This yr at CYBERWARCON, Microsoft Risk Intelligence analysts are sharing analysis and insights representing years of menace actor monitoring, infrastructure monitoring and disruption, and attacker tooling.
The speak DPRK – All grown up will cowl how the Democratic Individuals’s Republic of Korea (DPRK) has efficiently constructed laptop community exploitation functionality over the previous 10 years and the way menace actors have enabled North Korea to steal billions of {dollars} in cryptocurrency in addition to goal organizations related to satellites and weapons programs. Over this era, North Korean menace actors have developed and used a number of zero-day exploits and have grow to be specialists in cryptocurrency, blockchain, and AI expertise.
This presentation can even embody data on North Korea overcoming sanctions and different monetary obstacles by america and a number of different nations by the deployment of North Korean IT employees in Russia, China, and, different nations. These IT employees masquerade as people from nations apart from North Korea to carry out authentic IT work and generate income for the regime. North Korean menace actors’ focus areas are:
- Stealing cash or cryptocurrency to assist fund the North Korea weapons packages
- Stealing data pertaining to weapons programs, sanctions data, and policy-related choices earlier than they happen
- Performing IT work to generate income to assist fund the North Korea IT weapons program
In the meantime, within the speak No targets left behind, Microsoft Risk Intelligence analysts will current analysis on Storm-2077, a Chinese language menace actor that conducts intelligence assortment concentrating on authorities businesses and non-governmental organizations. This presentation will hint how Microsoft assembled the items of menace exercise now tracked as Storm-2077 to reveal how we overcome challenges in monitoring overlapping actions and attributing cyber operations originating from China.
This weblog summarizes intelligence on menace actors coated by the 2 Microsoft displays at CYBERWARCON.
Sapphire Sleet: Social engineering resulting in cryptocurrency theft
The North Korean menace actor that Microsoft tracks as Sapphire Sleet has been conducting cryptocurrency theft in addition to laptop community exploitation actions since at the least 2020. Microsoft’s evaluation of Sapphire Sleet exercise signifies that over 10 million US {dollars}’ price of cryptocurrency was stolen by the menace actor from a number of firms over a six-month interval.
Masquerading as a enterprise capitalist
Whereas their strategies have modified all through the years, the first scheme utilized by Sapphire Sleet over the previous yr and a half is to masquerade as a enterprise capitalist, feigning curiosity in investing within the goal consumer’s firm. The menace actor units up a web based assembly with a goal consumer. On the day of the assembly, when the goal consumer makes an attempt to connect with the assembly, the consumer receives both a frozen display screen or an error message stating that the consumer ought to contact the room administrator or assist crew for help.
When the goal contacts the menace actor, the menace actor sends a script – a .scpt file (Mac) or a Visible Fundamental Script (.vbs) file (Home windows) – to “repair the connection concern”. This script results in malware being downloaded onto the goal consumer’s gadget. The menace actor then works in direction of acquiring cryptocurrency wallets and different credentials on the compromised gadget, enabling the menace actor to steal cryptocurrency.
Posing as recruiters
As a secondary technique, Sapphire Sleet masquerades as a recruiter on skilled platforms like LinkedIn and reaches out to potential victims. The menace actor, posing as a recruiter, tells the goal consumer that they’ve a job they’re attempting to fill and imagine that the consumer could be a great candidate. To validate the talents listed on the goal consumer’s profile, the menace actor asks the consumer to finish a abilities evaluation from a web site underneath the menace actor’s management. The menace actor sends the goal consumer a sign-in account and password. In signing in to the web site and downloading the code related to the talents evaluation, the goal consumer downloads malware onto their gadget, permitting the attackers to realize entry to the system.
Ruby Sleet, a menace actor that Microsoft has been monitoring since 2020, has considerably elevated the sophistication of their phishing operations over the previous a number of years. The menace actor has been noticed signing their malware with authentic (however compromised) certificates obtained from victims they’ve compromised. The menace actor has additionally distributed backdoored digital non-public community (VPN) shoppers, installers, and varied different authentic software program.
