construct, check, and function our services and products, to attain the best safety requirements. SFI is our dedication to enhance Microsoft’s safety posture, thereby enhancing the safety posture of all our clients, and to work with governments and business to enhance the safety posture of your entire ecosystem.
Final yr, the Cybersecurity and Infrastructure Safety Company (CISA), by way of its “Safe by Design” pledge, referred to as on the know-how business to prioritize safety at each stage of product improvement and deployment. This method of embedding cybersecurity in digital supply from the outset can be mirrored in the UK’s Authorities’s Cyber Safety Technique in addition to within the Australian Cyber Safety Centre (ACSC)’s “Important Eight” mitigation methods to guard towards cyberthreats. All through this weblog submit, the time period “Safe by Design” encompasses each “safe by design” and “safe by default.”
Microsoft dedicated to work in the direction of key targets throughout a spectrum of Safe by Design ideas advocated by quite a few authorities companies all over the world. These targets goal to boost safety outcomes for purchasers by embedding sturdy cybersecurity practices all through the product lifecycle. We proceed to take our learnings, feed them again into our safety requirements, and operationalize these learnings as paved paths that may allow safe design and operations at scale. Our SFI updates present examples of Microsoft’s progress in implementing safe by design, safe by default, and safe in operations ideas, and supply greatest practices based mostly on Microsoft’s personal expertise, demonstrating our dedication to enhancing safety for purchasers.
Preserve studying to be taught concerning the initiatives Microsoft has undertaken over the previous 18 months to assist safe by design aims as a part of our SFI initiative. It’s organized round our SFI ideas to offer our clients and companions with an understanding of the sturdy safety measures we’re implementing to safeguard their digital environments.
Enhancing safety with multifactor authentication and default password administration
Phishing-resistant multifactor authentication supplies essentially the most sturdy protection towards password-based cyberattacks, together with credential stuffing and password theft. This consists of selling multifactor authentication amongst clients, implementing it as a default requirement for entry, and collaborating in efforts to ascertain long-term requirements in authentication.
In October 2024, Microsoft applied necessary multifactor authentication for the Microsoft Azure portal, Microsoft Entra admin middle, and Microsoft Intune admin middle. Since then, Microsoft has labored with our clients to scale back extensions and quickly advance multifactor authentication adoption. A key achievement is our progress in eliminating passwords throughout merchandise. Microsoft has launched enhancements to streamline authentication and enhance sign-in experiences, emphasizing usability and safety. Customers can now take away passwords from their accounts and use passkeys as a substitute, addressing vulnerabilities and stopping unauthorized entry.
On March 26, 2025, Microsoft launched a brand new sign-in expertise for greater than 1 billion customers. By the tip of April 2025, most Microsoft account customers will see up to date sign-in and sign-up consumer expertise flows for net and cell apps. This new consumer expertise is optimized for a passwordless and passkey-first expertise. Microsoft can be updating the account sign-in logic to make passkey the default sign-in selection at any time when doable.
Extra examples of Microsoft enhancing authentication and the way clients can be taught from Microsoft’s method and options embody:
- Microsoft suggestions for organizations to get began deploying phishing-resistant passwordless authentication utilizing Microsoft Entra ID.
- Safety defaults make it simpler to assist shield towards identity-related cyberattacks like password spray, replay, and phishing frequent in at the moment’s environments. Study extra about preconfigured safety settings accessible in Microsoft Entra ID.
- Microsoft’s Conditional Entry makes use of identity-driven indicators as a part of entry management choices.
- To assist stop phishing, Microsoft added extra hardening to Home windows Hiya, which is the multifactor authentication answer built-in to Home windows. Home windows Hiya has additionally been prolonged to assist passkeys, that are an business customary, and which we proceed to evolve. With Hiya and passkeys, on Home windows, it means a lot of the net could be protected with multifactor authentication, and folks now not want to decide on between a easy sign-in and a protected sign-in.
- Find out how Microsoft is advancing decentralized identification requirements and verifiable credentials.
- Following GitHub’s April 2024 replace on a yr of progress in pushing multifactor authentication adoption, additional cohorts requiring multifactor authentication enablement have been rolled out previously yr. This effort continues to drive multifactor authentication utilization with virtually 50% of contributing GitHub customers having multifactor authentication enabled. Of these, greater than 38% of customers have two or extra strategies of two-factor authentication enabled and greater than 3.6 million customers have a passkey enabled on their account. Moreover, GitHub has pushed for greatest practices in multifactor authentication strategies, and in November 2024 shipped enhancements to the administration of multifactor authentication settings for organizations and enterprises that enable the restriction of insecure strategies of multifactor authentication resembling textual content messaging.
Decreasing total courses of vulnerabilities
Most exploited vulnerabilities at the moment stem from sorts that may usually be mitigated on a big scale, resembling SQL injection, cross-site scripting, and reminiscence security language vulnerabilities. Governments goal to scale back these by encouraging firms to undertake practices like eliminating authorization validation logic errors, enabling using memory-safe languages, creating safe firmware architectures, and implementing safe administrative protections. The objective is to attenuate exploitation dangers by addressing systemic vulnerabilities at their root.