Ruby Sleet has additionally been noticed conducting analysis on targets to search out what particular software program they run of their atmosphere. The menace actor has developed customized capabilities tailor-made to particular targets. For instance, in December 2023, Microsoft Risk Intelligence noticed Ruby Sleet finishing up a provide chain assault by which the menace actor efficiently compromised a Korean development firm and changed a authentic model of VeraPort software program with a model that communicates with identified Ruby Sleet infrastructure.
Ruby Sleet has focused and efficiently compromised aerospace and protection-related organizations. Stealing aerospace and defense-related expertise could also be utilized by North Korea to extend its understanding of missiles, drones, and different associated applied sciences.
North Korean IT employees: The triple menace
Along with using laptop community exploitation by the years, North Korea has dispatched hundreds of IT employees overseas to earn cash for the regime. These IT employees have introduced in tons of of thousands and thousands of {dollars} for North Korea. We contemplate these North Korean IT employees to be a triple menace, as a result of they:
- Make cash for the regime by performing “authentic” IT work
- Might use their entry to acquire delicate mental property, supply code, or commerce secrets and techniques on the firm
- Steal delicate information from the corporate and in some circumstances ransom the corporate into paying them in alternate for not publicly disclosing the corporate’s information
Microsoft Risk Intelligence has noticed North Korean IT employees working out of North Korea, Russia, and China.
Facilitators complicate monitoring of IT employee ecosystem
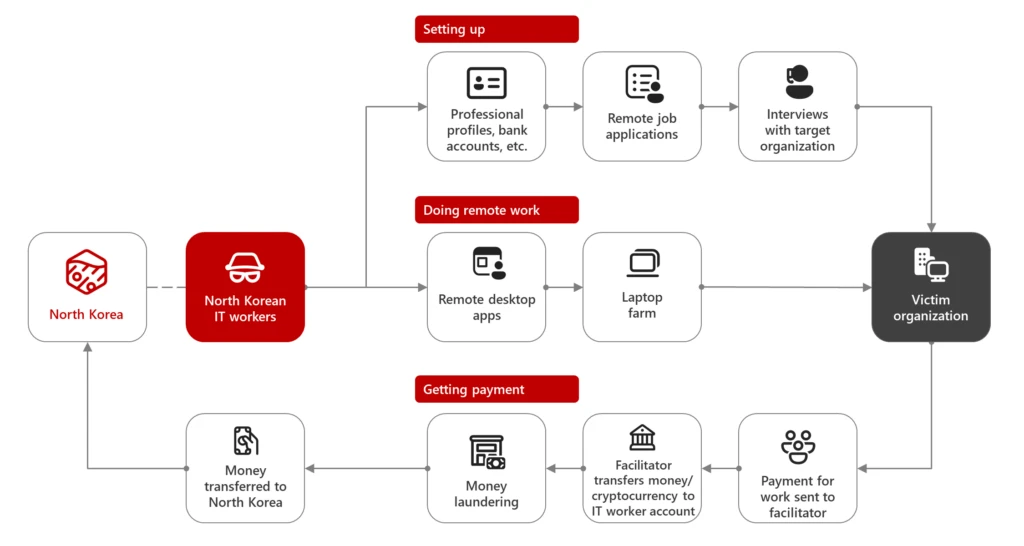
Microsoft Risk Intelligence noticed that the actions of North Korean IT employees concerned many alternative events, from creating accounts on varied platforms to accepting funds and transferring cash to North Korean IT worker-controlled accounts. This makes monitoring their actions tougher than conventional nation-state menace actors.
Because it’s tough for an individual in North Korea to enroll in issues reminiscent of a checking account or telephone quantity, the IT employees should make the most of facilitators to assist them purchase entry to platforms the place they will apply for distant jobs. These facilitators are utilized by the IT employees for duties reminiscent of creating an account on a contract job web site. As the connection builds, the IT employees might ask the facilitator to carry out different duties reminiscent of:
- Creating or renting their checking account to the North Korean IT employee
- Creating LinkedIn accounts for use for contacting recruiters to acquire work
- Buying cell phone numbers or SIM playing cards
- Creating further accounts on freelance job websites
Faux profiles and portfolios with the help of AI
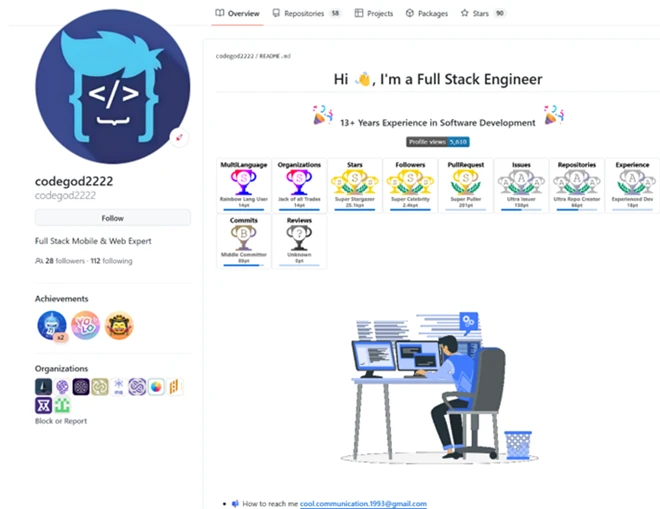
One of many first issues a North Korean IT employee does is ready up a portfolio to indicate supposed examples of their earlier work. Microsoft Risk Intelligence has noticed tons of of faux profiles and portfolios for North Korean IT employees on developer platforms like GitHub.
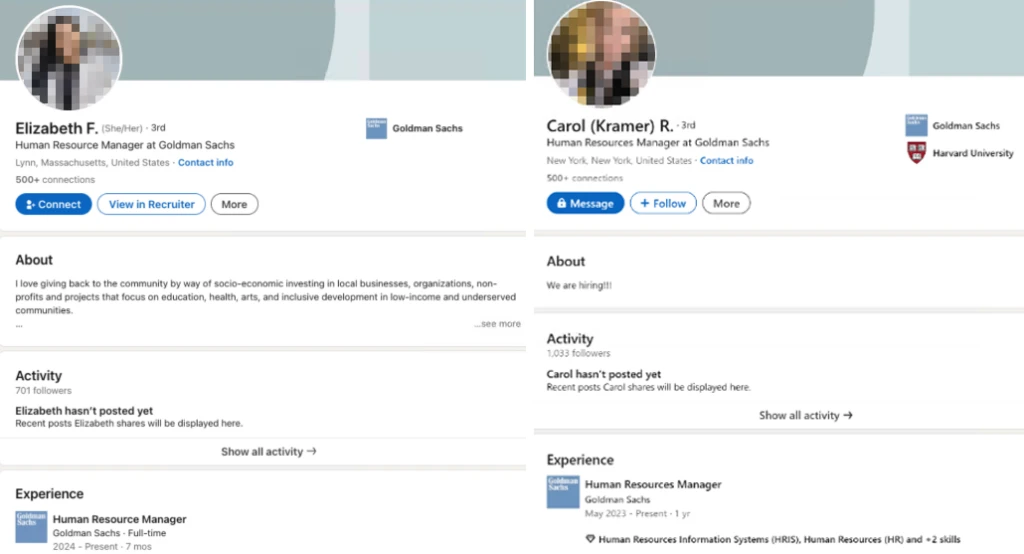
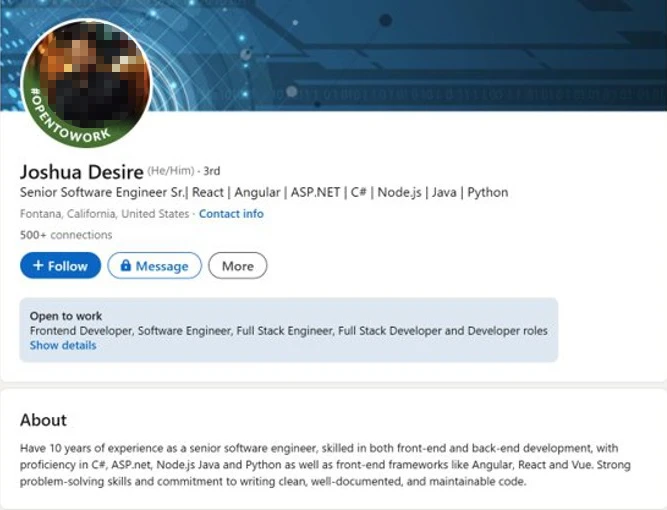
Moreover, the North Korean IT employees have used pretend profiles on LinkedIn to speak with recruiters and apply for jobs.