Our introduction of necessary use of the Microsoft Authentication Library (MSAL) throughout all Microsoft functions helps make sure that superior identification defenses, resembling token binding, steady entry analysis, and superior utility assault detections, are constantly applied. This standardizes safe authentication processes, making it considerably tougher for attackers to take advantage of identity-related vulnerabilities. MSAL permits builders to amass safety tokens from the Microsoft identification platform to authenticate customers and entry secured net APIs.
Microsoft can be dedicated to adopting memory-safe languages, resembling Rust, for creating new merchandise and transitioning present ones. This method addresses frequent vulnerabilities associated to reminiscence security. Microsoft is investing closely into protected language to boost the protection of our code, and we’re making use of this new method to our safety platform and different key areas like Microsoft Floor and Pluton safety firmware.
In Home windows 11, we’ve utilized a safe by design technique from the very first line of code. We have now established a {Hardware} Safety Baseline, which helps to make sure each Home windows 11 PC has constant {hardware} safety forming a safe basis. Home windows 11 has safe by default settings and stronger controls for what apps and drivers are allowed to run. That is essential as unverified apps and drivers result in malware and script assaults. And most malware and ransomware apps are unsigned, which suggests they are often authored and distributed with out being provably protected. For shoppers and smaller organizations, Sensible App Management is a brand new function that makes use of cloud AI to allow thousands and thousands of identified protected apps to run, no matter the place you bought them. For bigger organizations, IT admins can layer on App Management for Enterprise insurance policies and deploy them utilizing Intune.
With Home windows powering enterprise important options throughout all kinds of shoppers, we’re dedicated to serving to make sure that Home windows stays essentially the most safe and dependable platform. At Microsoft Ignite in 2024, we introduced the Home windows Resilience Initiative centered on enhancing the safety and resilience of the Home windows working system. This includes implementing superior safety features, enhancing risk detection and response capabilities, and to assist make sure that Home windows can face up to and recuperate from cyberattacks. As a part of the Home windows Resilience Initiative, we’re working to guard towards frequent cyberattacks along with strengthening identification safety talked about above.
As a part of this we’re addressing the long-standing problem of overprivileged customers and functions, which create vital threat. But many individuals don’t need to surrender admin management of their PC. To assist strike the steadiness of admin privileges and safety we’re introducing Administrator safety (presently in Home windows Insiders). Admin safety provides you the safety of normal consumer permissions by default, and when wanted you’ll be able to securely authorize a just-in-time system change utilizing Home windows Hiya. As soon as the method has accomplished, the momentary admin token is destroyed. This implies admin privileges don’t persist. Admin safety shall be disruptive to cyberattackers, as they now not have elevated privileges by default, which is able to assist organizations guarantee they continue to be answerable for Home windows.
We’re additionally collaborating with endpoint safety companions to undertake protected deployment practices. This implies all safety product updates shall be gradual, minimizing deployment dangers and monitoring to assist guarantee any detrimental impression is stored to a minimal. Moreover, we’re creating new Home windows capabilities that enable safety product builders to construct their merchandise outdoors of kernel mode, decreasing the impression to Home windows within the occasion of a safety product crash.
One other key improvement is our safe by design consumer expertise (UX) toolkit. Human error causes the vast majority of safety breaches. The UX toolkit helps construct safer software program and enhance consumer safety experiences. This toolkit represents a brand new mind-set—the place design and safety aren’t siloed however are working collectively from the very starting. Adopted internally and shared externally, the toolkit helps different software program organizations in enhancing their safety practices.
Different actions Microsoft has labored on to get rid of courses of vulnerabilities embody:
- Continued assist to allow builders to make use of the reminiscence protected language Rust on Home windows.
- Taking steps to mitigate Home windows NT LAN (NTLM) Relay Assaults by default towards Alternate Service, Energetic Listing Certificates Providers and Light-weight Listing Entry Protocol (LDAP).
- Zero Belief Area Title System (DNS) preview expanded to incorporate Home windows 11 enterprise clients. This function helps lock down units to solely access-approved community locations.
- Floor embedded firmware merchandise use of a frequent firmware structure.
- Launch of the Home windows 365 Hyperlink, which is the primary Cloud PC gadget for Home windows 365. Home windows 365 Hyperlink eliminates native knowledge and apps and has no native admin customers and supplies workers a solution to extra securely stream their Home windows 365 Cloud PC.
- GitHub launched CodeQL assist for GitHub Actions workflow recordsdata. This new static evaluation functionality identifies frequent steady integration and steady supply (CI/CD) flaws each in present code bases and earlier than they’re launched to assist get rid of this class of vulnerabilities. Utilizing this new function, the GitHub Safety Lab was capable of assist safe greater than 75 GitHub Actions workflows in open supply initiatives, disclosing greater than 90 completely different vulnerabilities.