In October 2024, Microsoft discovered a public repository containing North Korean IT employee information. The repository contained the next data:
- Resumes and e mail accounts utilized by the North Korean IT employees
- Infrastructure utilized by these employees (VPS and VPN accounts together with particular VPS IP addresses)
- Playbooks on conducting id theft and creating and bidding jobs on freelancer web sites with out getting flagged
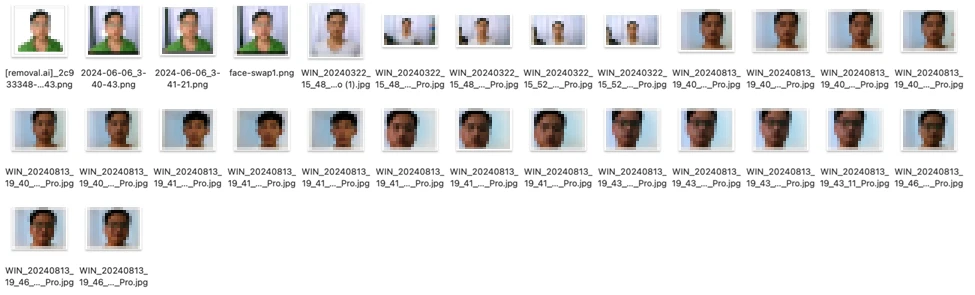
- Precise photos and AI-enhanced photos of suspected North Korean IT employees
- Pockets data and suspected funds made to facilitators
- LinkedIn, GitHub, Upwork, TeamViewer, Telegram, and Skype accounts
- Monitoring sheet of labor carried out and funds acquired by these IT employees
Evaluate of the repository signifies that the North Korean IT employees are conducting id theft and utilizing AI instruments reminiscent of Faceswap to maneuver their image over to paperwork that they’ve stolen from victims. The attackers are additionally utilizing Faceswap to take footage of the North Korean IT employees and transfer them to extra skilled wanting settings. The photographs created by the North Korean IT employees utilizing AI instruments are then utilized on resumes or profiles, generally for a number of personas, which might be submitted for job purposes.

In the identical repository, Microsoft Risk Intelligence discovered photographs that seem like of North Korean IT employees:
Microsoft has noticed that, along with utilizing AI to help with creating photos used with job purposes, North Korean IT employees are experimenting with different AI applied sciences reminiscent of voice-changing software program. This aligns with observations shared in earlier blogs displaying menace actors utilizing AI as a productiveness device to refine their assault strategies. Whereas we don’t see menace actors utilizing mixed AI voice and video merchandise as a tactic, we do acknowledge that if actors have been to mix these applied sciences, it’s attainable that future campaigns might contain IT employees utilizing these packages to aim to trick interviewers into pondering they aren’t speaking with a North Korean IT employee. If profitable, this might permit the North Korean IT employees to do interviews instantly and never should depend on facilitators acquiring work for them by standing in on interviews or promoting account entry to them.
Getting fee for distant work
The North Korean IT employees seem like very organized in the case of monitoring funds acquired. General, this group of North Korean IT employees seems to have made at the least 370,000 US {dollars} by their efforts.
Defending organizations from North Korean IT employees
Sadly, laptop community exploitation and use of IT employees is a low-risk, high-reward approach utilized by North Korean menace actors. Listed below are some steps that organizations can take to be higher protected:
- Comply with steerage from the US Division of State, US Division of the Treasury, and the Federal Bureau of Investigation on tips on how to spot North Korean IT employees.
- Educate human sources managers, hiring managers, and program managers for indicators to search for when coping with suspected North Korean IT employees.
- Use easy non-technical strategies reminiscent of asking IT employees to activate their digicam periodically and evaluating the individual on digicam with the one which picked up the laptop computer out of your group.
- Ask the individual on digicam to stroll by or clarify code that they purportedly wrote.
Storm-2077: No targets left behind
Over the previous decade, following quite a few authorities indictments and the general public disclosure of menace actors’ actions, monitoring and attributing cyber operations originating from China has grow to be more and more difficult because the attackers regulate their techniques. These menace actors proceed to conduct operations whereas utilizing tooling and strategies towards targets that usually overlap with one other menace actor’s operation. Whereas analyzing exercise that was affecting a handful of consumers, Microsoft Risk Intelligence assembled the items of what could be tracked as Storm-2077. Undoubtably, this actor had some victimology and operational strategies that overlapped with a few menace actors that Microsoft was already monitoring.
Microsoft assesses that Storm-2077 is a China state menace actor that has been lively since at the least January 2024. Storm-2077 has focused all kinds of sectors, together with authorities businesses and non-governmental organizations in america. As we continued to trace Storm-2077, we noticed that they went after a number of different industries worldwide, together with the Protection Industrial Base (DIB), aviation, telecommunications, and monetary and authorized providers. Storm-2077 overlaps with exercise tracked by different safety distributors as TAG-100.
We assess that Storm-2077 doubtless operates with the target of conducting intelligence assortment. Storm-2077 has used phishing emails to realize credentials and, in sure circumstances, doubtless exploited edge-facing units to realize preliminary entry. We now have noticed strategies that target e mail information theft, which may permit them to research the info later with out risking speedy lack of entry. In some circumstances, Storm-2077 has used legitimate credentials harvested from the profitable compromise of a system.
We’ve additionally noticed Storm-2077 efficiently exfiltrate emails by stealing credentials to entry authentic cloud purposes reminiscent of eDiscovery purposes. In different circumstances, Storm-2077 has been noticed having access to cloud environments by harvesting credentials from compromised endpoints. As soon as administrative entry was gained, Storm-2077 created their very own software with mail learn rights.
Entry to e mail information is essential for menace actors as a result of it typically accommodates delicate data that might be utilized later for malicious functions. Emails can embody sign-in credentials, confidential communication, monetary data, enterprise secrets and techniques, mental property, and credentials for accessing crucial programs, or worker data. Entry to e mail accounts and the flexibility to steal e mail communication may allow an attacker to additional their operations.
Microsoft’s speak on Storm-2077 at CYBERWARCON will spotlight how huge their concentrating on curiosity covers. All sectors seem like on the desk, leaving no targets behind. Our analysts will speak concerning the challenges of monitoring China-based menace actors and the way they needed to distinctly carve out Storm-2077.
CYBERWARCON Recap
At this yr’s CYBERWARCON, Microsoft Safety is sponsoring the post-event Fireplace Recap. Hosted by Sherrod DeGrippo, this session will characteristic particular company who will dive into the highlights, key insights, and rising themes that outlined CYBERWARCON 2024. Interviews with audio system will provide unique insights and produce the convention’s largest moments into sharp focus.
Be taught extra
For the most recent safety analysis from the Microsoft Risk Intelligence neighborhood, take a look at the Microsoft Risk Intelligence Weblog: https://aka.ms/threatintelblog.
To get notified about new publications and to affix discussions on social media, observe us on LinkedIn at https://www.linkedin.com/showcase/microsoft-threat-intelligence, and on X (previously Twitter) at https://twitter.com/MsftSecIntel.
To listen to tales and insights from the Microsoft Risk Intelligence neighborhood concerning the ever-evolving menace panorama, hearken to the Microsoft Risk Intelligence podcast: https://thecyberwire.com/podcasts/microsoft-threat-intelligence.