Boosting patch utility charges
Well timed and efficient patch administration is critical for cybersecurity, as that is how we will scale back the window of alternative for malicious actors to take advantage of software program flaws.
Microsoft has made measurable will increase within the set up of safety patches, which we achieved by enabling computerized set up of software program patches when doable and enabling this performance by default, in addition to by providing widespread assist for these patches.
Microsoft continues to roll out main safety updates on the second Tuesday of every month, referred to as Patch Tuesday. This common schedule ensures that each one techniques obtain well timed updates to handle important vulnerabilities, thereby decreasing the chance of exploitation by cyberattackers.
Constructing on this basis, Microsoft has made vital strides in enhancing the replace course of with Home windows 11. By decreasing the variety of required system restarts from 12 to 4 per yr by way of using Hotpatch updates, now we have additional streamlined operations and inspired organizations to stay compliant with patching necessities.
Different examples of our efforts in to spice up patch and safety replace charges embody:
- Home windows Hotpatch: Introduced at Microsoft Ignite 2024, this supplies a 60% discount in time to undertake safety updates, assisted by making use of updates seamlessly with out system restarts.
- Microsoft has emphasised the significance of clearly speaking the anticipated lifespan of merchandise on the time of sale and investing in provisioning capabilities to ease buyer transitions to supported variations when merchandise attain the tip of their lifecycle. This technique ensures that clients are well-informed and may easily adapt to new applied sciences.
Adopting a Vulnerability Disclosure Coverage (VDP) and Frequent Vulnerabilities and Exposures (CVE)
Coordinated vulnerability disclosure, a apply Microsoft adopted greater than a decade in the past, advantages each safety researchers and software program producers by enabling collaboration to boost product safety. A VDP that authorizes public testing of merchandise, commits to refraining from authorized motion towards those that comply with the VDP in good religion, supplies a transparent channel for reporting vulnerabilities, and permits public disclosure of vulnerabilities in keeping with coordinated vulnerability disclosure greatest practices and worldwide requirements makes an actual distinction for cybersecurity. Moreover, producers can exhibit transparency by together with correct Frequent Weak spot Enumeration (CWE) and Frequent Platform Enumeration (CPE) fields in each CVE document for the producer’s merchandise.
Our adoption of the CWE and CPE requirements in each CVE document for its merchandise is a vital achievement. This transparency facilitates correct and detailed details about vulnerabilities, facilitating well timed and efficient remediation. By issuing CVEs promptly for all important or high-impact vulnerabilities, Microsoft demonstrates its dedication to sustaining a safe surroundings and defending its clients from potential cyberthreats.
One other notable spotlight is the publication of a machine-readable CSAF recordsdata, which offer a transparent channel for reporting vulnerabilities and authorizes public testing of Microsoft merchandise. This fosters collaboration between safety researchers and software program producers, enabling the identification and mitigation of vulnerabilities in a coordinated method.
Different actions Microsoft has labored on to undertake VDP and CVE embody:
Empowering clients to detect and doc intrusions
Organizations ought to do extra to detect cybersecurity incidents and perceive their impression. To make sure they will do this, producers ought to present artifacts and evidence-gathering instruments, like audit logs.
An instance of Microsoft’s dedication on this space is our implementation of sturdy sensors and logs, enhancing detection of cyberthreats. This initiative supplies clients with actionable insights into potential intrusions, enabling swift responses and threat mitigation.
Different actions Microsoft has labored on to empower clients to detect and doc inclusions embody:
- Microsoft Purview has expanded its audit logging and retention durations, amongst different safety enhancements, to extend safety visibility and incident response capabilities for cloud-based providers.
- Microsoft Safety Copilot gives prebuilt promptbooks to automate security-related duties, resembling incident investigations, consumer evaluation, and risk intelligence assessments, enhancing effectivity and accuracy in cybersecurity operations.
- Microsoft has offered detailed steerage on implementing the United States Division of Protection (DoD) Zero Belief Technique, with actions categorized into goal and superior phases to attain full Zero Belief adoption by 2032.
- Microsoft’s Expanded Cloud Logs Implementation Playbook supplies detailed steerage on operationalizing new logging capabilities in Microsoft Purview Audit (Commonplace).
- Microsoft has revealed a whitepaper on classes discovered from purple teaming greater than 100 generative AI merchandise at Microsoft. The whitepaper highlights the significance of understanding AI techniques, breaking them with out computing gradients, and the need of human involvement in AI purple teaming, amongst different matters.
GitHub shipped enhanced capabilities to the GitHub audit log to offer clients with elevated visibility of API occasions and options to allow enterprise administration, automation, and integration.
To be taught extra about Microsoft Safety options, go to our web site. Bookmark the Safety weblog to maintain up with our knowledgeable protection on safety issues. Additionally, comply with us on LinkedIn (Microsoft Safety) and X (@MSFTSecurity) for the most recent information and updates on cybersecurity.
1Microsoft Digital Protection Report 2024.
2Microsoft Digital Protection Report 2022.
3IDC North America Instruments and Distributors Consolidation Survey, 2023.

